Original author: Bocai Bocai (X: @bocaibocai_)
Core Summary
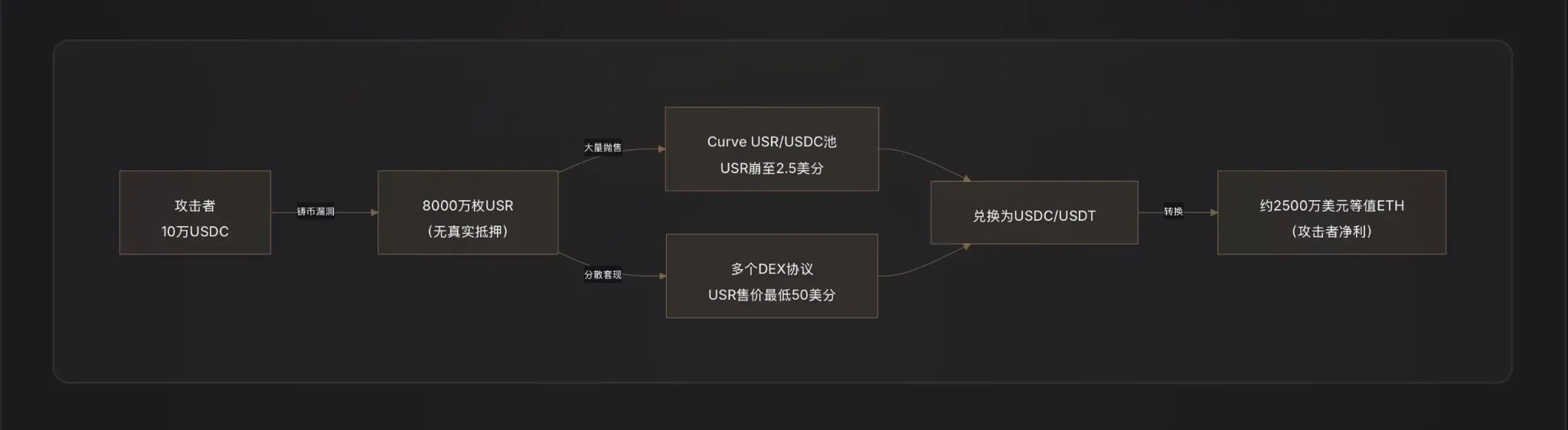
Attack method: The attacker exploited a critical vulnerability in the USR minting function—possibly due to oracle manipulation, leaked off-chain signer keys, or lack of amount validation between mint request and execution—to mint 80 million USR (worth approximately $80 million) using only about $100,000 in USDC, then quickly exchanged them for real assets.
Arbitrage path: The attacker dumped the illegally minted USR in batches into liquidity pools such as Curve Finance, causing the USR price to drop as low as $0.025. Amid the depegging chaos, approximately $25 million was cashed out, after which the arbitrage proceeds were converted into ETH to complete the laundering process.
Loss allocation: According to the design logic of Resolv’s two-layer risk architecture, the collateral shortfall caused by this attack is first absorbed by RLP insurance pool holders (RLP price will decline in line with the protocol’s net asset value), while USR holders are theoretically protected until the protocol suspends redemptions; however, leveraged looping positions on USR on lending protocols such as Morpho have been liquidated due to depegging, resulting in secondary losses.
Associated protocols: The main DeFi protocols affected include Curve Finance (USR/USDC liquidity pool collapsed instantly), Morpho (leveraged positions using USR as collateral were liquidated), and Fluid and Euler (both had USR/RLP circular positions).
Industry alert: This incident reveals a fundamental weakness in delta-neutral stablecoins—the coupling point between minting logic and off-chain signatures/oracles represents the system’s most vulnerable attack surface; any capital efficiency design based on "1:1 minting" must be predicated on extremely rigorous smart contract audits.
I. RESOLV and USR: Understanding this system is essential to understanding this attack
Before discussing the attack, we must first understand how USR works—because the attacker exploited its most sophisticated yet vulnerable design element.
USR's core mechanism: Delta-neutral stablecoin
USR is not a stablecoin backed by bank deposits like USDT, nor is it an over-collateralized stablecoin like DAI. It is a delta-neutral stablecoin—a structure that achieves net risk neutrality by simultaneously holding spot ETH and shorting ETH perpetual futures [Note 1].
The logic is as follows:
When you deposit $1 worth of ETH to mint 1 USR, the Resolv protocol simultaneously opens an equal-sized short position on ETH in the perpetual futures market. If ETH rises, you profit on the spot side but lose on the futures side; if ETH falls, you profit on the futures side but lose on the spot side—the two offset each other, keeping your net asset value approximately equal to $1. This decouples USR from ETH’s price while maintaining its 1:1 USD peg [Note 2].
The advantage of this architecture is extremely high capital efficiency: you only need $1 worth of ETH to mint 1 USR, without requiring over-collateralization. Revenue comes from funding rates on hedged positions (fees paid by longs to shorts) and ETH staking rewards, enabling USR holders to earn approximately 5–6% annualized yield, with the staked version, stUSR, offering an even higher rate [Note 3].

Two-layer architecture: Risk isolation between USR and RLP
Resolv designed a two-tier token structure to address the question of "who bears the protocol's operational risk":
USR layer (high priority): Holders enjoy stable peg protection, and losses are not borne by them;
RLP layer (subordinated layer): RLP holders act as the protocol's "insurance pool," assuming market risk, counterparty risk (such as sustained negative funding rates), and potential contract risk, in exchange for higher returns (20-40% annualized) [Note 4].
The rules are clear: any losses are first absorbed by RLP, then by USR. When the collateralization ratio of USR falls below 110%, RLP redemptions are automatically frozen to prioritize USR holders [Note 5].
This is the key prerequisite for understanding the allocation of losses from this attack.
Attack vector: What exactly went wrong with the minting function?
This is currently the most critical and least understood component. On-chain data has confirmed one thing: the attacker "purchased" $50 million worth of USR using $100,000 in USDC[1]. This 1:500 minting ratio indicates that the contract’s mint amount validation has completely failed.
The crypto fund D2 Finance proposed three possible attack path hypotheses [Note 9]:
Hypothesis A: Oracle Manipulation. The minting price of USR depends on a price oracle. If an attacker can temporarily depress the oracle’s price quote within a single transaction (e.g., by using a flash loan to dump the asset), causing the contract to believe the user’s deposited assets are worth more than they actually are, they could mint excess USR [Note 6].
Hypothesis B: Off-Chain Signer Compromise. The Resolv minting process includes an off-chain signature verification step—users’ minting requests must be signed by the protocol’s backend service to be executed. If this signing key is compromised, an attacker can forge legitimate minting instructions for any amount, bypassing all on-chain restrictions [2].
Hypothesis C: Missing validation between request and execution (Validation Gap). The minting process consists of two steps: "initiating a request" and "executing the mint." If the contract does not strictly verify that the final executed amount matches the requested amount during execution, an attacker could alter the parameters after initiating the request but before execution, enabling excessive minting.
As of the time this report was written, Resolv's official team has not yet released a complete root cause analysis (RCA), so the prioritization of the three hypotheses above cannot be definitively confirmed.
Based on the attack’s impact, Hypothesis B (signer key compromise) or Hypothesis C (missing validation logic) is more likely—oracle manipulation typically requires substantial funds and is unlikely to produce such extreme price deviations; meanwhile, the attacker invested very limited capital when minting 80 million USR, which better aligns with the characteristics of "bypassing contract validation."
How attackers cash out: A textbook DeFi exit scam
After acquiring 80 million USR, the attacker faced the challenge of converting the falsely minted stablecoin into real value.
D2 Finance calls this a "textbook DeFi hacker cash-out path": the attacker batch-sent USR to multiple liquidity protocols, prioritizing large-scale sales in Curve Finance’s USR/USDC pool (USR’s largest liquidity pool, with daily trading volume of $3.6 million) [Note 10].
Because Curve's liquidity was limited, the sudden influx of 80 million USR completely drained the pool—USR's price dropped from $1 to 2.5 cents within 17 minutes. The attacker did not intend to sell all USR at $1, but instead gradually exchanged them for USDC/USDT in the range of $0.25 to $0.50, ultimately converting the arbitrage proceeds into ETH to complete the washout.
PeckShield estimates the final cash-out amount to be approximately $25 million [Note 11]—considering the slippage losses caused by a large volume of USR being sold at extremely low price levels, this figure implies that the attackers’ actual withdrawal rate was around 30% ($25M/$80M). The remaining 70% of the "value" vanished due to massive slippage from depleted liquidity.
Three: After the Anchor, What Happened to USR, RLP, and the Collateral System
The collateralization ratio of USR collapsed instantly.
Under normal conditions, USR is backed 1:1 by ETH+ hedging positions. However, after 80 million uncollateralized USR were minted into the system, the actual assets backing the entire USR supply are far insufficient for 1:1 redemption—collateralization ratios have dropped significantly below 100%.
This directly triggered the RLP layer's protection mechanism—the protocol theoretically freezes RLP redemptions to prioritize protecting USR holders. However, at the same time, since USR itself has become de-pegged (trading at approximately $0.87 on secondary markets), USR holders also face losses from selling at market price.
Cascading liquidation of lending protocols
One of the most underestimated collateral damages from this incident.
Resolv's growth largely relies on a strategy: users deposit USR as collateral into lending protocols such as Morpho, Fluid, and Euler, borrow USDC, then use the borrowed USDC to purchase more USR, repeating this cycle to create a leveraged looping position—some users achieve leverage ratios as high as 10x [3].
When the price of USR plummeted from $1 to $0.87 and lower, the collateral value of these leveraged positions instantly evaporated by over 13%. Since lending protocols automatically trigger liquidations when the collateral ratio falls below the liquidation threshold, large amounts of USR were liquidated by bots, flooding the secondary market with more USR and further driving down the price—creating a classic death spiral pressure [Note 7].
On Morpho, there is a dedicated "MEV Capital Resolv USR Vault," which had already accumulated a substantial TVL prior to the attack, making these positions the primary bearers of collateral damage [4].
Sharp decline in protocol TVL
Prior to the attack, Resolv's TVL had grown to hundreds of millions of dollars (peaking at over $650 million, primarily driven by leveraged positions on Morpho and Euler). After the protocol was paused, users were unable to redeem USR, and the TVL calculation became chaotic due to USR's price depegging [5].
Four: Who bears the loss? Analysis of each party's risk exposure
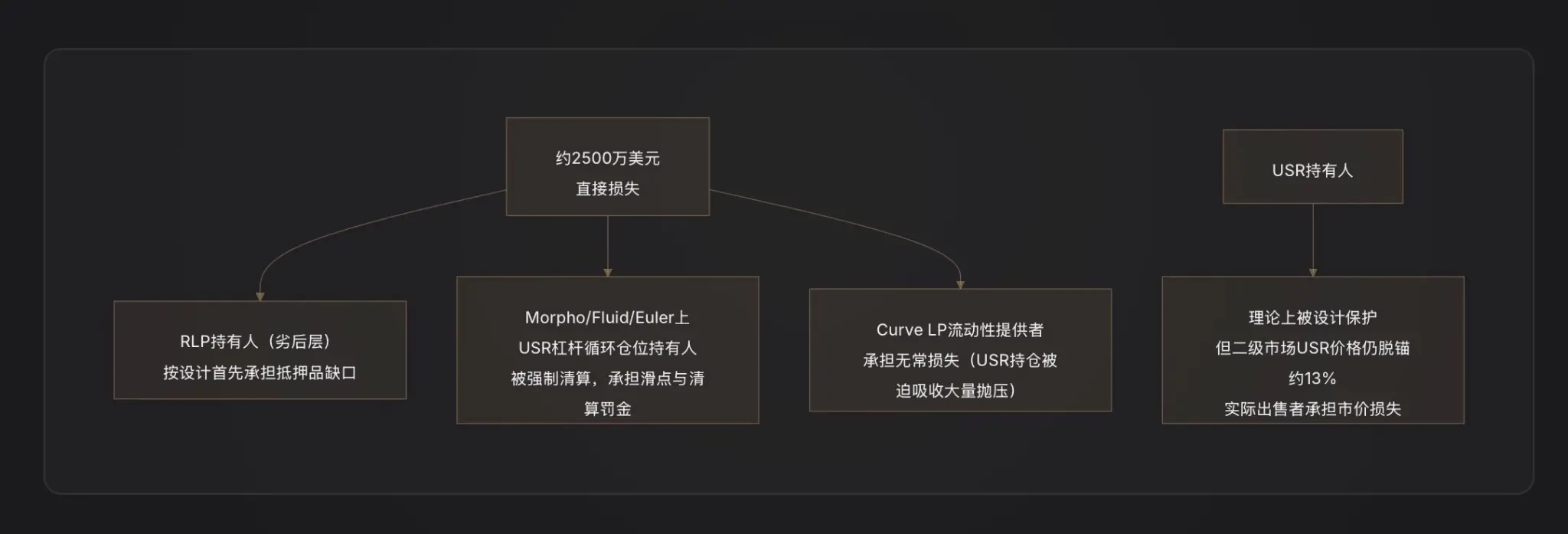
RLP holders are designed as the first loss layer. The collateral gap caused by the attack (80 million uncollateralized USR minted) will directly manifest as a decline in RLP net value—RLP price represents equity in the protocol’s overcollateralized portion, and when the protocol incurs uncovered debt, RLP depreciates first [6].
USR leveraged position holders have suffered the greatest actual losses. They not only face liquidation (which typically incurs a 5-10% penalty), but also sold their positions below the peg price during the USR depegging period, resulting in unavoidable compounded losses.
Curve LP providers bear impermanent loss—when attackers sell large amounts of USR, the LP pool passively absorbs a large volume of USR (selling USDC and holding more low-priced USR), resulting in arbitrage-related losses [Note 8].
Regular USR holders: By design, if the protocol triggers its pause mechanism normally, USR holders can redeem their tokens at a 1:1 rate against the remaining underlying collateral. However, the issue is that after the attack, the protocol suspended all functions, closing the redemption window—actual sellers could only transact at the market price of $0.87, incurring a 13% depeg loss.
Five: Emergency Response: RESOLV Team's Response Measures
The Resolv team's immediate response was to suspend all protocol functions, including minting, redeeming, and transferring, to cut off the attacker's further avenues of operation [1].
As of the time this report was written, Resolv has publicly acknowledged the attack, but the full post-mortem report and official compensation plan have not yet been released. This aligns with the typical response timeline for DeFi security incidents—teams generally require 48 to 72 hours to complete on-chain forensic analysis and vulnerability confirmation before disclosing detailed remediation plans.
Notably, Resolv previously partnered with Immunefi to establish a bug bounty program and deployed Hypernative’s proactive security monitoring system [7]. The latter was theoretically capable of detecting early warning signals of anomalous minting events—raising the question: Did the alert system trigger in time, or did the speed of the attack exceed the window for human intervention?
Given the extreme speed at which USR crashed to 2.5 cents within 17 minutes, the attack was executed with high efficiency, leaving an extremely limited reaction window.
Six: Warning on Similar Protocols: Systemic Risks of Delta-Neutral Stablecoins
This Resolv incident is not isolated; it is a representative failure in the DeFi "synthetic dollar" sector.
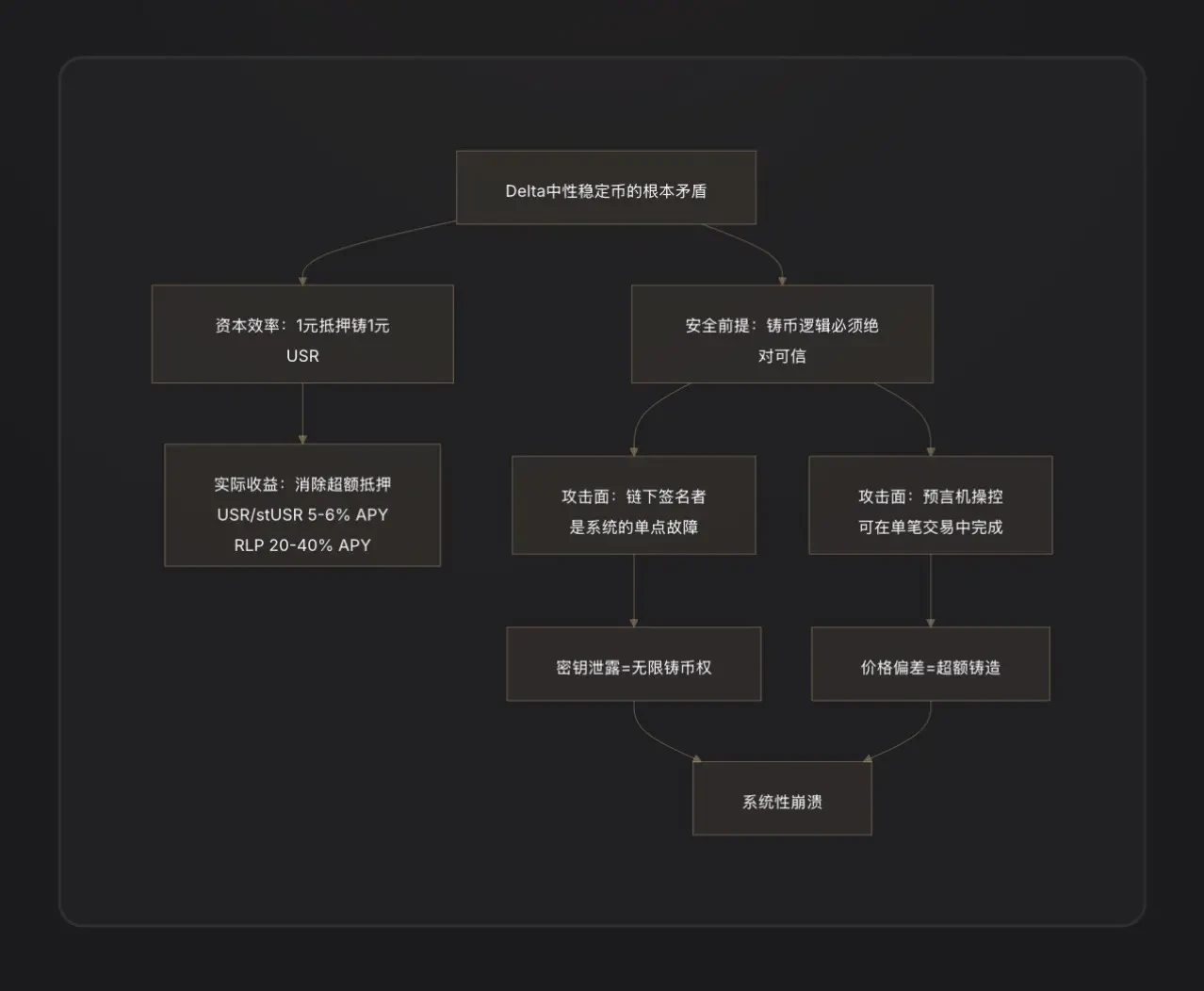
Key Lesson One: Off-chain signers are a centralized risk. Delta-neutral stablecoins often introduce off-chain backend services to validate orders for efficient minting. This "off-chain component" is essentially a centralized point of power—if its private key is compromised, attackers gain the protocol’s minting authority. This introduces Web2 security vulnerabilities into Web3[8].
Key Lesson Two: "1:1 capital efficiency" is a double-edged sword. The design philosophy of over-collateralized systems (like MakerDAO) is that even if there are minor contract vulnerabilities, the excess collateral buffer can absorb some losses. Delta-neutral systems eliminate this buffer entirely—any failure in the minting logic directly creates a proportional system shortfall, with no redundancy.
Key Lesson Three: Audits fail to keep pace with rapid TVL growth. Resolv’s TVL surged from under $50 million to over $650 million in just three months, primarily driven by leveraged arbitrage strategies on Morpho. The rapid expansion in system complexity and integration points placed immense pressure on audits. Similar lessons have been repeated throughout DeFi history: Euler Finance (March 2023, $197 million loss) and Inverse Finance (April 2022, $15.6 million loss) were both tragedies of designs that appeared sound but contained subtle flaws in minting or lending logic [9].
Seven: Key Conclusions
This attack reveals not just a contract vulnerability, but a deeper structural contradiction within the delta-neutral stablecoin sector.
The story begins with the ambitious design of USR: achieving 1:1 capital efficiency without relying on fiat reserves or over-collateralization, solely through hedging derivatives. This design worked perfectly during the upward phase—users minted one USR with one dollar’s worth of ETH, and the protocol rewarded them with funding rates, rapidly attracting hundreds of millions in TVL.
But "1:1 capital efficiency" also means the system has no collateral buffer whatsoever. If there is a flaw in the minting logic—whether due to leaked off-chain signatory keys or missing validation between request and execution—an attacker can generate any amount of stablecoin at nearly zero cost. Unlike over-collateralized systems, there is no safety cushion; the attack penetrates the system directly.
The creation of 80 million USR took just $100,000, 17 minutes, and a price low of 2.5 cents. The attacker withdrew $25 million in real value, leaving the protocol with a black hole awaiting repair—and a bill paid in real costs by RLP holders, leveraged position users, and Curve LPs.
The ripple effects from peripheral protocols like Curve, Morpho, Fluid, and Euler illustrate another side of DeFi’s “hypercomposability”: while integrations between protocols amplify returns during normal times, they also magnify risks during crises. Ultimately, the lesson here is clear: in DeFi, every efficiency window you open is also an attack surface you expose. The presence of off-chain signers makes protocols more flexible but introduces an additional centralized point of failure.
Notes
[Note 1] Delta Neutral: A financial derivatives term. Delta measures an asset's sensitivity to price changes in the underlying asset. "Delta = 0" means the position does not profit or lose from movements in the underlying asset's price—indicating full hedging. For Resolv, holding $1 worth of ETH (Delta = +1) while shorting an equal amount of ETH futures (Delta = -1) results in a net Delta of 0, hence termed "Delta Neutral."
[Note 2] Perpetual Futures: A type of futures contract with no expiration date, and the dominant derivative instrument in the cryptocurrency market. Holding a short perpetual futures position means profiting when the ETH price falls and losing when it rises, thereby hedging against price risk of spot ETH.
[Note 3] Funding Rate: A mechanism to balance the perpetual futures market. When long positions exceed short positions, longs pay funding fees to shorts periodically, and vice versa. As a short position holder, Resolv typically receives consistent funding fees in a bull-biased crypto market, which is its core source of income.
[Note 4] Junior Tranche: In a financial tranching structure, junior tranche investors are the first to absorb losses (acting as the "first loss bear"), but they also receive a higher risk premium as compensation during profit distributions. RLP corresponds to the junior tranche of the Resolv protocol, while USR corresponds to the senior tranche.
[Note 5] 110% collateralization trigger line: The total value of collateral backing USR is 1.1 times the total circulating supply of USR. When this line is breached, RLP redemptions are paused to ensure remaining assets are prioritized for USR holders' redemptions.
[Note 6] Flash Loan: A collateral-free borrowing tool unique to DeFi, requiring both borrowing and repayment to occur within the same transaction (same block). Attackers can use this to temporarily acquire large sums of funds to manipulate prices, as long as the loan is repaid before the transaction ends, with nearly zero capital cost.
[Note 7] Death Spiral: A self-reinforcing collapse during deleveraging: falling asset prices → triggering liquidations → more assets sold → prices fall further → triggering more liquidations, in a vicious cycle.
[Note 8] Impermanent Loss: A unique risk faced by liquidity providers (LPs) on automated market makers (AMMs). When the price ratio of the two assets in the pool deviates from their initial state, the value of the LP’s portfolio falls below the value of simply holding the two assets outright; this difference is known as impermanent loss.
[Note 9] D2 Finance / CoinTelegraph analysis, quoting D2 Finance: "Either the oracle was gamed, the off-chain signer was compromised, or the amount validation between request and completion is simply missing." Same source.
[Note 10] CoinTelegraph reported that USR had a 24-hour trading volume of $3.6 million in the Curve USR/USDC pool, with the price dropping to 2.5 cents at 2:38 UTC.
[Note 11] PeckShield estimated data, cited from CoinTelegraph, same source: "PeckShield estimated that the attacker was able to extract around $25 million from the attack amid USR's depeg."










