CoW Swap Frontend Attack Explained: DNS Hijacking, How It Works, and How to Protect Your Wallet in DeFi
2026/04/22 11:00:00
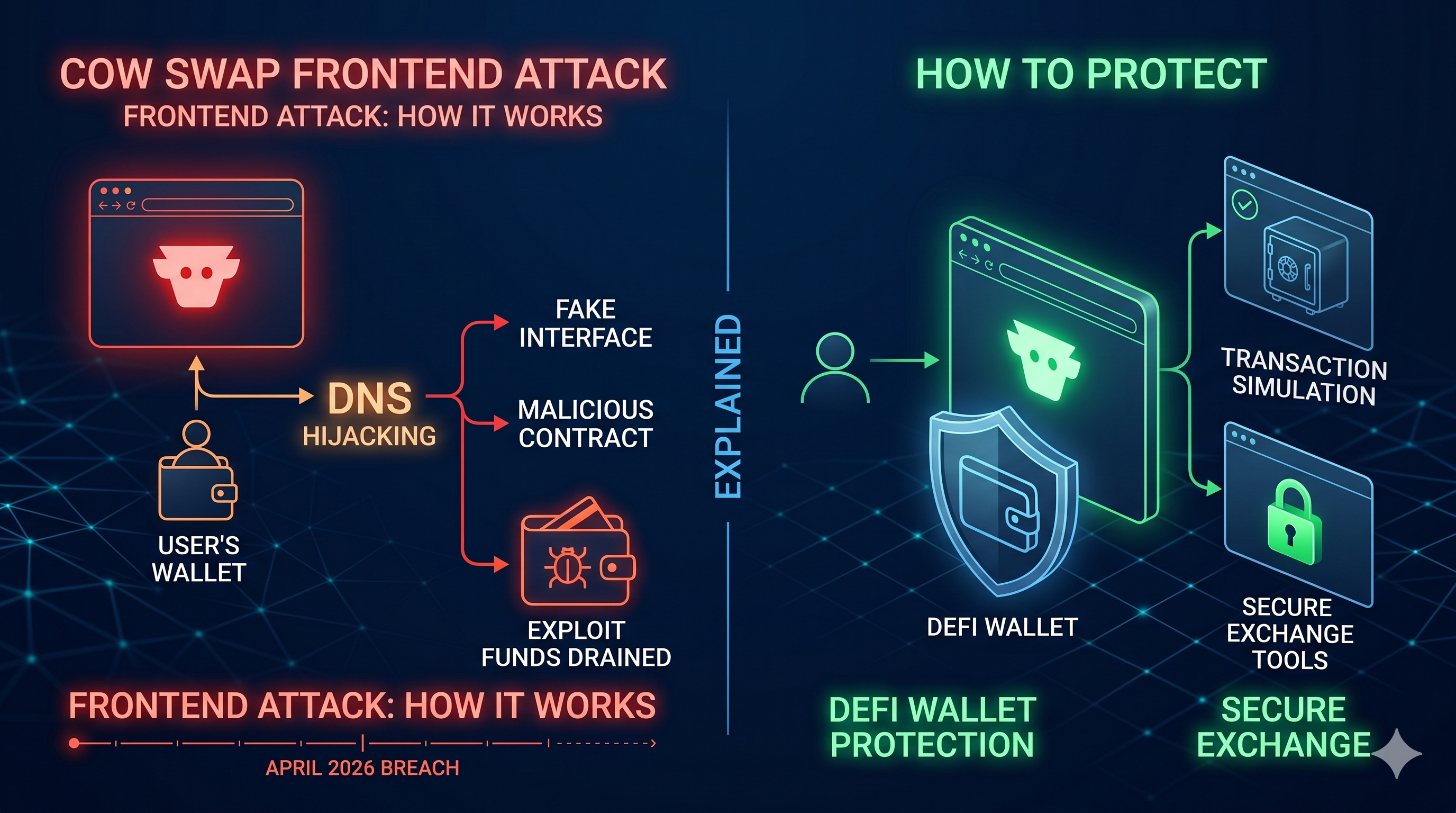
In the high-stakes world of decentralized finance, security is usually discussed in terms of smart contract audits and on-chain vulnerabilities. However, the April 2026 CoW Swap attack served as a brutal reminder that the most vulnerable part of a dApp isn't always the code, it’s the interface. By hijacking the domain name system (DNS), attackers managed to siphon over $1.2 million from users who thought they were using a trusted platform.
This article explains how the CoW Swap DNS hijack occurred, why frontend attacks are becoming the preferred weapon for hackers in 2026, and the specific steps you must take to ensure your wallet remains safe when the "official" website can no longer be trusted.
Key Takeaways
-
On April 14, 2026, the cow.fi domain was hijacked, redirecting users to a malicious phishing site that drained connected wallets.
-
Unlike a smart contract exploit, DNS hijacking manipulates the path between your browser and the server, making a fake site look identical to the real one.
-
The CoW Swap attackers used forged documents and supply chain vulnerabilities in the .fi domain registration process to gain control.
-
Users should rely on transaction simulation tools and hardware wallets that show the actual raw transaction data, not just what the website displays.
-
If you interacted with CoW Swap during the attack window, you must revoke all permissions using tools like Revoke.cash immediately.
The April 2026 CoW Swap DNS Hijack: What Happened?
In the current DeFi landscape, we often assume that as long as a protocol’s smart contracts are audited, our funds are safe. However, the events of April 14, 2026, proved that the web infrastructure sitting between the user and the blockchain is a massive, often under-secured target. The attack on CoW Swap was not a failure of decentralized code, but a sophisticated exploitation of the centralized Domain Name System (DNS).
A Timeline of the Breach
The incident began at approximately 14:54 UTC on April 14, when the CoW Swap team first identified anomalies in the resolution of the
cow.fi domain. Within minutes, it became clear that the official frontend had been hijacked at the registrar level.-
14:54 UTC: The breach is detected. Attackers successfully redirected traffic from
swap.cow.fito a malicious IP address hosting a pixel-perfect clone of the trading interface. -
15:41 UTC: CoW DAO issued an urgent public warning on social media, instructing users to cease all interactions with the site and revoke any recent permissions.
-
18:30 UTC: To maintain service continuity and protect users, the team initiated an emergency migration to a fallback domain, cow.finance.
-
April 15: Following intense coordination with the .fi registry and Gandi SAS, the original
cow.fidomain was fully recovered and secured with RegistryLock within roughly 26 hours of the initial hijack.
The Impact and Losses
While the attack was relatively short-lived, its impact was significant due to the high volume of liquidity typically moving through the CoW Protocol. Preliminary post-mortem data estimates total user losses at approximately $1.2 million.
The most high-profile theft involved a single trader who unknowingly interacted with the malicious frontend, resulting in the loss of 219 ETH (worth over $750,000 at the time). The attackers utilized a "wallet drainer" script that presented users with what looked like standard token approval but was actually a broad permit allowing the attacker to sweep assets.
Crucially, CoW Swap confirmed that the on-chain contracts, backend APIs, and solver networks remained entirely secure. The core protocol infrastructure was never breached; the vulnerability existed solely in the domain registration supply chain, where attackers used forged identity documents to trick registrar staff into handing over DNS control.
Anatomy of a DNS Hijacking: How It Works
In a hack, the underlying code is exploited. In a hijack, the infrastructure leading to that code is diverted. Think of it like a thief who doesn't pick the lock on your house but instead changes the street signs so you accidentally drive to a counterfeit version of your home.
The Domain Registration Supply Chain Attack
Most DeFi users assume that domain security is as decentralized as blockchain, but it remains one of the most centralized vulnerabilities in Web3. In the case of CoW Swap, the attackers didn't breach CoW DAO’s internal servers; they targeted the supply chain, specifically the Finnish registry and the registrar.
Using sophisticated social engineering and forged identity documents, the attackers convinced registrar support staff that they were the legitimate owners of the
cow.fi domain. Once they gained access to the administrative account, they didn't delete the site. Instead, they modified the DNS A Records, pointing the domain away from CoW Swap's secure servers and toward a malicious Cloudflare-hosted server under their control.The Phishing "Shadow" Site
Once the DNS was diverted, anyone typing
swap.cow.fi was served a "shadow" version of the site. This counterfeit UI was pixel-perfect, often using the original site's own CSS and image assets to look identical to the real platform.The core of this shadow site was a Wallet Drainer script. When a user connected their wallet, the script would:
-
Scan for Assets: Instantly identify the most valuable tokens and NFTs in the user's wallet.
-
Generate Malicious Permits: Instead of a standard swap, the site would pop up a signature request for an ERC-2612 Permit or a broad
setApprovalForAllfunction. -
The Lure: The UI would disguise these signatures as a "Security Update" or a "Network Verification" step. Once the user signed, they were effectively handing the attacker a "blank check" to move their assets at will.
Why Your Browser Can't Tell the Difference
The most terrifying aspect of a DNS hijack is that it bypasses standard user intuition. Because the DNS resolution happens at the infrastructure level, the URL in your browser address bar remains exactly the same—it still says
https://swap.cow.fi.Why Frontend Attacks Are the New DeFi Frontier?
For years, the primary threat was a "bug in the code", a logic flaw in a smart contract that allowed hackers to drain a protocol’s treasury. However, as formal verification and AI-powered auditing tools have made on-chain exploits harder to execute, attackers have redirected their efforts toward the path of least resistance: the user interface.
Matured Contracts vs. Weak Infrastructure
The DeFi industry has spent millions on smart contract audits, but very little on web infrastructure security. While a protocol’s vault might be mathematically secure, the website used to access that vault often relies on 1990s-era centralized technology like DNS and domain registrars.
Hackers have realized it is far easier to trick a registrar employee through social engineering or identity forgery than it is to find a zero-day vulnerability in a battle-tested Solidity contract. This is why we have seen a massive uptick in frontend attacks hitting major protocols like OpenEden, Curvance, and Maple Finance.
DNS as a Trust Backslide
Frontend attacks are uniquely dangerous because they are invisible to the naked eye. In a standard phishing attack, a user might notice a misspelled URL (e.g.,
coowswap.fi). In a DNS hijacking event like the CoW Swap breach, the URL is 100% correct.Vitalik Buterin famously declared 2026 as the year developers must reverse "DNS trust backsliding." The core issue is that the modern web browser was not built for the "Code is Law" era. When a DNS server is compromised, it breaks the entire chain of trust without any warning to the user. Your browser’s "Lock" icon is effectively weaponized against you, providing a false sense of security while you are connected to a malicious IP.
The Rise of Scam-as-a-Service
A new generation of wallet drainers, such as the AngelFerno drainer, has made it possible for even low-skill attackers to execute high-impact frontend hijacks.
These drainer scripts are sophisticated pieces of software that:
Identify the "Whales": Instantly scan a connected wallet to prioritize the most valuable assets.
Craft Deceptive Signatures: They don't just ask for a transfer; they generate complex ERC-2612 Permit signatures that look like standard protocol interactions but grant the attacker total control.
Automate Profits: The stolen funds are automatically split between the scammer and the drainer developer, creating a professionalized incentive loop that ensures frontend attacks remain a persistent threat to the DeFi frontier.
How to Protect Your Wallet from Frontend Attacks?
Use Transaction Simulation Tools
The most effective defense against a hijacked frontend is a pre-transaction firewall. Tools like Pocket Universe, Wallet Guard, and Fire are browser extensions that act as an intermediate layer between the dApp and your wallet.
When you click "Swap" or "Approve," these tools simulate the transaction in a private environment and show you exactly what will happen to your assets before you sign. If a hijacked site tries to use a "Permit" to drain your ETH while displaying a "Confirm Swap" button on the UI, the simulator will flag the discrepancy, showing a warning that "219 ETH will leave your wallet for $0 in return."
Leverage Isolated Signing Environments
Traditional wallets like MetaMask are often "blind" to the malicious intent of a hijacked frontend. Now, many power users have migrated to Rabby Wallet or Frame, which are built specifically for DeFi security.
Automatic Risk Scanning: Rabby natively parses every transaction, flagging if a contract is new, unverified, or has been recently associated with exploits.
Whitelisted Origins: These wallets maintain a database of verified official contract addresses. If you are on
cow.fi but the contract asking for approval isn’t the official CoW Swap Settlement contract, the wallet will throw a high-level security alert.Contextual Clarity: Instead of showing a raw hex string, these environments translate the code into plain English: "You are giving [Hacker Address] permission to spend your USDC."
Hardware Wallets
A hardware wallet like the Ledger Flex or Trezor Safe 5 is only as secure as the user operating it. During the CoW Swap attack, many victims used hardware wallets but still lost funds because they enabled "Blind Signing."
To survive a DNS hijack, you must treat your hardware wallet's screen as the only source of truth.
Disable Blind Signing whenever possible to force the device to show the full transaction details.
Verify the Recipient: Always check the contract address shown on your Ledger or Trezor against a trusted source (like Etherscan or the project's official documentation).
Check the Amount: If you are doing a $100 swap but the device shows an "Unlimited" allowance request, reject the transaction immediately.
Permission Hygiene and Revocation
Even if you haven't been attacked, you likely have infinite approvals sitting in your wallet from past trades. If any of those protocols suffer a frontend breach in the future, your funds are at risk.
Establishing a routine of Permission Hygiene is critical. Use Revoke.cash or your wallet’s built-in approval manager once a week to audit your permissions. Look for:
Unlimited Allowances: Change these to specific amounts.
Stale Contracts: Revoke access for any dApp you haven't used in the last 30 days.
Suspicious Permits: If you see an approval for a contract you don't recognize, revoke it instantly.
Trading Safely Amid Security Risks on KuCoin
While DeFi offers innovation, the lack of centralized accountability during a DNS hijack can leave users stranded. For those looking to gain exposure to the DeFi ecosystem without the infrastructure risks of unverified frontends, KuCoin provides a secure, monitored environment built on institutional-grade safety.
Accessing DeFi Tokens via Secure Exchanges
When a protocol like CoW Swap suffers a frontend breach, the price of the native token (COW) often experiences extreme volatility. Trading on the KuCoin Spot Market allows you to swap and hold COW tokens without ever interacting with a potentially hijacked dApp interface. By keeping your assets within the KuCoin ecosystem, you benefit from real-time market monitoring and deep liquidity, ensuring you can enter or exit positions even when a protocol's official website is offline or compromised.
KuCoin’s Security Infrastructure
Unlike the decentralized domain registrars that failed during the CoW Swap attack, KuCoin employs a multi-layered defense strategy designed for institutional resilience.
As of 2026, KuCoin maintains SOC 2 Type II and ISO 27001:2022 certifications, representing the gold standard for information security management.
Following major wallet architecture optimization, KuCoin has enhanced its address management logic, providing a more reliable and resilient asset protection system that is monitored in real-time by dedicated technical teams.
KuCoin utilizes multi-factor authentication (MFA) and withdrawal delay protocols for new addresses, preventing the "instant drain" scenarios commonly seen in frontend phishing attacks.
Earning Yield with Institutional Security
One of the primary drivers for users to visit risky DeFi frontends is the search for yield.
Hold to Earn: KuCoin’s Hold to Earn feature allows you to generate daily rewards directly on your available trading balances (Spot, Margin, and Futures) without ever locking your funds.
KuCoin Earn: For those seeking higher yields, KuCoin Earn offers a suite of professional-grade products, from Simple Earn to fixed-term staking, all backed by the exchange's internal risk controls. This provides a much safer alternative to interacting with experimental DeFi interfaces during periods of market-wide DNS instability.
Conclusion
The CoW Swap incident of 2026 is a stark reminder that the decentralized part of DeFi often ends at the user interface. As attackers shift their focus from complex code exploits to simple, effective DNS hijacking, the responsibility for security falls back on the user. By combining hardware wallets, transaction simulation, and the institutional security of platforms like KuCoin, you can navigate the DeFi landscape without becoming the next headline.
FAQs
Is CoW Swap safe to use now?
Yes. The CoW team recovered the domain, implemented RegistryLock, and migrated to a more secure infrastructure. However, always verify you are on the correct URL.
Did the CoW Swap attack affect on-chain contracts?
No. Smart contracts were never compromised. Only the website interface was hijacked. If you did not sign a transaction during the attack window, your funds remain safe.
What is a RegistryLock?
RegistryLock is an additional security layer provided by domain registrars that requires manual, multi-factor verification from authorized personnel before any changes can be made to a domain’s DNS settings.
How can I tell if a site has been hijacked?
It is nearly impossible to tell by looking at the URL alone. Use a transaction simulator (like Rabby Wallet) to see if the contract you are interacting with is the verified, official contract.
Should I move my funds to a new wallet?
If you signed an "approval" or "permit" during the attack window, your wallet may be at risk. You should revoke all permissions immediately via Revoke.cash or move your assets to a fresh, secure hardware wallet.
Disclaimer:This content is for informational purposes only and does not constitute investment advice. Cryptocurrency investments carry risk. Please do your own research (DYOR).

