X Chat will be available for download on the App Store this Friday. Media outlets have already gone through the feature list—self-destructing messages, screenshot blocking, 481 group chats, Grok integration, and registration without a phone number—and have widely labeled it the "Western WeChat." But three issues have scarcely been clearly addressed in any coverage.
On X's official help page, there is a statement that remains posted on X's help website to this day: "If a malicious insider or X itself is compelled by legal process to expose encrypted conversations, neither the sender nor the recipient will be notified."
Question 1: Is this encryption the same as Signal's encryption?
No. The difference lies in where the key is stored.
Signal’s end-to-end encryption ensures that your keys never leave your device. Neither X, nor courts, nor any external party holds your keys. Signal’s servers have no means to decrypt your messages—they can only provide registration timestamps and last connection times when served with a subpoena, as proven by historical subpoena records.
X Chat uses the Juicebox protocol. This system splits the key into three parts, each stored on one of three servers operated by X. When recovering the key with a PIN code, the system retrieves these three shards from X’s servers and reassembles them. Regardless of the PIN’s complexity, the key is ultimately held by X, not the user.
This is the technical background behind "that line on the help page": because the keys are stored on X’s servers, X has the ability to comply with legal requests without the user’s knowledge. Signal does not have this ability—not due to policy, but because it does not possess the keys in the first place.
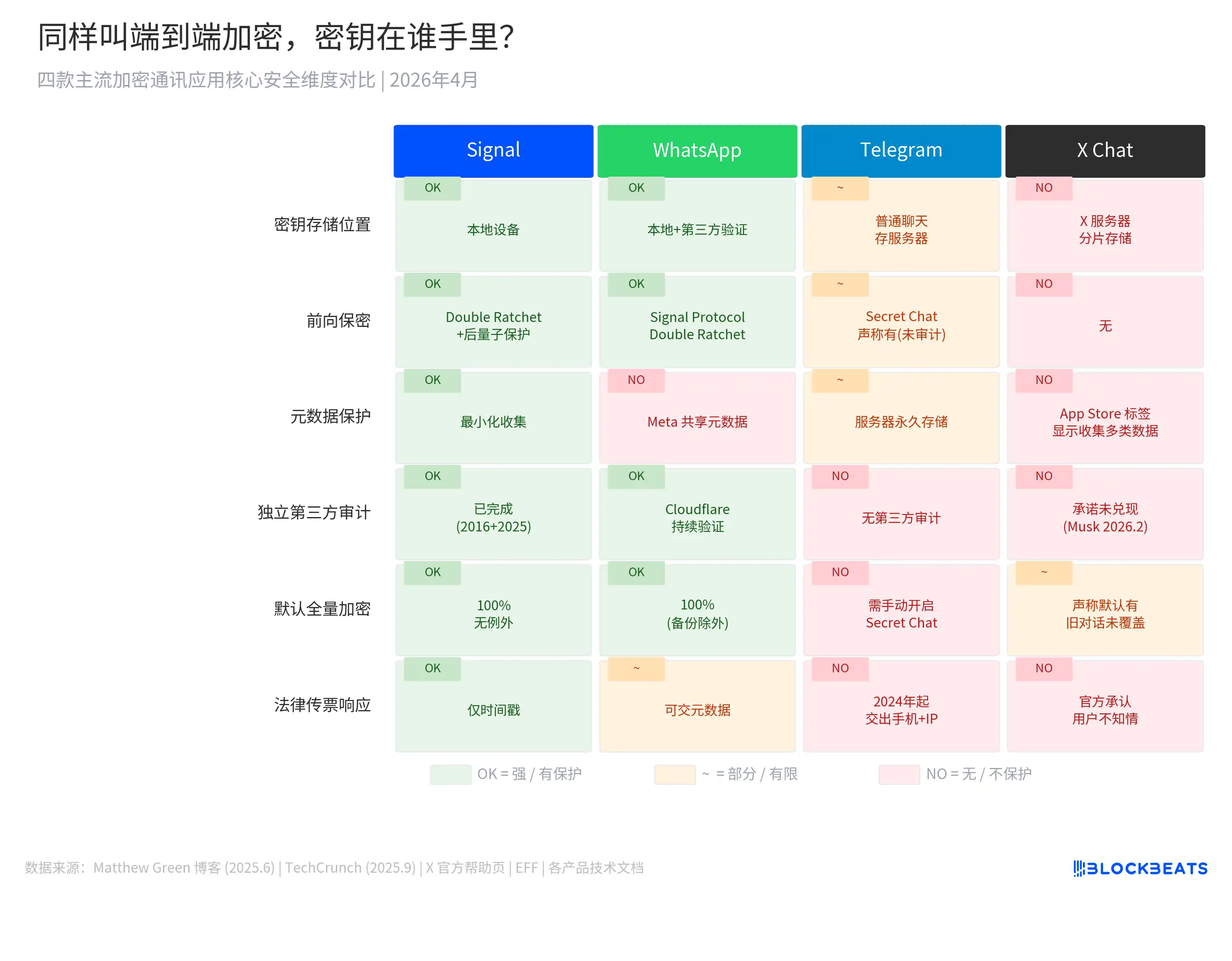
The chart above compares the security mechanisms of Signal, WhatsApp, Telegram, and X Chat across six dimensions. X Chat is the only one among the four where the platform holds the keys and the only one without forward secrecy.
Forward secrecy ensures that even if a key from a specific point in time is compromised, past messages cannot be decrypted, because each message uses a unique key. Signal’s Double Ratchet protocol automatically updates the key after each message, but X Chat does not have this mechanism.
Matthew Green, a cryptography professor at Johns Hopkins University, analyzed the XChat architecture in June 2025 and stated: "If we judge XChat as an end-to-end encryption scheme, this seems like a pretty game-over type of vulnerability." He later added, "I would not trust this any more than I trust current unencrypted DMs."
From the TechCrunch report in September 2025 to its launch in April 2026, this architecture remained unchanged.
On February 9, 2026, Musk tweeted a commitment to conduct rigorous security tests of X Chat and open source all the code before its release.
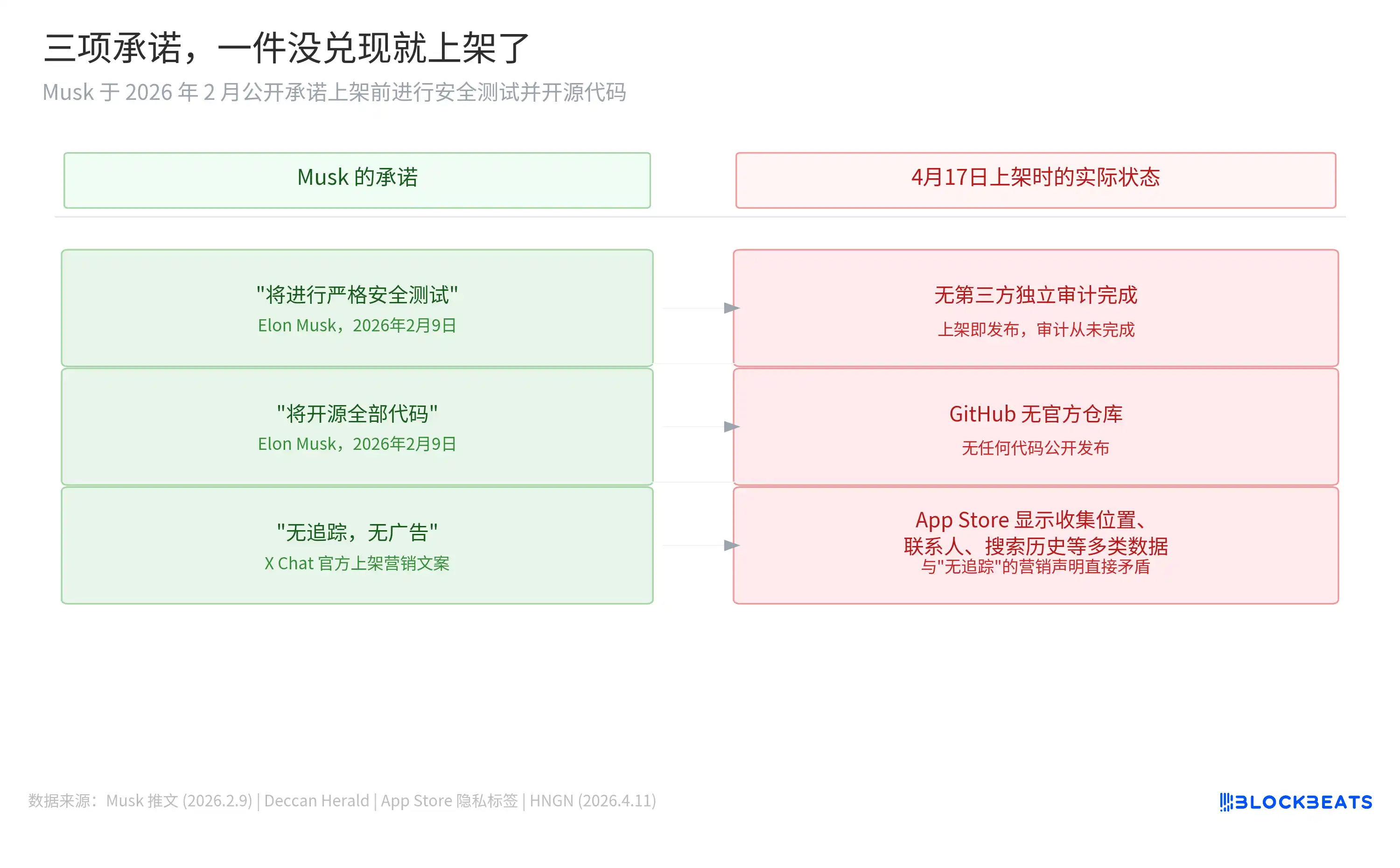
As of its listing on April 17, no independent third-party audit has been completed, there is no official code repository on GitHub, and the App Store privacy label indicates that X Chat collects more than five categories of data, including location, contact information, and search history—directly contradicting its marketing claims of "No Ads, No Trackers."
Question 2: Does Grok know what you’re messaging privately?
Not continuously monitored, but there is a clear entry point.
On each message in X Chat, users can long-press to select "Ask Grok." When this button is tapped, the message is transmitted in plaintext to Grok, at which point it transitions from an encrypted to an unencrypted state.
This design is not a vulnerability—it's a feature. However, X Chat’s privacy policy does not specify whether these plaintext data will be used for Grok’s model training or whether Grok will store this conversation content. By actively clicking “Ask Grok,” the user voluntarily removes the encryption protection from that message.
There is also a structural issue: how quickly this button will shift from being an “optional feature” to a “default habit.” The higher the quality of Grok’s responses, the more frequently users will rely on it, leading to a higher proportion of messages exiting end-to-end encryption. In the long term, the actual encryption strength of X Chat depends not only on the design of the Juicebox protocol but also on how often users click “Ask Grok.”
Question 3: Why is there no Android version?
X Chat is initially available only on iOS; the Android version says "coming soon" with no timeline provided.
Globally, Android holds approximately 73% of the smartphone market, while iOS holds about 27% (IDC/Statista, 2025). Of WhatsApp’s 3.14 billion monthly active users, 73% are on Android (according to Demand Sage). In India, WhatsApp reaches 854 million users, with Android penetration exceeding 95%. In Brazil, it has 148 million users and 81% Android adoption; in Indonesia, it has 112 million users and 87% Android adoption.
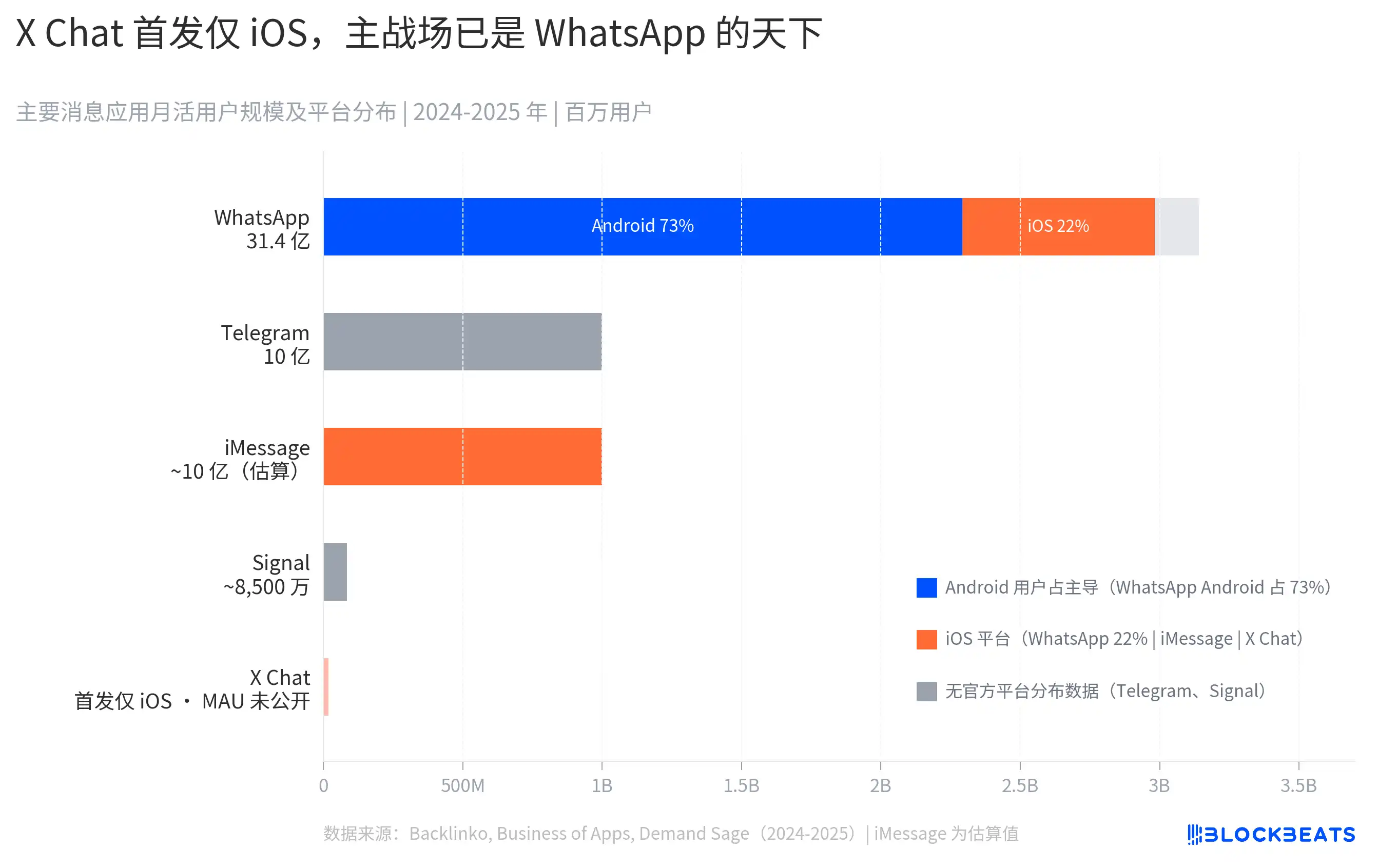
WhatsApp's dominance in the global communications market is built on Android. Signal's monthly active users, at around 85 million, also primarily rely on privacy-conscious users in Android-dominated countries.
X Chat sidestepped this battlefield, and there are two interpretations. First, technical debt: X Chat is built in Rust, and cross-platform support is not easy; prioritizing iOS may reflect engineering timelines. Second, a strategic choice: the U.S. market has an iOS penetration rate of nearly 55%, and X’s core user base is in the U.S.; prioritizing iOS means focusing on its core market rather than directly competing with WhatsApp in Android-dominated emerging markets.
The two interpretations are not mutually exclusive, and the outcome is the same: X Chat, at launch, voluntarily gave up access to 73% of global smartphone users.
Musk's "All-in-One App"
This has been described before: X Chat, X Money, and Grok form a data闭环, parallel to existing infrastructure, with a logic identical to the WeChat ecosystem. This assessment is not new, but with the launch of X Chat, it’s worth revisiting the wiring diagram.
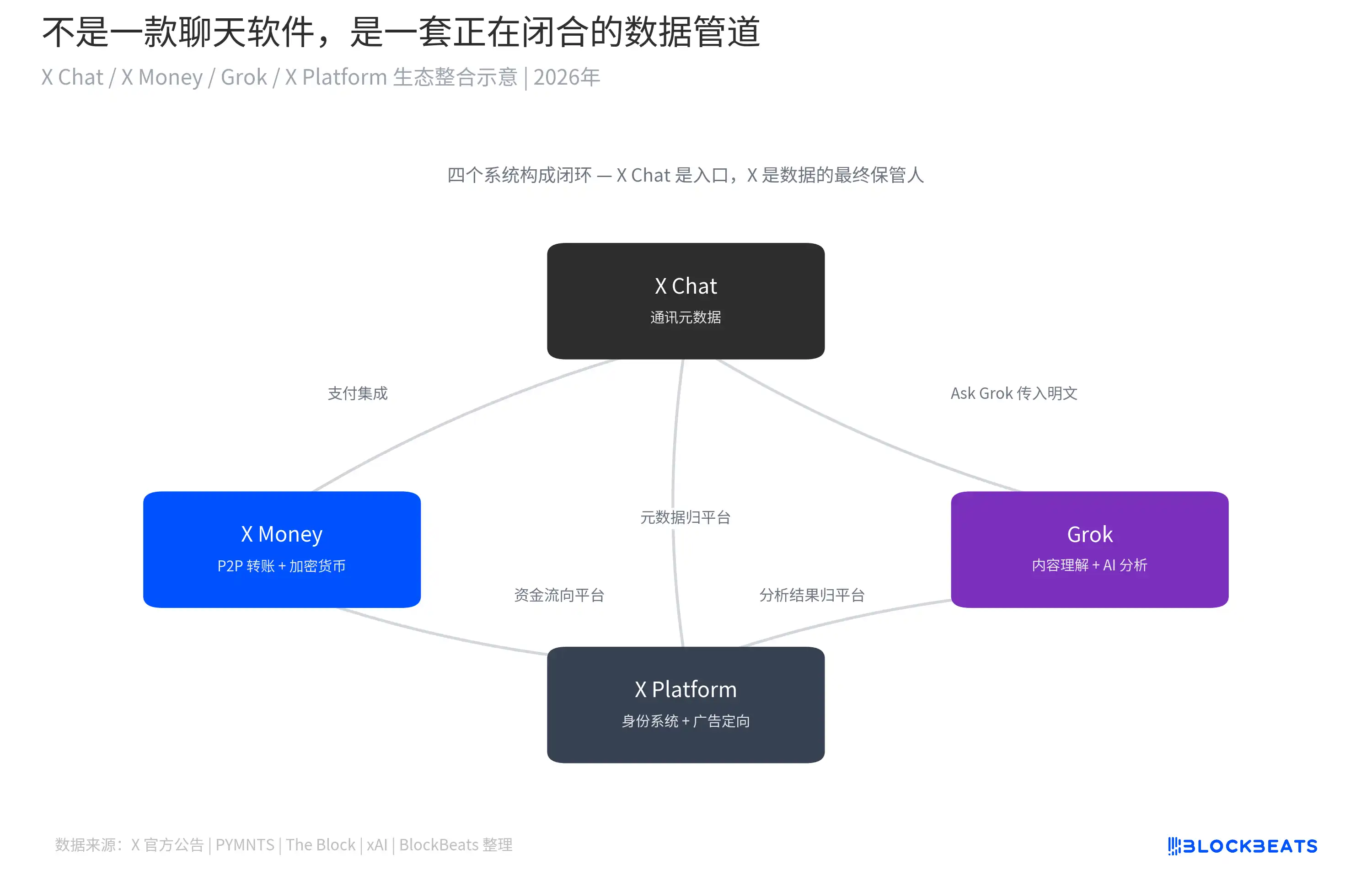
X Chat generates communication metadata, including who is chatting with whom, how long conversations last, and how frequently they occur; this data flows into X’s identity system. A portion of message content enters Grok’s processing pipeline via the Ask Grok feature. Fund transfers are handled by X Money: external beta testing was completed in March, and the service opened to the public in April, enabling fiat peer-to-peer transfers via Visa Direct. Fireblocks executives confirmed that cryptocurrency payments are scheduled to launch by year-end; X Money currently holds money transmitter licenses in over 40 U.S. states.
Each feature of WeChat operates within China's regulatory framework. Musk's system operates within Western regulatory frameworks, but he also heads the Department of Government Efficiency (DOGE). This is not a copy of WeChat; it is the same logic replayed under different political conditions.
The difference is that WeChat has never claimed on its main interface that it is "end-to-end encrypted," while X Chat has. To users, "end-to-end encrypted" means that no one, including the platform itself, can see their messages. X Chat’s architecture does not meet this user expectation, yet it uses the term.
X Chat consolidates three data streams—identifying who this person is, who they’re communicating with, and where their money is coming from and going to—under one company.
That line on the help page has never been just a technical instruction.
Disclaimer: The views expressed in this article are solely those of the author and do not represent the position or opinions of this platform. This article is provided for informational purposes only and does not constitute investment advice of any kind. Any disputes between users and the author are unrelated to this platform. If any articles or images published on this webpage infringe upon your rights, please send an email to support@aicoin.com with relevant proof of rights and identification, and our staff will review your submission.









