Bitcoin’s Quantum Wake-Up Call: Inside BIP-361 and the Push to Freeze Legacy Coins
2026/05/01 04:13:08
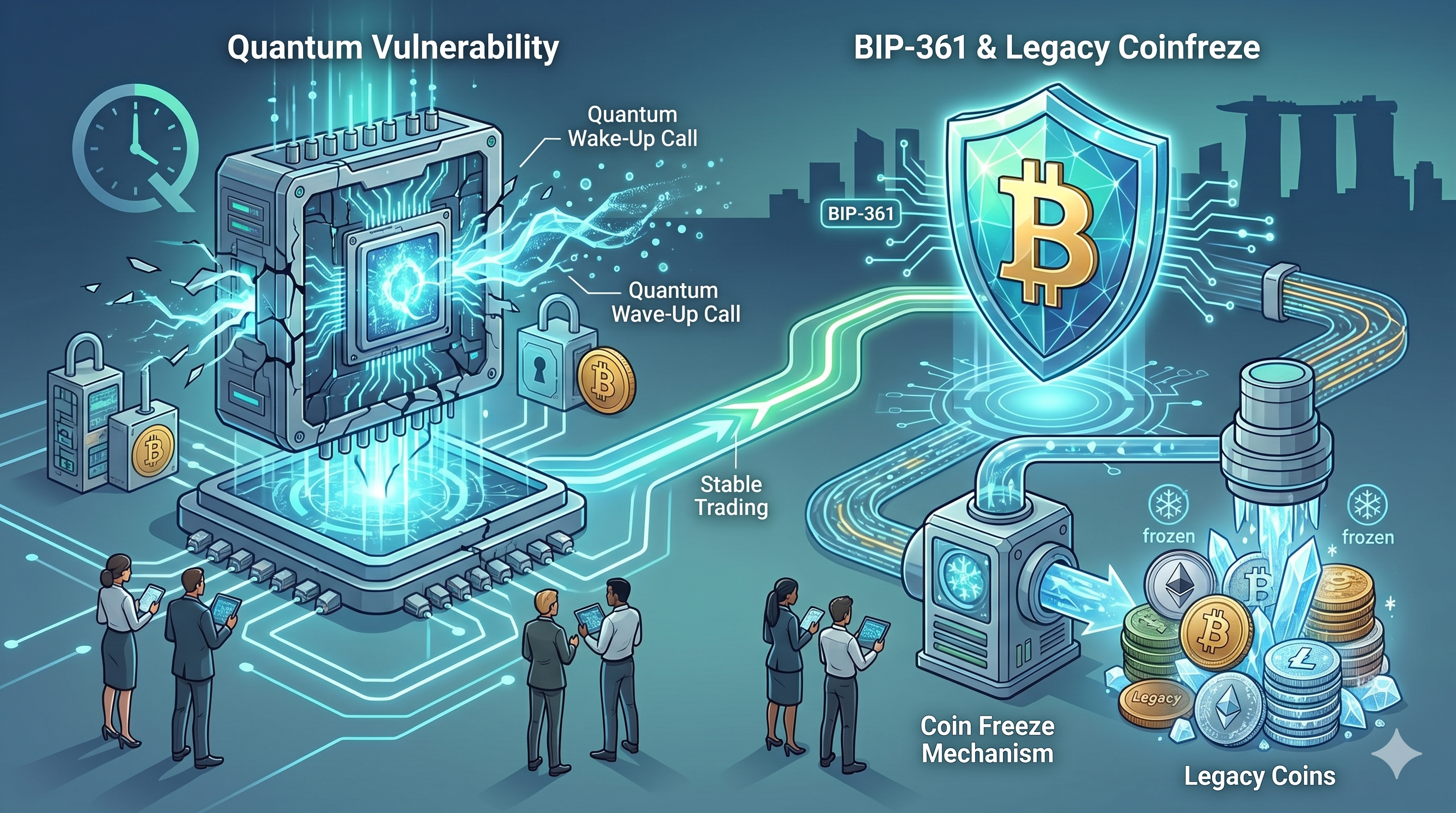
Thesis Statement
Bitcoin faces a distant but serious risk from quantum computers that could one day crack its current cryptography. A new proposal called BIP-361 aims to prepare the network by encouraging holders to move funds to safer addresses while setting deadlines that could leave old coins unspendable if ignored. This bold step highlights growing concern over exposed public keys in legacy wallets and pushes the community to act before threats become real.
How Quantum Computers Could Target Bitcoin’s Core Security
Quantum computers operate differently from today’s machines by using qubits that handle complex calculations in parallel. Shor’s algorithm stands out as the key tool that could break elliptic curve cryptography, the foundation of Bitcoin’s ECDSA and Schnorr signatures. Once a quantum machine reaches sufficient scale, it could derive private keys from public ones exposed on the blockchain. Early Bitcoin addresses, especially Pay-to-Public-Key (P2PK) types from the mining era, reveal public keys directly. Any transaction that spends from an address also exposes the key in the process.
Estimates show roughly 6.7 million BTC, or about 34% of the total supply, sits in such vulnerable positions. This includes around 1.7 million BTC locked in pure P2PK outputs, with a significant portion linked to early holders and even estimates of Satoshi Nakamoto’s roughly 1.1 million BTC. Recent research from Google Quantum AI in early 2026 lowered the bar for a credible threat. Models suggest a system with under 500,000 qubits might execute an attack in about nine minutes, faster than Bitcoin’s average block time. Other studies point to possibilities with as few as 10,000 qubits for scaled Shor’s implementations.
While no such machine exists today, progress in error correction and hardware has shortened projected timelines, with some experts now eyeing 2029 as a potential milestone for heightened risks. The danger grows because attacks might stay hidden. An attacker could quietly drain funds without immediate detection, eroding trust. A malicious actor might instead broadcast massive moves to crash confidence in the network. Developers argue that waiting until the threat materializes leaves no room for orderly preparation, turning a technical upgrade into a potential crisis.
Meet the Team Behind BIP-361 and Their Urgent Motivation
Jameson Lopp, co-founder of Casa and a longtime Bitcoin contributor, leads the effort alongside five other experts in quantum security. The group published the draft on April 15, 2026, titling it “Post Quantum Migration and Legacy Signature Sunset.” Lopp has openly shared mixed feelings, stating he dislikes the idea but fears the alternative of quantum theft even more. He frames it as adversarial thinking to protect the network’s long-term integrity.
The proposal builds directly on BIP-360, which introduced a new Pay-to-Merkle-Root (P2MR) output type. This design keeps public keys off-chain, shrinking the attack surface for new transactions. BIP-361 adds enforcement layers to drive widespread adoption of such safer methods. Co-authors include figures like Hunter Beast from MARA Protocol, who describes the roadmap as essential to “quantum-harden” Bitcoin.
Insiders emphasize that the push comes from years of monitoring quantum advances. Blockstream Research has already tested post-quantum cryptography on sidechains, showing practical steps exist. The team sees BIP-361 as creating private economic incentives for users to upgrade rather than relying on voluntary action alone.
Breaking Down the Three-Phase Migration Timeline
BIP-361 lays out a clear, multi-year schedule once activated through a soft fork. Phase A kicks in after roughly three years, measured by 160,000 blocks. From that point, the network stops accepting new sends to quantum-vulnerable legacy address types. Users gain a window to move holdings to P2MR or future quantum-resistant formats without immediate pressure on existing balances.
Phase B follows about two years later. At this stage, the protocol rejects any transactions that rely on legacy ECDSA or Schnorr signatures from unmigrated addresses. Funds in those wallets become effectively frozen, meaning owners cannot spend them even if they hold the private keys. The goal is to eliminate the vulnerable signature schemes from active use across the network.
Phase C remains under discussion and would introduce a recovery path for frozen coins. It envisions zero-knowledge proofs tied to BIP-39 seed phrases, allowing legitimate owners to reclaim access after proving control. Details need further research and consensus, but the option aims to balance security with user rights for those who miss earlier deadlines.
This structured approach gives the ecosystem time to adapt. Wallets, exchanges, and custodians can update tools, while users learn about migration. The phases turn security into an incentive by raising friction for outdated setups.
Real Numbers on Bitcoin at Risk from Quantum Exposure
Data paints a striking picture of exposure. Around 1.7 million BTC rest in classic P2PK scripts, many from Bitcoin’s earliest blocks when rewards reached 50 BTC. Broader estimates reach 6.7 million BTC when including dormant addresses with exposed keys from past spending or reuse. This slice equals roughly one-third of all Bitcoin ever created.
Satoshi-era coins feature heavily in discussions. Analysts link about 1.1 million BTC to the creator’s wallets, most in vulnerable formats. Recent on-chain activity shows over 85,000 BTC from old wallets moving in the past year, hinting that some holders have already repositioned for safety. Yet vast dormant supplies remain untouched.
Top addresses and institutional holdings add layers. Even modern setups face risks if keys get reused or exposed in the mempool during pending transactions. The concentration in early mining outputs means a successful quantum attack could unlock enormous value, potentially flooding markets or triggering panic if partial evidence leaks.
These figures drive urgency. Developers note that lost coins already boost scarcity for the remaining supply, but quantum-drained coins would instead undermine confidence and value.
Why Legacy Addresses Stay Vulnerable Even Today
Bitcoin’s original design prioritized simplicity. Early P2PK outputs placed public keys directly in the script, making them visible forever on the immutable ledger. Later formats improved privacy, but any spent address still reveals the key at the moment of transaction. Taproot, while powerful, exposes keys by default in certain cases, compounding the issue for newer users who do not take extra steps. The mempool creates short-term windows of exposure for every transaction. Quantum machines, if powerful enough, could race to derive keys and front-run spends within the ten-minute block window. At-rest attacks on never-spent legacy coins pose the bigger long-term risk since public keys sit openly for years.
No immediate breach exists because current quantum hardware lags far behind requirements. Google’s Willow processor operates with just over 100 qubits, while estimates for breaking ECDSA start in the hundreds of thousands. Yet rapid progress in error-corrected logical qubits keeps researchers watchful. Holders of old coins often treat them as long-term stores, sometimes losing seeds or hardware over time. Migration requires careful planning to avoid mistakes that could result in permanent loss during transfers.
How BIP-361 Builds on Earlier Quantum-Ready Work
BIP-360 sets the technical foundation by introducing P2MR outputs. This Merkle-root approach commits to scripts without revealing public keys on-chain, directly addressing a core weakness. New transactions using P2MR stay secure even against future quantum advances. BIP-361 layers governance and incentives on top. It does not invent new signatures yet but prepares the network to sunset old ones once a consensus post-quantum algorithm emerges. Candidates include lattice-based, hash-based like SPHINCS+, or hybrid schemes that balance security and efficiency.
The combination creates a roadmap. First, standardize safe output types. Then, encourage migration through restrictions. Finally, phase out vulnerable signatures. This modular strategy avoids rushed changes while building resilience step by step. Sidechain experiments already demonstrate feasibility. Blockstream’s tests with post-quantum protection show real-world performance without disrupting mainnet rules.
What Migration to Quantum-Safe Wallets Actually Involves
Users would move funds from legacy addresses to new P2MR or equivalent outputs. The process resembles standard sends but requires updated wallet software that supports the safer formats. Custodians and exchanges play a big role by offering seamless tools and warnings to clients holding exposed balances. Costs stay modest for most, similar to regular fees, though large dormant holdings might need multiple transactions for safety. Education campaigns could highlight steps, such as generating fresh seeds and verifying addresses.
Institutions with cold storage face extra planning. They must audit holdings, test migrations in staging environments, and coordinate with auditors. The phased timeline gives years for such work, reducing rushed errors. Individual holders with paper wallets or hardware from the early days might need to revive old devices carefully. The proposal aims to create gentle pressure rather than sudden locks, giving everyone a fair window.
Reactions and the Debate Over Frozen Coins
Bitcoiners split sharply on the idea. Supporters call it responsible stewardship that protects the network’s value for everyone. They point out that frozen coins resemble lost ones, which Satoshi himself noted increases scarcity for active supply. Lopp argues economic incentives should outweigh pure philosophy when facing existential risks. Critics push back hard, labeling the plan as authoritarian or a violation of Bitcoin’s immutability and self-sovereignty. They worry about dormant holders who lost access years ago or simply stayed offline. Freezing billions in value, especially legendary early coins, raises questions about precedent and trust in developer decisions.
Discussions on forums and social platforms reflect passion. Some see it as a necessary evolution, while others fear it opens doors to future interventions. Lopp acknowledges the discomfort but maintains that the alternative, mass theft, would hurt far more. The debate itself signals healthy engagement. Bitcoin has always grown through open proposals and consensus, and BIP-361 enters that arena as a draft open to evolution.
Potential Market Effects if the Proposal Gains Traction
A credible migration path could boost confidence by showing proactive defense. Reduced uncertainty might attract more institutional money seeking long-term security. Scarcity from any frozen supply could support price dynamics, though the effect depends on actual implementation. Short-term volatility might arise during debates or as users move coins. Exchanges could see increased withdrawal activity as people test new wallets. Wallet providers would likely release updates quickly to capture demand.
Long-term, successful quantum hardening strengthens Bitcoin’s narrative as the most secure digital asset. It positions the network ahead of other blockchains still grappling with similar issues. Analysts watch on-chain metrics closely. Rising movement from old addresses already hints at preparation, and BIP-361 could accelerate that trend.
Insider Views on Quantum Timelines and Readiness
Experts differ on exact dates but agree that preparation matters. Some place credible threats a decade or more away, while Google’s work compresses expectations toward the late 2020s. The Bitcoin Policy Institute notes advances tighten timelines without creating immediate panic. Developers stress that upgrades take years for testing, consensus, and rollout. Starting discussions now avoids last-minute scrambles. Lopp and co-authors frame BIP-361 as a sketch that will evolve with more research.
Industry voices like Adam Back have called the threat distant, yet the community benefits from exploring defenses early. Coordination between researchers, wallet teams, and node operators will prove key. Real-world tests on sidechains provide confidence that post-quantum tools can integrate without sacrificing performance.
The Human Side of Securing Generational Wealth
Stories emerge of early miners who set aside coins and moved on with life. Some lost devices or forgot seeds, turning holdings into digital time capsules. Others guard them carefully as family legacies. Migration forces reflection. A holder waking an old laptop to transfer funds might feel the weight of history. Custodians helping institutions safeguard employee or client assets add layers of responsibility.
The proposal touches real people. A developer spending nights refining code, a trader auditing personal wallets, or a family debating how to handle inherited keys—all become part of the larger story. Bitcoin’s strength has always come from participants who care enough to engage deeply. Proactive steps today preserve options for tomorrow, ensuring the network remains a reliable store of value across generations.
Technical Challenges in Implementing Post-Quantum Changes
Integrating new cryptography requires careful balancing of security, size, and speed. Post-quantum signatures often produce larger keys or proofs, potentially affecting block space and fees. Hybrid approaches might combine classical and quantum-resistant methods during transition. Node software must validate new rules without breaking old consensus. Soft fork mechanisms help by making changes backward-compatible at first. Testing on testnets and sidechains catches edge cases before mainnet activation.
Signature validation times matter for miners and full nodes. Efficient algorithms keep the network responsive even as security strengthens. The community continues researching candidates to find the best fit for Bitcoin’s unique constraints.
Long-Term Prospect for a Quantum-Resistant Bitcoin Network
BIP-361 represents one piece in a broader effort to future-proof Bitcoin. Success would mean a network where new funds stay protected by design and old risks gradually fade. It reinforces the idea that Bitcoin evolves through careful, community-driven improvements.
As quantum technology advances in labs worldwide, the blockchain community gains time to test, debate, and refine solutions. The focus stays on preserving core principles while adapting to new realities. Holders who act early gain peace of mind. The network as a whole gains resilience that supports its role as digital gold for decades ahead.
How Wallet Developers and Exchanges Prepare for the Shift
Teams already update interfaces to flag vulnerable addresses and suggest safer alternatives. Educational resources explain risks in plain terms. Exchanges plan support for new output types and may offer migration services.
Custody providers invest in quantum-safe storage solutions, testing recovery flows in advance. The ecosystem’s response will determine how smoothly the transition unfolds.
Coordination ensures no single point of failure during the multi-year window.
Why Starting the Conversation Now Strengthens Bitcoin
Early discussion prevents surprise. It surfaces concerns, gathers feedback, and improves the proposal before any activation. Bitcoin thrives on transparency, and BIP-361 fits that tradition by laying ideas open for review.
The process itself builds knowledge across the community. Users learn more about their own security practices. Developers sharpen tools. Researchers push boundaries in cryptography. In the end, preparation turns potential weakness into demonstrated strength.
FAQs
What exactly does BIP-361 propose for Bitcoin users holding old addresses?
The draft suggests a phased approach where, after activation, new deposits to vulnerable legacy addresses get blocked after three years. Two years later, spending from those addresses using old signatures could stop entirely, effectively freezing the funds unless migrated to quantum-resistant formats like those enabled by BIP-360. A possible later recovery mechanism using zero-knowledge proofs remains under study to help legitimate owners. The idea gives years of notice so people can move coins safely without sudden disruption.
How many Bitcoins currently sit in quantum-vulnerable positions?
Estimates place roughly 6.7 million BTC, or about 34% of total supply, in addresses with exposed public keys. This includes 1.7 million BTC in early P2PK outputs alone. Many of these coins come from Bitcoin’s first years and have stayed dormant, though some movement from old wallets occurs as holders prepare. The exact risk depends on future quantum hardware, but the volume involved makes the topic important for network health.
Who created BIP-361, and what do they say about it?
Jameson Lopp and five co-authors from the quantum security space published the proposal in mid-April 2026. Lopp has noted discomfort with freezing mechanisms but argues the risk of quantum theft justifies exploring strong incentives for migration. The group presents it as an evolving sketch open to community input rather than a finished plan ready for immediate adoption.
Will BIP-361 require a hard fork or change Bitcoin’s rules drastically?
The proposal aims for implementation via soft fork, maintaining compatibility for non-vulnerable transactions. It builds on existing upgrade paths and focuses on sunsetting specific legacy signature uses over time. No immediate changes to block production or consensus would occur, and the timeline spreads adjustments across several years.
What steps should Bitcoin holders take right now regarding quantum risks?
Check wallet types and whether public keys appear on-chain for your addresses. Consider moving funds to modern wallets that support newer output types and avoid key reuse. Stay informed through official Bitcoin channels and test small transfers first. Using hardware wallets with fresh seeds adds protection. Monitor updates on BIP-360 and related work as tools improve.
Could frozen coins under BIP-361 ever get recovered?
Phase C explores recovery through zero-knowledge proofs linked to seed phrases, allowing owners to prove control without exposing keys broadly. Details need more research and consensus, so nothing is finalized. The goal balances security against theft with fairness for users who might miss migration windows for legitimate reasons.
Disclaimer: This content is for informational purposes only and does not constitute investment advice. Cryptocurrency investments carry risk. Please do your own research (DYOR).