What Is a Dusting Attack and What Are Its Characteristics?
2026/04/05 00:16:33
A dusting attack is not a direct theft mechanism but a sophisticated privacy exploitation technique that leverages blockchain transparency to trace, cluster, and ultimately de-anonymize cryptocurrency users, turning seemingly insignificant transactions into powerful intelligence tools for targeted cyber threats.
A Quiet Threat Hidden in Plain Sight
A dusting attack rarely announces itself. It arrives as a tiny, almost meaningless transaction, sometimes just a few cents’ worth of cryptocurrency, quietly sitting in a wallet without raising suspicion. Yet beneath that insignificant value lies a calculated strategy designed to expose something far more valuable: identity. In the cryptocurrency ecosystem, where privacy is often assumed but not guaranteed, these micro-transactions have become a subtle method of surveillance. According to various explanations of dusting attacks, attackers distribute small amounts of crypto to many addresses specifically to track and analyze how those funds move across the blockchain.
This approach works because blockchain networks are transparent by design. Every transaction is publicly recorded, creating a permanent and traceable ledger. While wallet addresses do not directly reveal personal identities, patterns emerge over time. A dusting attack exploits this transparency, using data rather than force to uncover connections between wallets. Unlike hacking attempts that target vulnerabilities in software, dusting attacks focus on behavioral patterns. They turn routine transactions into breadcrumbs, gradually revealing ownership structures.
What makes this threat particularly interesting is its invisibility. Many users never notice these deposits, and even fewer understand their purpose. The attack does not demand action, does not trigger alarms, and does not attempt to steal funds immediately. Instead, it waits. This patience is what makes dusting attacks so effective, and so underestimated.
Understanding “Dust” in Cryptocurrency Context
To understand a dusting attack, it is essential to first understand what “dust” actually means. In cryptocurrency, dust refers to extremely small amounts of digital assets, often so tiny that they are practically useless for spending. For example, on the Bitcoin network, dust can be just a few hundred satoshis, a fraction of a cent in value.
These amounts exist naturally within blockchain systems. Over time, repeated transactions can leave behind small fragments of cryptocurrency, known as unspent transaction outputs (UTXOs). These fragments accumulate and are often ignored by users because they hold negligible financial value. However, what appears insignificant financially can be highly valuable from a data perspective.
Attackers take advantage of this by deliberately sending dust to thousands of wallets. Because blockchain networks allow anyone to send funds to any public address, there is no barrier preventing this action. Once the dust enters a wallet, it becomes part of that wallet’s transaction history. This is where the real strategy begins.
Dust acts as a marker. It is not meant to be spent for profit but to serve as a tracking tool. When a user unknowingly includes that dust in a future transaction, it links different wallet addresses together. Over time, these connections form a map of ownership.
In this sense, dust is less about money and more about metadata. It transforms the blockchain from a financial ledger into an intelligence network, where even the smallest transaction can reveal patterns about behavior, habits, and identity.
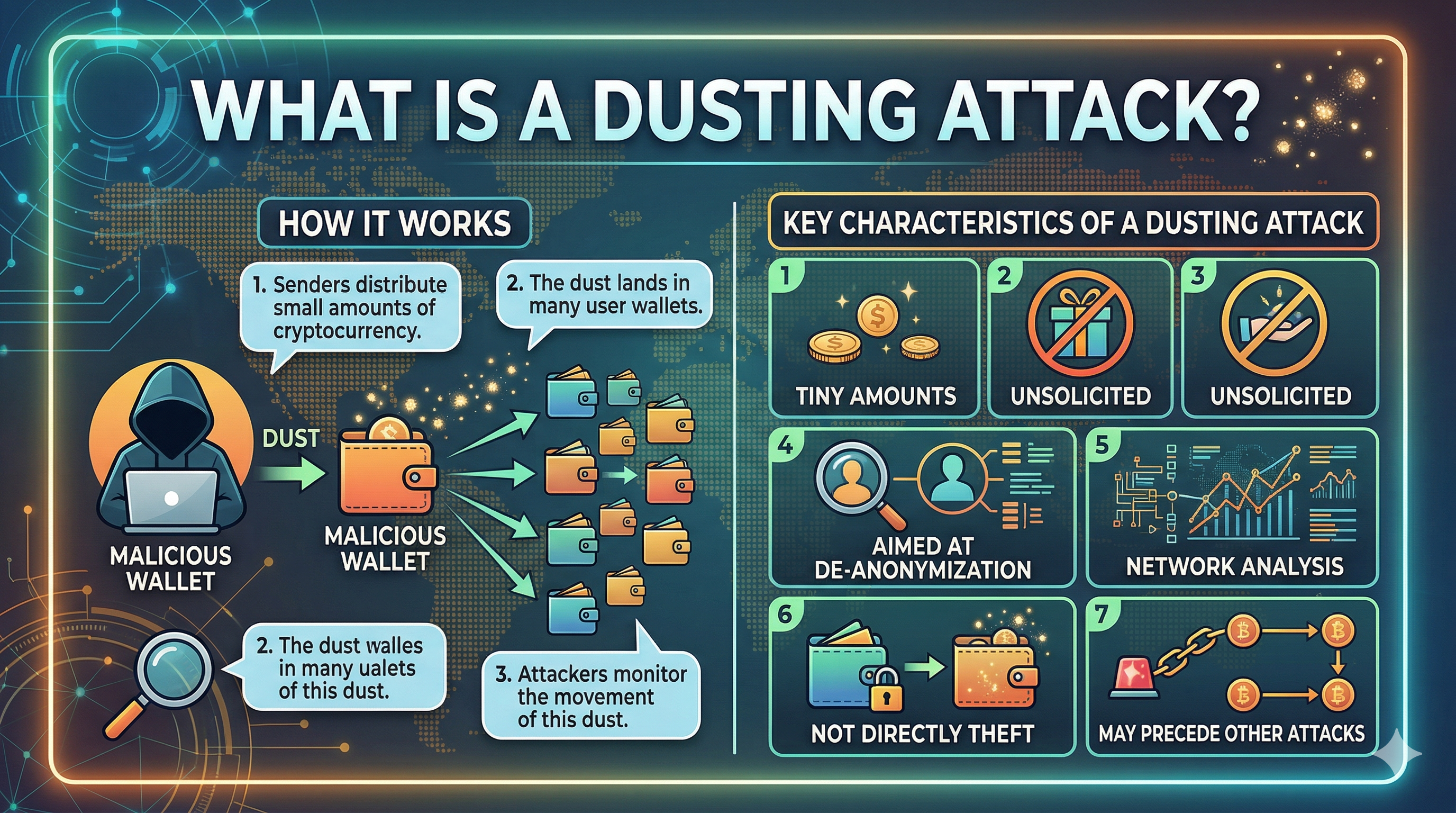
How a Dusting Attack Actually Works
A dusting attack follows a structured process that unfolds in stages, often without the victim realizing what is happening. It begins with data collection. Attackers scan blockchain networks for active wallet addresses, those that frequently send or receive transactions. Active wallets are more likely to interact with the dust later, making them ideal targets.
The next phase is distribution. Small amounts of cryptocurrency are sent to thousands, sometimes millions, of addresses. These transactions are automated, requiring minimal cost relative to the potential intelligence gained. According to CoinTracker’s 2026 breakdown, attackers often use scripts to distribute dust efficiently across large datasets of wallets.
After distribution, monitoring begins. This is the most critical phase. Attackers track the movement of dust using blockchain analytics tools. If the dust remains untouched, it provides little value. If it is spent, however, it becomes a key that unlocks connections between addresses.
The final stage involves clustering and identification. When dust is combined with other funds in a transaction, it reveals that those funds belong to the same entity. If that transaction interacts with a centralized exchange requiring identity verification, the attacker may link wallet activity to a real-world identity.
This process does not rely on breaking security systems. It relies on patience, data analysis, and human behavior. That is what makes it particularly effective, and difficult to detect.
The Core Objective: De-Anonymization
The ultimate goal of a dusting attack is not theft, it is de-anonymization. Cryptocurrency users often assume that their identities are protected because wallet addresses do not include personal information. While technically true, this anonymity is fragile.
Blockchain transparency allows anyone to trace transactions. By linking multiple wallet addresses together, attackers can build a profile of a user’s financial behavior. This includes transaction frequency, asset holdings, and interaction with specific platforms. Over time, this data becomes increasingly detailed.
Once wallet clusters are identified, attackers can infer ownership patterns and even estimate total holdings. This information is highly valuable, especially when targeting high-net-worth individuals or organizations.
The danger escalates when these insights intersect with external data sources. For example, if a wallet interacts with a regulated exchange, identity verification processes may expose personal details. Once a link is established, anonymity collapses.
This is why dusting attacks are often described as intelligence-gathering operations. They are not immediate threats but preparatory steps. By turning anonymous blockchain activity into identifiable patterns, attackers create opportunities for more direct and targeted attacks in the future.
Key Characteristics of a Dusting Attack
Dusting attacks share several defining characteristics that distinguish them from other types of crypto threats. One of the most notable is the extremely small transaction size. These amounts are intentionally insignificant, ensuring they do not trigger concern or immediate action.
Another defining trait is scale. Dusting attacks are rarely targeted at a single wallet. Instead, they involve mass distribution across thousands of addresses. This broad approach increases the likelihood of identifying valuable targets.
Persistence is also a key characteristic. Dusting attacks are not one-time events. Attackers may conduct repeated campaigns, continuously gathering data and refining their analysis. The process can span weeks or even months.
A further characteristic is the reliance on blockchain transparency. Unlike traditional cyberattacks that exploit software vulnerabilities, dusting attacks exploit the open nature of blockchain systems. Every transaction is visible, making it possible to track and analyze user behavior without direct interaction.
Finally, these attacks are passive in nature. They do not require immediate engagement from the victim. The effectiveness of the attack depends on whether the user eventually interacts with the dust.
These characteristics make dusting attacks uniquely subtle. They operate quietly, scale efficiently, and rely on fundamental properties of blockchain technology.
Why Dusting Attacks Matter More in 2026
Dusting attacks have evolved alongside the broader cryptocurrency ecosystem. As blockchain adoption increases, so does the amount of publicly available transaction data. This creates a richer environment for analysis and tracking. Modern blockchain analytics tools are far more advanced than they were a few years ago. They can identify patterns, cluster addresses, and even predict behavior based on transaction history. This makes dusting attacks more effective than ever.
Recent reports show that dusting attacks are increasingly used as part of larger attack strategies. These attacks often serve as the first step in more complex operations, including phishing campaigns and targeted scams.
The rise of decentralized finance (DeFi) and multi-wallet usage has also increased vulnerability. Users often manage multiple wallets for different purposes, creating more opportunities for attackers to map connections between them. This shift means dusting attacks are no longer isolated incidents. They are part of a broader trend toward data-driven cyber threats, where information, not access, is the primary objective.
Real-World Examples and Patterns
Dusting attacks are not theoretical, they have occurred repeatedly across different blockchain networks. Bitcoin, Litecoin, and Ethereum users have all reported receiving unexplained micro-transactions.
One notable pattern involves attaching messages or links to dust transactions. In some cases, users have received tiny amounts of cryptocurrency along with a memo directing them to a website. These links often lead to phishing pages designed to steal credentials or private keys.
Another pattern involves targeting high-value wallets. Attackers focus on addresses with large holdings, as the potential payoff from successful de-anonymization is higher. Once identified, these users may become targets for personalized scams or extortion attempts.
Institutional wallets have also been targeted. In these cases, the objective may extend beyond financial gain to include competitive intelligence. By mapping transaction flows, attackers can infer business relationships and operational strategies. These real-world examples demonstrate that dusting attacks are adaptable. They develop based on the target, the blockchain, and the attacker’s objectives.
Common Misconceptions About Dusting Attacks
One of the most common misconceptions is that dusting attacks directly steal funds. In reality, the attack itself does not compromise wallet security or access private keys. Funds remain safe unless the user falls victim to a secondary attack.
Another misunderstanding is that dusting attacks are rare. While not always visible, they occur more frequently than most users realize. Many wallets contain dust without the owner ever noticing.
Some users also believe that ignoring dust completely eliminates risk. While ignoring dust reduces exposure, the underlying data collection may still occur if patterns can be inferred from other transactions.
There is also a misconception that only large investors are targeted. While high-value wallets are attractive targets, dusting attacks often cast a wide net. Any active wallet can become part of a dataset.
Understanding these misconceptions is important. It shifts the perspective from fear to awareness, helping users recognize the true nature of the threat.
Behavioral Patterns Attackers Look For
Dusting attacks are fundamentally about behavior. Attackers are less interested in the dust itself and more interested in how users interact with it.
One key pattern is transaction grouping. When a user combines multiple inputs in a single transaction, it reveals that those inputs belong to the same entity. This is a primary method for linking addresses.
Another pattern is frequency. Regular transactions provide more data points, making it easier to identify habits and predict future behavior.
Interaction with centralized exchanges is also a critical signal. These platforms often require identity verification, creating a bridge between anonymous blockchain activity and real-world identity.
Timing patterns can also reveal insights. For example, consistent transaction times may indicate geographic location or routine behavior.
These behavioral signals, when combined, create a detailed profile. This is the ultimate objective of a dusting attack, not just identifying a wallet, but understanding the person behind it.
How Dusting Attacks Lead to Larger Threats
Dusting attacks are rarely the end goal. They are the beginning of a larger strategy. Once attackers gather enough data, they can launch more targeted and effective attacks.
Phishing is one of the most common follow-ups. Armed with knowledge about a user’s holdings or recent transactions, attackers can craft highly convincing messages. These messages may reference specific details, making them more likely to succeed.
Extortion is another potential outcome. If an attacker identifies a high-value wallet, they may attempt to threaten or coerce the owner.
In some cases, dusting attacks are used for surveillance rather than direct exploitation. Organizations may use them to monitor competitors or track market behavior.
This progression, from data collection to targeted action, shows why dusting attacks should not be dismissed as harmless. They are part of a broader ecosystem of cyber threats.
How to Recognize a Dusting Attack
Recognizing a dusting attack requires attention to detail. The most obvious sign is receiving a very small, unexpected transaction from an unknown address. These transactions often appear without explanation. They may not include a message or may contain vague or suspicious notes.
Another indicator is repetition. Multiple small deposits over time may suggest an ongoing campaign rather than a random occurrence.
Users should also pay attention to unfamiliar tokens. In some cases, dust may appear as new or obscure assets added to a wallet.
Monitoring transaction history is essential. Regular review can help identify unusual patterns and distinguish between normal activity and potential attacks. Awareness is the first line of defense. Recognizing the signs early can prevent further exposure.
Final Thoughts: A Data Game Disguised as a Transaction
Dusting attacks reveal a fundamental truth about blockchain technology: transparency is both a strength and a vulnerability. The same openness that enables trust also enables surveillance.
These attacks are not about immediate financial gain. They are about information, collecting it, analyzing it, and using it strategically. In a world where data is power, even the smallest transaction can become a valuable asset.
Understanding dusting attacks is not just about security. It is about perspective. It requires seeing beyond the surface and recognizing how seemingly insignificant actions can have broader implications.
As cryptocurrency continues to grow, so too will the methods used to exploit it. Dusting attacks are just one example of how innovation can be used in unexpected ways.
FAQs
1. What is a dusting attack in simple terms?
A dusting attack is when someone sends tiny amounts of cryptocurrency to many wallets to track and identify their owners.
2. Can a dusting attack steal my crypto?
No, it cannot directly steal funds. The risk comes from follow-up attacks like phishing.
3. Why do attackers use dust instead of hacking?
Because blockchain data is public, attackers can gather information without breaking security systems.
4. Should I be worried if I receive dust?
Not immediately, but you should avoid interacting with it and stay alert.
5. Is dusting attacks common in 2026?
Yes, especially with advanced blockchain analytics making tracking easier.
Disclaimer
This content is for informational purposes only and does not constitute investment advice. Cryptocurrency investments carry risk. Please do your own research (DYOR).