What Is a Sybil Attack? Complete Guide to Detection, Prevention, and Real-World Solutions
In the world of decentralized networks, trust rests on the idea that every participant is exactly who they claim to be. But what happens when one person pretends to be dozens or even thousands of different people at once? That is the heart of a Sybil attack, a clever and persistent threat that has challenged everything from privacy-focused networks like Tor to major blockchain projects and airdrop distributions.
This guide walks through the concept in straightforward terms. You will see exactly how these attacks unfold, the damage they can cause, real examples from recent years, and, most importantly, how teams detect them, stop them before they start, and clean up the mess if one slips through. Whether you run a node, participate in governance votes, or simply hold crypto, understanding Sybil attacks helps protect the integrity of the systems we all rely on.
What Is a Sybil Attack?
A Sybil attack occurs when a single person or small group creates multiple fake identities—often called Sybil nodes or accounts to gain outsized influence within a peer-to-peer network. The name comes from the 1973 book Sybil, which told the story of a woman with multiple personalities. In technology circles, the term took hold after researchers Brian Zill and John R. Douceur highlighted the problem in early peer-to-peer systems around the early 2000s. Douceur’s paper pointed out a basic weakness: without some form of central authority or costly barrier, a network cannot easily tell whether many “separate” participants are actually one clever actor wearing different masks.
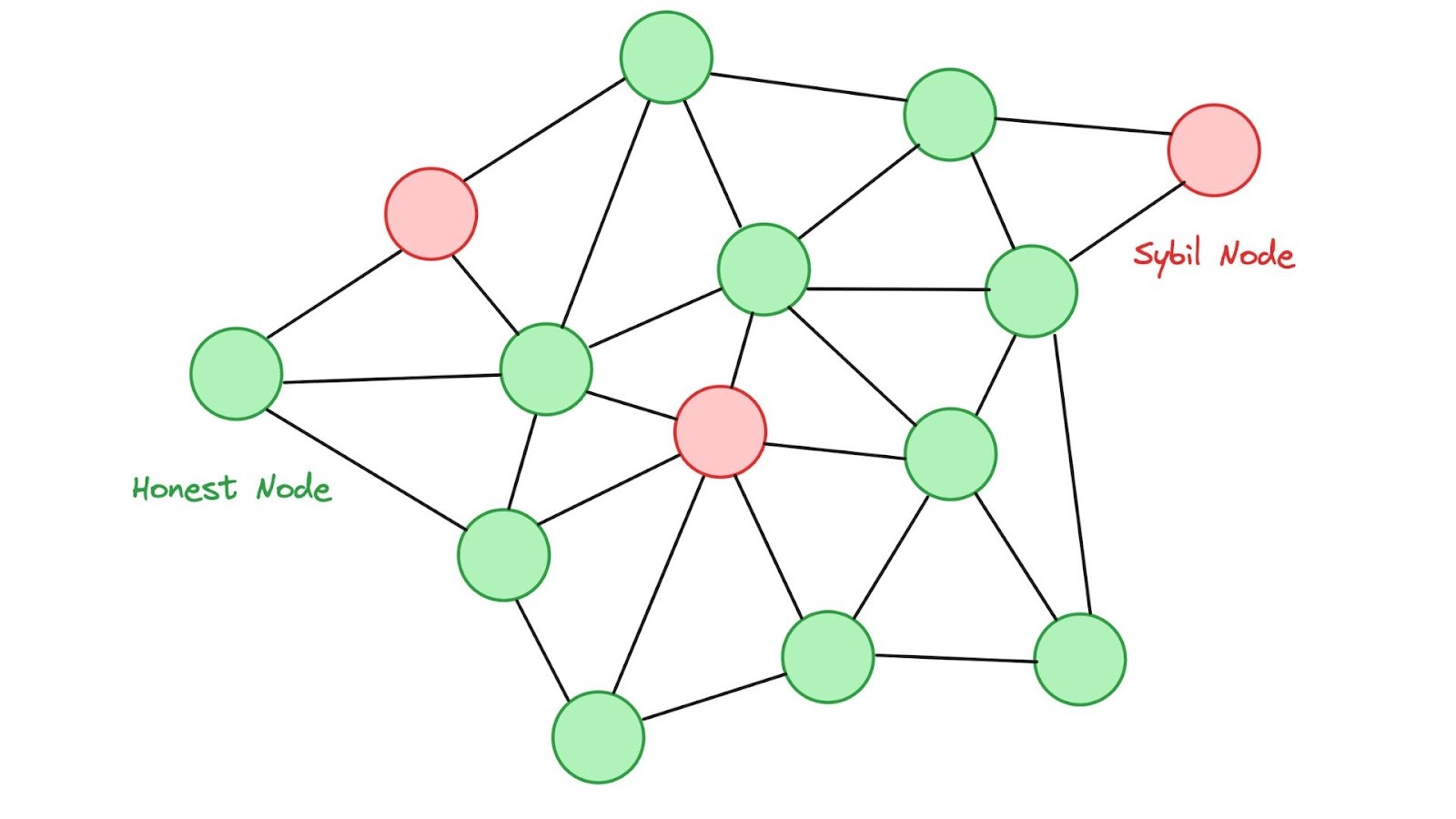
In blockchain terms, the attacker spins up hundreds or thousands of fake wallets, nodes, or validator accounts. These fakes behave normally at first; maybe they relay transactions honestly or earn small reputation points, so the network treats them as legitimate community members. Once the attacker has enough fake identities in place, they flip the script. They might outvote honest participants in a governance proposal, censor certain transactions, or even attempt a 51% attack to rewrite recent history on the chain.
Think of it like a small town where one resident shows up to the community meeting with a hundred fake IDs and votes on every issue. The system looks democratic on paper, but the outcome is anything but fair.
How Sybil Attacks Actually Work
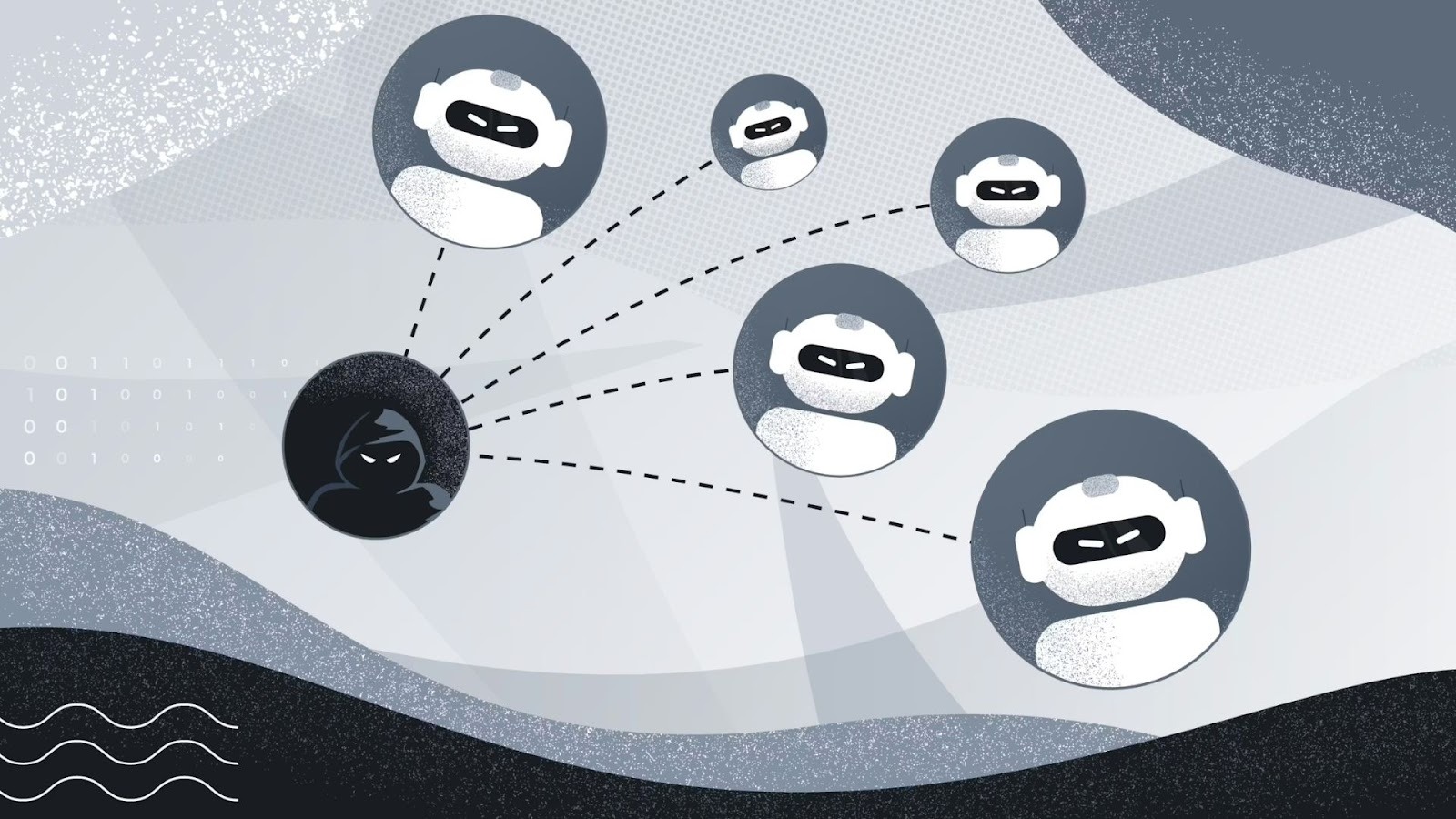
Sybil attacks come in a few different flavors, yet they all rely on one simple trick: flooding a network with fake identities that cost almost nothing to create. The attacker doesn’t need advanced hacking skills in most cases, just the ability to generate and manage multiple accounts that appear to be ordinary users or nodes.
Direct vs Indirect Attacks
Direct attacks happen when the fake nodes communicate directly with honest ones. The genuine participants have no straightforward way to tell whether the newcomer is fake, so they accept the newcomer's data, votes, or blocks at face value. These attacks can spread influence quickly because there is no buffer between the attacker and the rest of the network.
Indirect attacks are sneakier.
Instead of connecting directly, the attacker routes influence through middleman nodes, sometimes compromised relays, sometimes completely innocent ones. Honest nodes never interact with the original malicious source, making the attack much harder to trace and detect. The bad information travels through these proxies, slowly poisoning decisions or consensus without raising immediate red flags.
The Attacker’s Typical Playbook
In practice, most Sybil attacks follow a clear three-step process that feels almost routine once you see the pattern.
First comes identity creation. The attacker generates dozens, hundreds, or even millions of wallet addresses using automated tools that make the process cheap and fast. On many blockchains, creating a new address requires almost no resources, which is exactly why the attack works so well at first.
Next is reputation building. The fake identities don’t act maliciously right away. Instead, they behave like normal participants sending small transactions, staking tiny amounts of tokens, or simply relaying data across the network. This phase can last days or weeks, allowing the Sybil nodes to earn trust points, build on-chain history, and blend in with legitimate users.
Finally comes the power grab. Once the fake identities reach a critical mass, the attacker flips the switch. They use this manufactured majority to influence consensus mechanisms, sway governance votes, censor transactions, or manipulate data flows. On proof-of-work chains, the attacker might try to control enough hash power simply by running large numbers of low-power nodes. On proof-of-stake networks, they spread minimal stakes across many separate accounts to avoid triggering economic safeguards. In airdrop farming, the goal is simpler and more direct: claim rewards multiple times by pretending to be many different users at once.
This layered approach explains why Sybil attacks remain effective even on seemingly secure networks. The early stages look completely normal, so detection tools often miss them until the damage is already underway. Understanding these steps helps teams design better defenses and gives everyday users a clearer picture of what to watch for when participating in new protocols or incentive programs.
The Real Damage: Impacts on Blockchain Networks
The consequences go far beyond inconvenience. A successful Sybil attack can undermine the three pillars most blockchains promise: security, decentralization, and privacy.
51% Attacks and Double-Spending
One of the most feared outcomes is the classic 51% attack combined with double-spending. If malicious nodes manage to control more than half of the network’s resources, whether through computing power in proof-of-work systems or staked tokens in proof-of-stake, the attacker gains the ability to reorder or even reverse recent transactions.
This breaks the fundamental promise of blockchain finality. Ethereum Classic experienced this painfully in 2020, when an attacker leveraged majority hash power to execute sophisticated double-spends, ultimately stealing over $5 million in ETC. The incident reminded everyone how vulnerable smaller or less secure chains can become when Sybil-style control is achieved.
Censorship and Network Fragmentation
Beyond outright theft, Sybil attacks enable powerful censorship and network fragmentation. Attackers can simply refuse to forward blocks or transactions from honest users, effectively silencing parts of the community. In more advanced forms, they isolate specific nodes and feed them false information, an “eclipse attack” variant.
The targeted node believes it is still connected to the wider network, but in reality, it operates inside a manipulated bubble. This kind of isolation can delay confirmations, distort market data, or prevent users from seeing the true state of the chain, quietly undermining confidence without triggering immediate alarms.
Privacy Breaches
Privacy-focused networks feel the pain especially sharply. In systems like Tor or privacy-oriented coins such as Monero, an attacker who controls many entry and exit nodes can begin linking IP addresses to specific transactions. This directly attacks the anonymity that users expect. Monero faced exactly this kind of 10-day assault in November 2020. The goal was straightforward: deanonymize users by observing traffic patterns across the malicious nodes.
Although the network’s Dandelion++ protocol helped limit the damage, the attempt itself highlighted how Sybil tactics can turn a strength, decentralized routing, into a serious weakness when enough fake participants join the mix.
Governance Manipulation
Decentralized Autonomous Organizations (DAOs) are particularly exposed because they often rely on token-weighted voting or one-person-one-vote systems. When an attacker floods the ecosystem with Sybil wallets, they can sway proposals in their favor.
Harmful upgrades might pass, treasury funds could be redirected, or legitimate community voices could be drowned out. The result is not just a bad decision today but a long-term erosion of faith in the governance process itself. Users start wondering whether their vote or anyone else’s actually counts.
Airdrop and Incentive Abuse
Projects that try to reward genuine users see their token distributions hijacked. In 2025, blockchain analytics firm Bubblemaps flagged roughly 100 linked wallets on the MYX Finance airdrop that claimed about 9.8 million tokens valued at around $170 million at the time, allegedly from a single entity.
LayerZero’s 2024 airdrop provided another high-profile case. The team, working with Nansen and Chaos Labs, identified more than 800,000 addresses as Sybils, about 13% of eligible wallets. They even ran a self-reporting program and bounty system to encourage honesty, turning the fight into an ongoing game of cat and mouse.
These incidents show how Sybil attacks do not just steal funds; they erode confidence in the entire ecosystem.
Real-World Examples That Changed the Game
History offers clear lessons. The 2014 Tor network attack saw one operator run 115 relays from a single IP address, giving them unusual sway over traffic routing and user de-anonymization. A similar but more targeted attack hit Tor again in 2020, focusing on Bitcoin users routing through the network.
On the blockchain, Verge’s 2021 51% attack wiped roughly 200 days of transaction history, but the team recovered within days. Ethereum Classic’s repeated struggles in 2020 highlighted how smaller chains with lower hash rates remain tempting targets.
Airdrop farming has become the most visible modern battleground. Projects now routinely publish Sybil reports, partner with analytics firms, and experiment with bounty programs. The MYX Finance case in 2025 raised eyebrows because the scale of nearly $170 million allegedly funneled through a small cluster suggested either sophisticated automation or, as some speculated, an inside job.
The team pushed back, emphasizing that most rewards went to legitimate traders and liquidity providers, while admitting the need for stronger filters in future incentive programs.
These stories prove one thing: no network is immune, but the best teams treat Sybil resistance as an ongoing process rather than a one-time fix.
Detecting Sybil Attacks Before They Cause Harm
Detection is half the battle. Teams look for patterns that no genuine user would show:
-
IP and address correlation: Many nodes or wallets sharing the same IP range or funded from the same exchange wallet in quick succession.
-
Behavioral analysis: Clusters of accounts that interact only with each other, perform identical low-value transactions, or activate at the exact same times.
-
Social trust graphs: Algorithms like SybilRank, SybilGuard, or newer graph neural networks map how nodes connect. Honest communities tend to form dense, interconnected webs; Sybil clusters look like isolated islands with few genuine links.
-
Machine learning and on-chain forensics: Tools from firms like Nansen or Bubblemaps scan transaction graphs for suspicious clusters. In the Linea airdrop analysis, Nansen flagged nearly 40% of addresses as Sybils after adjusting thresholds to spare smaller legitimate multi-wallet users.
Advanced research even explores decentralized federated learning, where nodes train detection models together without sharing raw data to spot anomalies in real time while preserving privacy.
Prevention Strategies That Actually Work
The strongest defenses make it expensive or impossible to create fake identities.
Consensus Mechanisms as the First Line of Defense
Consensus mechanisms form the foundational protection for most blockchains. Proof-of-Work, as used by Bitcoin, demands real computing power to create and maintain nodes. An attacker cannot simply spin up thousands of low-effort identities because each one requires actual hardware and electricity. This economic reality has kept large-scale Sybil attacks rare on mature PoW networks.
Proof-of-Stake, seen prominently in Ethereum, raises the bar even higher by requiring participants to lock up valuable tokens. At one point, becoming a validator demanded 32 ETH per node, an amount that made running dozens of separate identities financially painful for most attackers. The risk of losing that staked capital for dishonest behavior adds another powerful deterrent.
Delegated Proof-of-Stake introduces yet another layer. Instead of allowing unlimited nodes, communities elect a smaller group of trusted delegates to handle validation. These delegates have strong incentives to act honestly because their position and rewards depend on community support, making it much harder for Sybil nodes to gain meaningful influence.
Proof-of-Personhood and Identity Verification
Some projects go beyond economic costs and tackle the identity problem directly through Proof-of-Personhood. Worldcoin, for example, uses biometric iris scans to verify that each account belongs to one unique human. This approach aims to enforce a true “one person, one vote” system.
KYC requirements or simple phone verification add noticeable friction for users, but they dramatically raise the cost of farming fake accounts. While these methods spark debate around privacy, they remain highly effective at limiting the sheer volume of Sybil identities an attacker can create.
Reputation Systems and Hierarchical Controls
Reputation and hierarchical systems introduce time and behavior as additional defenses. New nodes are treated with suspicion until they prove themselves. Long-standing participants gradually earn higher voting power, priority in governance, or greater influence across the network.
This structure prevents brand-new fake identities from immediately causing damage.
Social trust graphs and vouching systems take this further. Established members must effectively “endorse” newcomers through visible on-chain connections. Algorithms analyze how nodes relate to one another, making it easier to spot and limit isolated clusters of suspicious accounts.
Custom Tools and Multi-Layered Approaches
Developers also deploy specialized custom tools tailored to specific networks. Distributed hash tables like Kademlia, used by the Invisible Internet Project (I2P), make it technically difficult to flood the network with coordinated fake nodes. Smart-contract-based reputation scoring can automatically slash stakes or reduce influence when bad behavior is detected.
In practice, the most resilient projects do not rely on any single method. They combine several layers of economic costs from consensus mechanisms, identity checks through Proof-of-Personhood or KYC, reputation building over time, and custom technical barriers. The guiding principle remains consistent: honest participation should remain cheap and easy, while attempts at malicious scale become prohibitively expensive in terms of money, time, or technical complexity.
This multi-layered philosophy explains why mature networks have grown increasingly resistant to Sybil attacks over the years. Each new threat prompts refinements, turning prevention into an evolving practice rather than a static checklist.
How to Solve a Sybil Attack Once It Has Already Happened
Even the best defenses can be tested. When an attack slips through, speed and transparency matter.
-
Immediate filtering and exclusion: Teams analyze on-chain data to blacklist linked clusters. In airdrops, this means removing Sybil wallets before distributing tokens. LayerZero’s public list and ongoing bounty program showed how community involvement can accelerate cleanup.
-
Emergency governance pauses: If a vote appears manipulated, projects can pause proposals, review evidence, and reverse decisions. Some protocols temporarily hand control back to a trusted multisig or core team while the dust settles.
-
Raising the economic bar: After an incident, teams may raise staking requirements or add new collateral rules to make future attacks costlier.
-
Reputation resets and vouching: New or suspicious nodes lose voting rights until they prove themselves over time. Established nodes can indirectly vouch for others through graph-based trust scores.
-
Protocol patches: Nodes can reject connections from duplicate IPs, enforce geographic diversity, or implement inbound connection limits. Post-attack audits often reveal simple fixes, such as better random node selection.
The process feels like a game of cat and mouse, but each round makes the network smarter. Real recovery also involves clear communication, publishing findings, explaining decisions, and sometimes compensating affected users, to rebuild trust.
Challenges and Considerations for the Road Ahead
No solution is perfect. Strong identity checks can clash with crypto’s privacy ethos. Biometric proof-of-personhood raises accessibility and data-privacy questions. Overly aggressive filtering might exclude legitimate users who simply run multiple wallets.
Smaller or newer chains remain more vulnerable because they lack the hash rate or economic depth of Bitcoin or Ethereum. Airdrop culture itself creates incentives for farming, turning every token launch into a potential target.
Emerging threats include AI-powered automation that mimics human behavior more convincingly. On the bright side, 2025 and 2026 have seen rapid progress in machine-learning detection, decentralized reputation systems, and hybrid approaches that blend economic costs with social graphs.
Investors and users can protect themselves by supporting projects that publish clear Sybil-defense roadmaps, use battle-tested consensus, and engage third-party auditors. Holding assets in hardware wallets and avoiding suspicious links remains basic but essential hygiene.
Conclusion
Sybil attacks remind us that decentralization is not automatic; it requires constant vigilance. From the early days of Tor to the sophisticated airdrop battles of 2024–2025, these attacks have exposed weaknesses but also driven innovation. Projects that treat Sybil resistance as a living system combining costly participation, smart detection, community tools, and quick recovery plans stand the best chance of staying resilient.
As blockchain moves deeper into everyday finance, governance, and even real-world applications like industrial IoT, the ability to separate genuine participants from clever impostors will define which networks thrive. The good news? The tools exist, the lessons are public, and the community keeps learning. Staying informed is the first step toward keeping the network honest.
If you found this guide helpful, explore more on blockchain security or share your own experiences with Sybil filtering in the comments. For hands-on protection, consider hardware wallets and follow projects that prioritize transparency around incentives and governance. Stay curious, stay secure, and keep building on solid foundations.
Frequently Asked Questions
1. Are all blockchains vulnerable to Sybil attacks?
Every peer-to-peer network faces the risk in theory, but mature chains using proof-of-work or proof-of-stake make large-scale attacks extremely expensive. Smaller or low-security networks remain more exposed.
2. How do you detect a Sybil attack?
Look for clusters of wallets or nodes that share funding sources, exhibit identical behavior, or lack genuine social trust connections in social trust graphs. Analytics firms and graph algorithms do the heavy lifting.
3. What is the difference between direct and indirect Sybil attacks?
Direct attacks involve fake nodes talking straight to honest ones. Indirect attacks route influence through middle nodes, making the original attacker harder to trace.
4. Can proof-of-stake fully prevent Sybil attacks?
It raises the cost dramatically because each identity needs real stake at risk, but clever attackers can still spread small stakes across many accounts unless additional layers like reputation or personhood checks are added.
5. What happened in the LayerZero airdrop Sybil case?
The team identified over 800,000 suspicious addresses using analytics partners and community reporting, then adjusted distributions to reward genuine users.
6. How do projects recover after a successful attack?
They blacklist malicious nodes, pause governance, revert bad decisions if possible, and patch the protocol. Clear communication helps restore community trust.
7. Is KYC the only way to stop Sybil attacks?
No. While effective, it sacrifices privacy. Many projects prefer hybrid approaches that balance security and decentralization through economic costs, reputation systems, and graph analysis.
8. What should users watch for to avoid being part of a Sybil scheme?
Be wary of “farming guides” that promise easy rewards through dozens of wallets. Legitimate participation usually looks like normal, varied activity rather than scripted repetition.
Risk Disclaimer: This content is for informational purposes only and does not constitute financial, investment, or legal advice. Cryptocurrency investments carry significant risk and volatility. Always conduct your own research and consult a qualified professional before making any financial decisions. Past performance does not guarantee future results or returns.