Key Insights:
- A flash loan attack exploited a mistaken funds transfer, draining $240,000 in WSEI tokens from the Sei Network.
- Sei Network faces potential issues with USDC.n as the platform transitions to EVM-only in March.
- SEI’s price holds support near $0.12, but broader market trends remain bearish following a steep decline.
A recent flash loan attack on the Sei Network drained roughly $240,000 worth of WSEI tokens from the Synnax contract, according to blockchain security firm BlockSec Phalcon. The attacker borrowed a staggering 1.96 million WSEI tokens through a flash loan and exited without repaying the loan, leaving the funds irrecoverable.
The attack occurred due to an accidental transfer by wallet “0x9748…a714,” which sent funds into the Synnax contract, unintentionally seeding liquidity for the attacker. Two transactions, identified by BlockSec as TX1 and TX2, completed the attack path. The process was straightforward: funds were mistakenly deposited, borrowed via a flash loan, and never returned. This incident highlights how operational mistakes, even on high-performance blockchains like Sei, can lead to significant exploits.
Operational Mistakes Remain a DeFi Risk
This attack serves as a reminder of the recurring vulnerabilities in decentralized finance (DeFi). Despite the robustness of blockchain networks, simple operational errors, such as mistaken transfers, continue to be a pathway for attackers. In this case, the attack was not driven by a flaw in the contract itself, but rather by an unexpected liquidity injection that was exploited by malicious actors.
The timing of the exploit coincides with Sei’s upcoming major network transition. The Sei team has issued a warning to users holding USDC.n, a bridged version of Circle’s USDC used within the Cosmos ecosystem. The planned SIP-3 upgrade, set for March, will convert Sei into an EVM-only chain, which means that Cosmos-native assets, including USDC.n, will no longer be supported. The Sei team has urged users to migrate their assets before the upgrade to avoid potential loss of access or value.
SEI’s Price Faces Bearish Trends
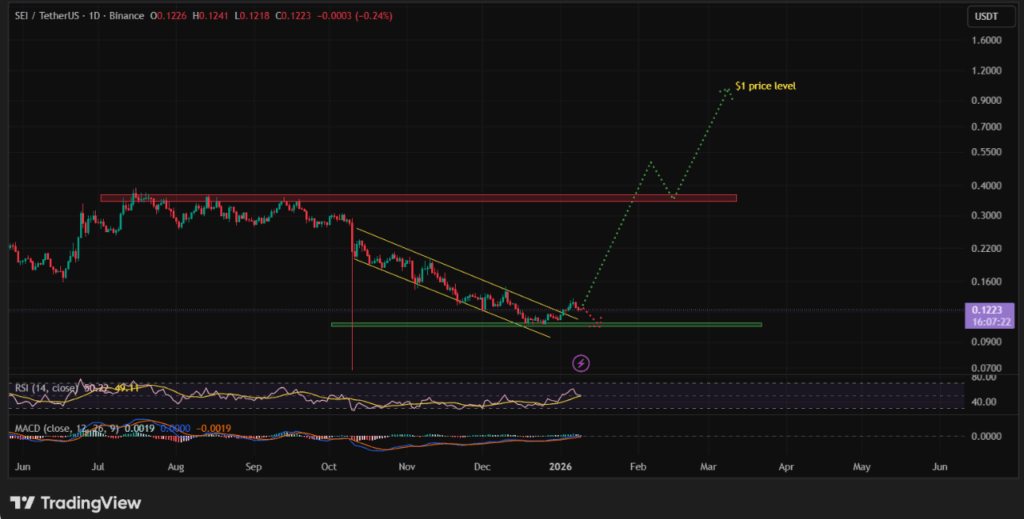
Currently, SEI is trading near $0.12, holding support at a horizontal level that has capped pullbacks since late December. Despite the stabilization, the broader trend remains bearish, as SEI has experienced a significant decline of over 60% from its summer highs. The price movement is showing little momentum for a recovery, with indicators suggesting that the market remains in a consolidation phase. However, as long as SEI holds above $0.11, the risk of further drastic drops is minimized.
A recent flash loan attack drained $240,000 in WSEI from the Sei Network. A mistaken funds transfer created liquidity for the exploit.











