KelpDAO rsETH Exploit: How The $292M LayerZero Bridge Attack Created $177M Bad Debt on Aave
2026/04/20 18:30:03
Introduction
What happens when a single point of failure in a cross-chain bridge becomes a $292 million problem?
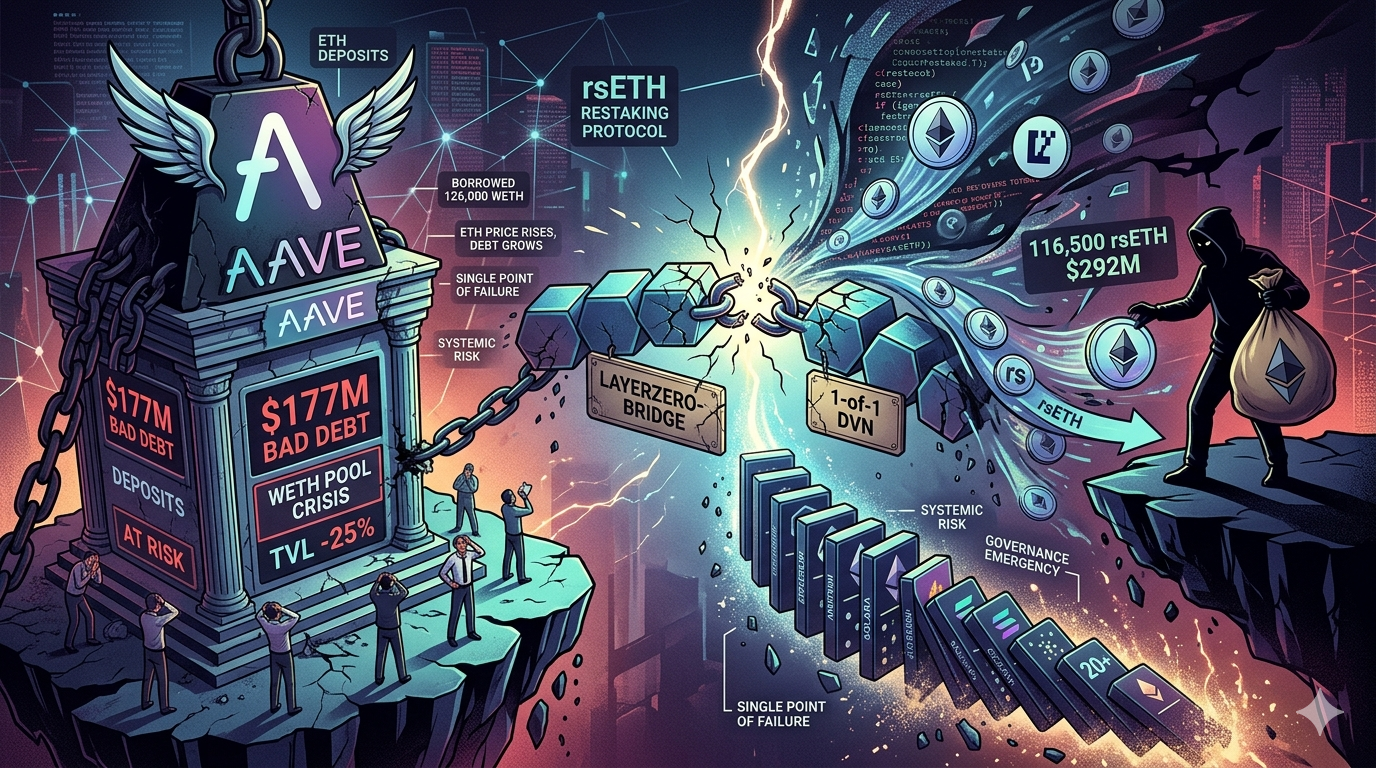
On April 18, 2026, the cryptocurrency industry got its answer in real time. KelpDAO, a liquid restaking protocol, was drained of 116,500 rsETH worth approximately $292 million through a vulnerability in its LayerZero-powered bridge. The attack didn’t just steal tokens - it created an estimated $177 million in bad debt that now sits on Aave’s books, leaving depositors scrambling and the DeFi community asking whether the era of cross-chain finance has a fundamental trust problem.
What is KelpDAO and rsETH? Understanding the Liquid Restaking Space
KelpDAO is a liquid restaking protocol built on EigenLayer, allowing users to stake their ETH through the protocol and receive rsETH (restaked ETH) as a liquid token representing their staked position. This concept - liquid restaking - lets users maintain liquidity while still earning staking rewards, combining the yield of native staking with the flexibility of a tradeable token.
The rsETH token became popular because it could be used across DeFi protocols as collateral. Users stake ETH through KelpDAO, receive rsETH, then use that rsETH to borrow other assets across multiple chains. The problem? This cross-chain functionality relied on LayerZero’s bridge technology, specifically a 1-of-1 DVN (Data Verification Network) configuration that turned out to be a single point of failure.
For newcomers to DeFi, the concept is straightforward. KelpDAO promised users could earn staking rewards while their ETH remained usable in other protocols. The execution relied on trust in bridge infrastructure - trust that collapsed on April 18 when a single compromised validator allowed the attacker to mint unbacked rsETH. The attacker didn’t hack the blockchain itself - they manipulated the message verification system that tells one chain the token exists on another.
The April 18, 2026 Exploit: How the Attack Unfolded
The exploit unfolded in phases over approximately 46 minutes, according to incident reports. Starting at 18:52 UTC on April 18, 2026, the attacker exploited a flaw in KelpDAO’s LayerZero bridge configuration - specifically, the 1/1 DVN (single signer verification) that validated cross-chain messages.
Here’s what happened technically:
| Phase | Action | Impact |
| 1 | Attacker identifies 1-of-1 DVN vulnerability | Single point of failure exposed |
| 2 | Mints 116,500 unbacked rsETH | ~18% of circulating supply |
| 3 | Bridges rsETH across 20+ chains | Assets stranded globally |
| 4 | Deposits rsETH as collateral on Aave V3 | Borrows 126,000 WETH |
| 5 | Executes exit before emergency pause | $292M stolen |
The attacker supplied the stolen rsETH as collateral on Aave V3 and borrowed approximately 126,000 WETH (worth approximately $236 million at the time). This created immediate bad debt - Aave now holds rsETH worth far less than the WETH it lent out.
Security researchers noted that a 46-minute window existed between when suspicious activity began and when the protocol paused. Had the pause occurred sooner, an additional $200 million in potential bridged assets could have been prevented. The delay proved costly.
The Aave Bad Debt Crisis: $177M and Counting
The exploit’s aftermath created a crisis far larger than the initial theft. Aave’s WETH pool now holds approximately $177 million in bad debt - the attacker borrowed 126,000 ETH using stolen rsETH as collateral, and that debt is now fixed in ETH terms while the collateral has collapsed in value.
The math is stark. When the attacker supplied rsETH as collateral, they knew it was unbacked. Aave saw it as valid collateral worth approximately $2,500 per rsETH. The attacker walked away with real WETH. Aave is left holding rsETH that is now essentially worthless as collateral.
Aave’s governance responded quickly:
-
Paused all new rsETH deposits across V3 markets
-
Activated the Aave Guardian emergency powers
-
Started governance discussions about bad debt recovery
-
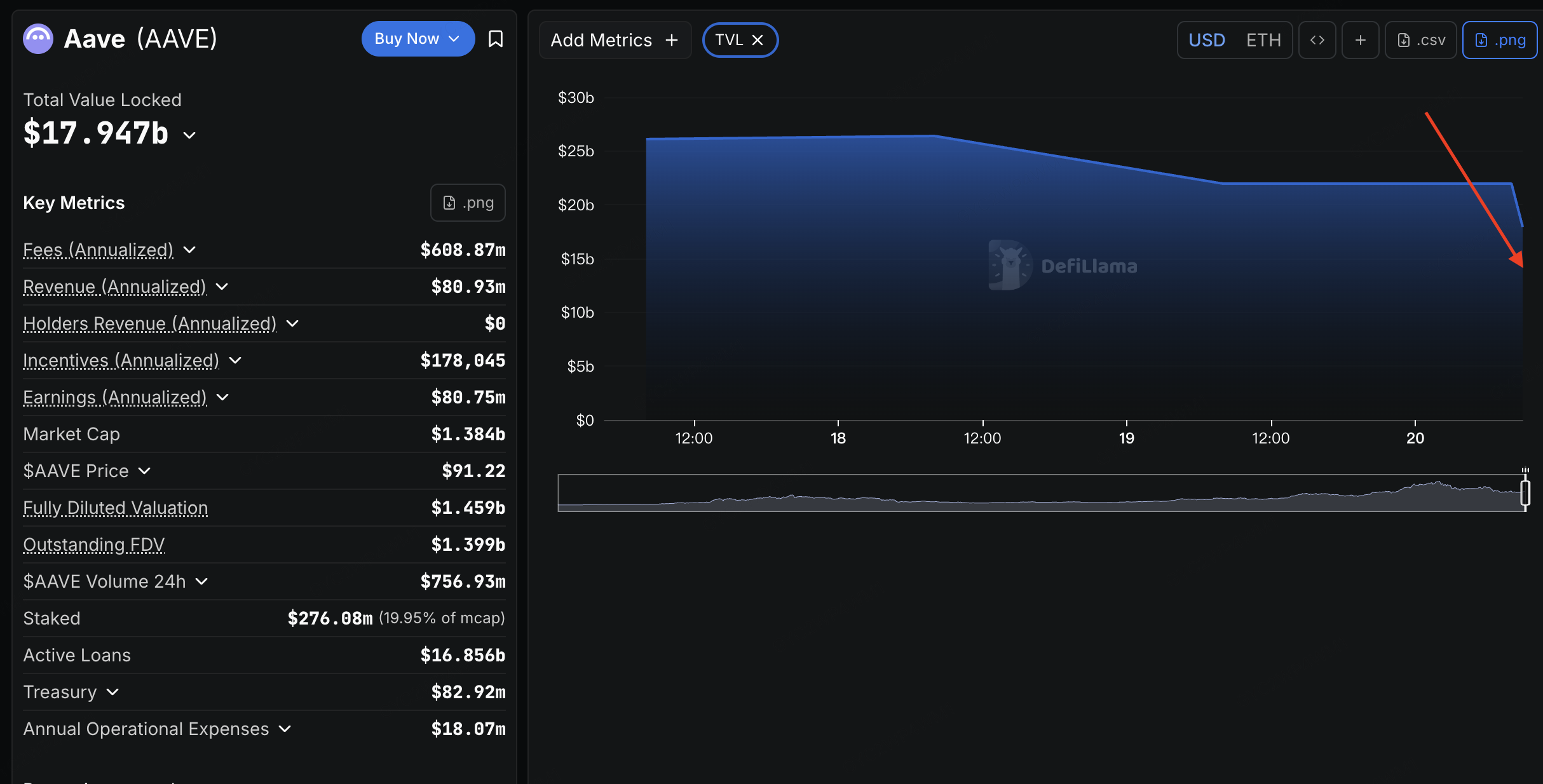
Aave TVL dropped from $26.4 billion to $20.7 billion - a 25% decline in total value locked
For WETH depositors on Aave, the situation is precarious. The bad debt means depositors’ funds are at risk if recovery doesn’t occur. Aave governance is exploring recovery options through the Umbrella protocol and the Aave treasury, but no clear solution has emerged as of this writing.
The attacker borrowed over 82,600 ETH (approximately $195 million) from Aave using the stolen rsETH, creating bad debt that continues to compound as ETH price appreciation makes the debt more difficult to cover through treasury reserves.
Cross-Chain Bridge Vulnerabilities: A Systemic Problem
The KelpDAO exploit is not an isolated incident - it’s the largest DeFi hack of 2026 to date, following a pattern of bridge vulnerabilities that have plagued the industry. From 2022’s Ronin Bridge ($625M) to 2023’s Multichain, cross-chain bridges have consistently proven to be the weakest link in DeFi infrastructure.
The fundamental issue is architectural. Cross-chain bridges require trust in message verification systems. When a bridge tells Chain B that a token exists on Chain A, that message is only as trustworthy as the verification mechanism. The KelpDAO attack exploited a 1-of-1 DVN configuration - a single point of failure that should never have been deployed for a protocol managing hundreds of millions in user funds.
Industry responses have been mixed, but the pattern is clear:
| Year | Incident | Loss | Root Cause |
| 2022 | Ronin Bridge | $625M | Private key compromise |
| 2023 | Multichain | $130M | Multi-sig failure |
| 2024 | Various bridges | $400M+ | Multiple |
| 2026 | KelpDAO | $292M | 1-of-1 DVN failure |
The KelpDAO case is particularly concerning because the vulnerability was known in LayerZero’s architecture but was not addressed at the protocol level until after damage occurred.
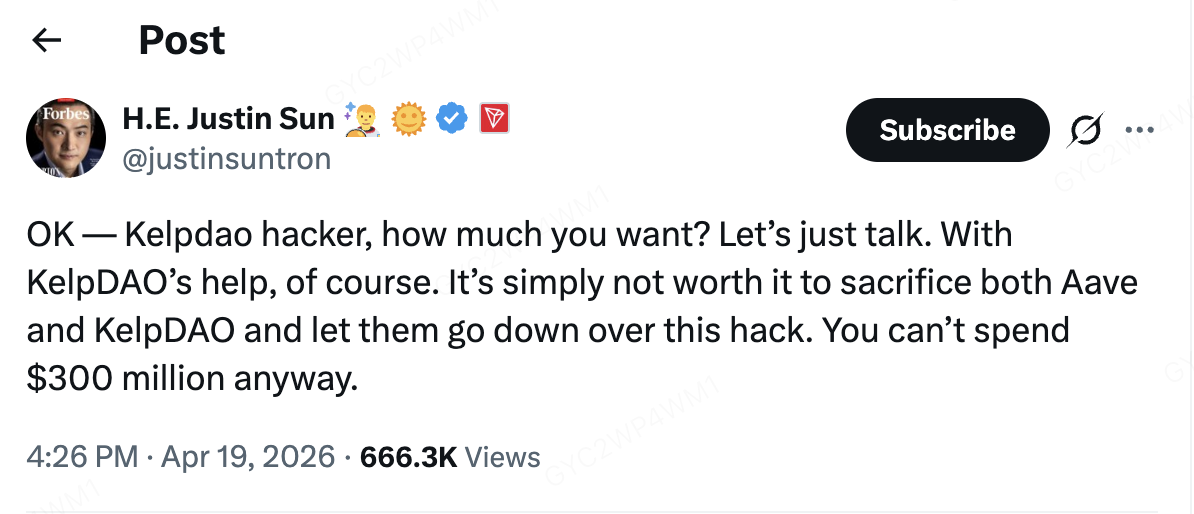
Justin Sun’s Intervention and Recovery Efforts
In an unusual move, TRON founder Justin Sun publicly offered to negotiate with the KelpDAO attacker. Sun posted on X (formerly Twitter), “KelpDAO hacker, how much do you want? Let’s just talk. It’s simply not worth it to sacrifice both Aave and KelpDAO and let them go down over this hack.”
The attacker borrowed approximately 126,000 ETH, creating debt fixed in ETH terms. As ETH price increases, so does the debt burden on Aave’s treasury and Umbrella protocol. Sun’s intervention reflected the broader ecosystem’s concern - this wasn’t just about KelpDAO or Aave, it was about preventing a systemic crisis that could affect lending markets across DeFi.
The stolen rsETH has been flagged and frozen on multiple networks. The attacker controls significant ETH but cannot easily exit positions without triggering freezes and investigations. This creates a standoff - the attacker has value on paper but cannot realize it without cooperation.
Should I Invest in AAVE on KuCoin After the rsETH Exploit?
This is the question on every DeFi investor’s mind following the KelpDAO incident. Aave is the largest lending protocol in DeFi, and this exploit exposed vulnerabilities that many thought were resolved. Here’s the honest assessment.
Reasons for Caution
-
Bad debt uncertainty: $177M in bad debt sits on Aave’s WETH pool, and recovery timeline is unclear
-
TVL decline: 25% TVL drop signals eroding confidence
-
Cross-chain risk: Aave uses third-party bridges for cross-chain assets - any bridge vulnerability creates exposure
-
Governance uncertainty: Recovery proposals are still being discussed, with no guaranteed outcome
-
Market sentiment: AAVE price dropped approximately 10% as the market priced in potential losses
Reasons to Consider AAVE
-
Market leader position: Despite the exploit, Aave remains the dominant lending protocol
-
Recovery potential: The Aave treasury and Umbrella protocol have resources to partially cover losses if properly implemented
-
DeFi necessity: Lending protocols are foundational - demand exists regardless of individual protocol issues
-
Historical resilience: Aave has survived previous exploits and market crises
-
Governance response: Quick pausing and governance activation show crisis response capability
Risk Assessment Summary
The KelpDAO exploit represents a new era of DeFi risk - cross-chain vulnerabilities that affect not just the bridge user but anyone providing collateral to exposed protocols. For Aave, the direct impact is approximately $177M in bad debt against $20.7B in remaining TVL, roughly 0.85% of total deposits at risk.
The key question: Can you tolerate this level of protocol risk? If you’re depositing into Aave, understand you’re exposed to the collateral choices of other borrowers. The attacker exploited Aave’s collateral system, not a direct deposit vulnerability, but the effect on depositors is similar - their funds are now at risk during recovery negotiations.
How to Trade AAVE on KuCoin
For those deciding to trade AAVE on KuCoin following the exploit, here’s the practical guide.
Step 1: Understand the Risk
AAVE is experiencing significant volatility following the exploit. Price could move 10-20% in either direction based on recovery news. Only trade with capital you can afford to lose or hold through extended volatility.
Step 2: Execute Your Trade
On KuCoin, search “AAVE/USDT” in the trading interface. Trading volumes are high during this period, providing liquid markets for both market and limit orders.
Step 3: Consider Position Sizing
Given ongoing uncertainty, consider smaller position sizes than normal. The 10% price drop already occurred, but recovery timeline remains uncertain. Dollar-cost averaging into positions over time reduces timing risk.
Conclusion
The KelpDAO rsETH exploit stands as 2026’s largest DeFi incident - not just for the $292M theft, but for what it reveals about cross-chain infrastructure. A single validator allowed the attacker to mint unbacked tokens across 20+ chains, then use them as collateral on Aave.
The $177M bad debt now sitting on Aave highlights DeFi’s systemic risk chains. Protocol composability benefits users but also creates failure modes that cross-protocol boundaries. Cross-chain bridges remain the industry’s weakest link until architectural reforms address single-point-of-failure configurations.
For DeFi participants, the lesson isn’t abandoning the space - it’s understanding risks more precisely. The attacker holds $292M in flagged assets they cannot easily liquidate. For Aave specifically, recovery involves governance-funded mechanisms with no guaranteed timeline. The protocol has survived previous challenges, but this incident exposed limitations requiring ongoing structural response.
FAQs
Q: Is my ETH safe on Aave after the KelpDAO exploit?
A:$177M in bad debt exists on Aave’s WETH pool, but this represents less than 1% of total TVL ($20.7B). Governance is actively discussing recovery options. Monitor Aave governance announcements for updates on recovery timelines and mechanisms.
Q: What happened to the stolen rsETH?
A:$292M in rsETH remains flagged across chains. The attacker cannot easily liquidate these assets without triggering freezes. Justin Sun publicly offered to negotiate with the attacker for return of funds.
Q: Who is responsible for the KelpDAO exploit?
A:Technical analysis points to exploitation of LayerZero’s 1-of-1 DVN configuration. This allowed the attacker to forge cross-chain messages and mint unbacked rsETH. The vulnerability was in KelpDAO’s bridge setup, not LayerZero’s core protocol.
Q: Will Aave recover the $177M bad debt?
A:Aave governance is exploring recovery through the Umbrella protocol and treasury reserves. No confirmed timeline exists yet. The attacker borrowed 126,000 ETH against unbacked collateral - recovery requires either hacker cooperation or governance-funded coverage.
Q: Should I avoid DeFi after this exploit?
A:The KelpDAO exploit reveals cross-chain risks but doesn’t indicate all DeFi protocols are unsafe. Understand your exposure to cross-chain assets and audit the bridge configurations of protocols you use. Diversification across protocols and careful position sizing remain prudent strategies.