Elliptic Curve Cryptography (ECC) Explained: The Core of Blockchain Security and Its Impact
2026/04/17 14:09:02

Elliptic Curve Cryptography (ECC) serves as the foundational mathematical framework that secures modern distributed ledger technology. By leveraging the algebraic structure of elliptic curves over finite fields, this method provides a high level of security with relatively small key sizes, making it ideal for the resource-constrained environments of decentralized networks. Its ability to facilitate trustless verification without the need for centralized intermediaries is a cornerstone of the entire digital asset ecosystem.
At the heart of every secure transaction lies the application of Elliptic Curve Cryptography, which enables robust digital signatures that verify ownership and integrity. Whether you are trading or accessing the token's markets, you are indirectly interacting with these complex mathematical proofs that maintain the immutability of the blockchain.
Key Takeaways
-
Elliptic Curve Cryptography provides high security with smaller key sizes compared to traditional methods, enhancing efficiency for distributed networks.
-
Digital signatures generated through these curves allow users to prove ownership of assets without revealing their private keys.
-
The SECP256K1 curve is the specific standard used in foundational blockchain networks, defining the math behind public and private key derivation.
-
Public Key Infrastructure relies on the mathematical difficulty of the discrete logarithm problem to ensure that public keys cannot be inverted to reveal private keys.
-
Understanding these security primitives is essential for grasping why assets are secure and how transactions are verified on-chain.
-
Market confidence in digital assets is fundamentally underpinned by the mathematical rigor of these cryptographic standards.
The Mathematical Foundation of ECC
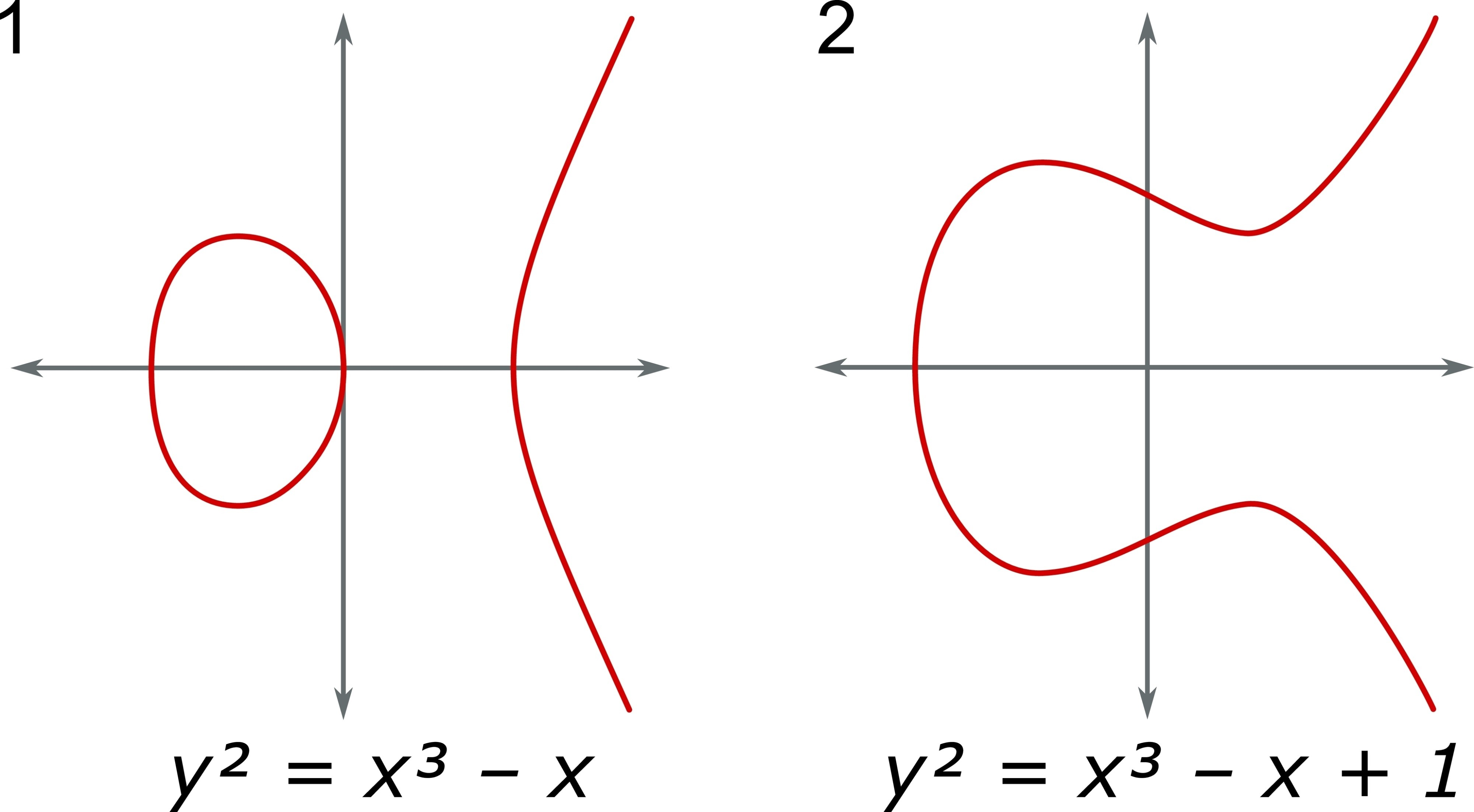
Elliptic Curve Cryptography operates on the geometry of elliptic curves, typically defined by equations of the form y^2 = x^3 + ax + b. In a cryptographic context, these points are restricted to a finite field, meaning that calculations are performed using modular arithmetic. The security of this system relies on the elliptic curve discrete logarithm problem: it is computationally straightforward to perform point multiplication, but it is mathematically infeasible to reverse the operation to find the original scalar.
This asymmetry is what makes the system secure. A private key is simply a randomly selected integer, and the corresponding public key is a point on the curve derived through repeated addition (scalar multiplication). Because the reverse operation—finding the scalar given the public point—would require an impractical amount of computational power, the private key remains protected.
Standardizing Security: The SECP256K1 Curve
Within the ECC blockchain space, one specific curve has become the industry standard: SECP256K1. This curve is defined by the parameters $a=0$ and $b=7$. Its widespread adoption is due to its efficiency and the fact that its parameters were chosen in a way that minimizes potential backdoors, providing a transparent and verifiable mathematical foundation for key generation.
Every time a user generates an address or initiates a transaction, the underlying software is performing operations on this specific curve. This consistency ensures that wallets and exchanges, including those on KuCoin, can interoperate seamlessly. When viewing the KuCoin market data or trading pairs, the integrity of the assets listed is guaranteed by the fact that these mathematical rules are enforced uniformly by the network nodes.
Digital Signatures and Ownership Verification
The process of creating digital signatures is how users authorize transactions. To sign a transaction, a user combines their private key with the transaction data through an ECC algorithm. The resulting signature allows any network node to verify that the message was created by the owner of the associated public key, without ever seeing the private key itself.
How Verification Works:
-
Transaction Creation: The user constructs a message detailing the asset transfer.
-
Signing: The private key is applied to the hash of the message to create a unique signature.
-
Broadcasting: The message and signature are sent to the network.
-
Validation: Nodes use the public key to check if the signature mathematically aligns with the message, confirming the authorization.
ECC and Public Key Infrastructure
The broader Public Key Infrastructure (PKI) in blockchain is essentially a decentralized implementation of traditional cryptographic principles. Unlike traditional PKI, which often relies on a Certificate Authority to verify identity, blockchain-based systems use the ledger itself to manage the relationship between public keys and asset ownership.
-
Decentralization: No central authority manages the keys.
-
Immutability: Once a signature is verified and a transaction is recorded, it cannot be altered.
-
Transparency: Anyone can verify the validity of a signature, but only the holder of the private key can generate one.
For participants interested in the technical nuances of these systems, further reading or research resources are available to explore the evolution of these protocols.
Market Analysis and Cryptographic Integrity
The trust that market participants place in digital assets is effectively a trust in the underlying cryptographic standards. When assessing the market, one might notice that periods of high network activity or protocol upgrades often correlate with an increased focus on security updates. On KuCoin, the trading environment remains stable and secure precisely because these ECC-based signatures prevent unauthorized access or asset duplication.
When analyzing chart patterns or volume spikes on KuCoin, it is useful to remember that every trade executed is a validated cryptographic event. The mathematical stability provided by SECP256K1 is what allows for the high-frequency and high-volume trading seen in the digital asset space without the systemic risk of identity theft or transaction forgery.
Conclusion
Elliptic Curve Cryptography is not merely an abstract mathematical concept; it is the active, functional layer of security that defines the integrity of the blockchain. Through the implementation of the SECP256K1 curve and the deployment of robust digital signatures, this technology ensures that Public Key Infrastructure remains decentralized, transparent, and immutable. As the ecosystem continues to grow, the importance of these cryptographic foundations remains constant. By understanding the math that secures their holdings, traders can better appreciate the technical resilience of the assets they engage with, ensuring they remain informed about the security standards that govern all movements on KuCoin and beyond, including any relevant platform updates or announcements.
Create a free KuCoin account to discover the next crypto gems and trade over 1,000 global digital assets today. Create Now!
FAQs
Why is Elliptic Curve Cryptography used instead of other methods?
ECC offers equivalent security to traditional methods but with much smaller key sizes. This efficiency reduces the computational load and storage requirements for nodes, which is vital for the scalability and performance of blockchain networks.
What is the significance of the SECP256K1 curve?
The SECP256K1 curve is the industry standard for key generation in major blockchain networks. It is chosen for its efficiency and clear parameter definitions, providing a consistent mathematical base that ensures compatibility across wallets and exchanges.
How do digital signatures prove asset ownership?
Digital signatures are created using a private key and the transaction data. Because the signature is mathematically linked to the private key, anyone with the corresponding public key can verify that the transaction was authorized by the owner without the private key ever being revealed.
Can an ECC-secured public key be reversed to find the private key?
No, the security of the system is based on the discrete logarithm problem. It is mathematically infeasible to reverse the scalar multiplication operation, making it impossible to derive a private key from a public key using current computational capabilities.
How does Public Key Infrastructure function in a decentralized system?
In a blockchain, the ledger acts as the source of truth for public keys. The decentralized network replaces the need for a centralized Certificate Authority by allowing any node to verify the mathematical validity of a transaction signature against the associated public key.
Further reading
Disclaimer: The information on this page may have been obtained from third parties and does not necessarily reflect the views or opinions of KuCoin. This content is provided for general informational purposes only, without any representation or warranty of any kind, nor shall it be construed as financial or investment advice. KuCoin shall not be liable for any errors or omissions, or for any outcomes resulting from the use of this information. Investments in digital assets can be risky. Please carefully evaluate the risks of a product and your risk tolerance based on your own financial circumstances. For more information, please refer to our Terms of Use and Risk Disclosure.