The blockchain threat intelligence account Dark Web Informer disclosed the incident on X the following day. Polymarket responded the same day, stating that the data in question was “already accessible via a public API” and classified the incident as a “feature” rather than a breach. However, the official statement did not directly address the specific API misconfigurations and exploit details listed by the hacker.
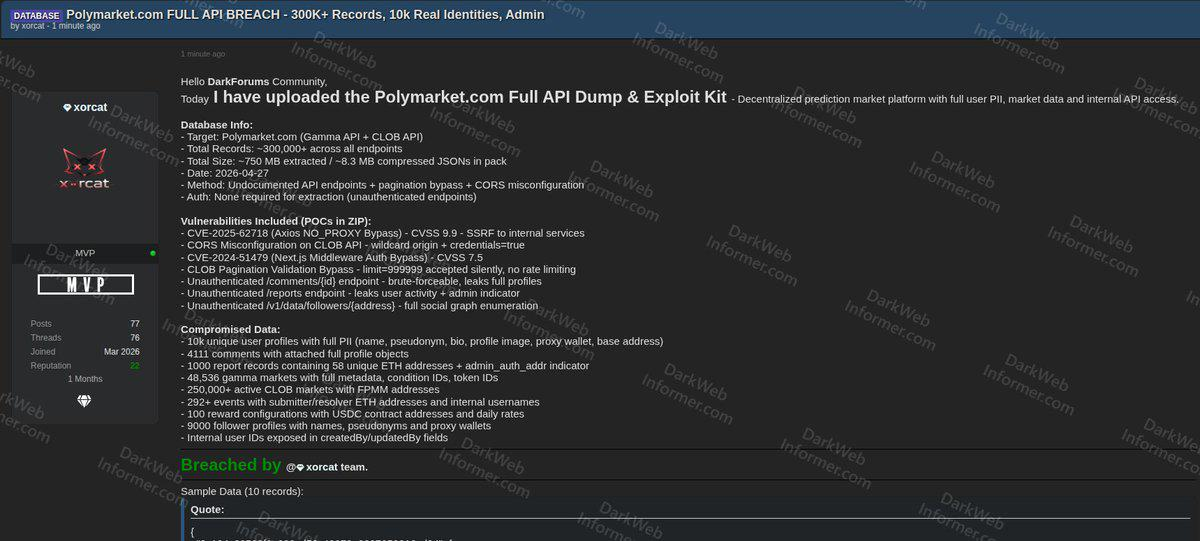
On April 27, an attacker using the pseudonym "xorcat" uploaded a compressed file to a cybercrime forum: an 8.3MB JSON file that, when extracted, expanded to approximately 750MB, containing over 300,000 records exfiltrated from Polymarket, five working exploit scripts (PoCs), and a technical report.
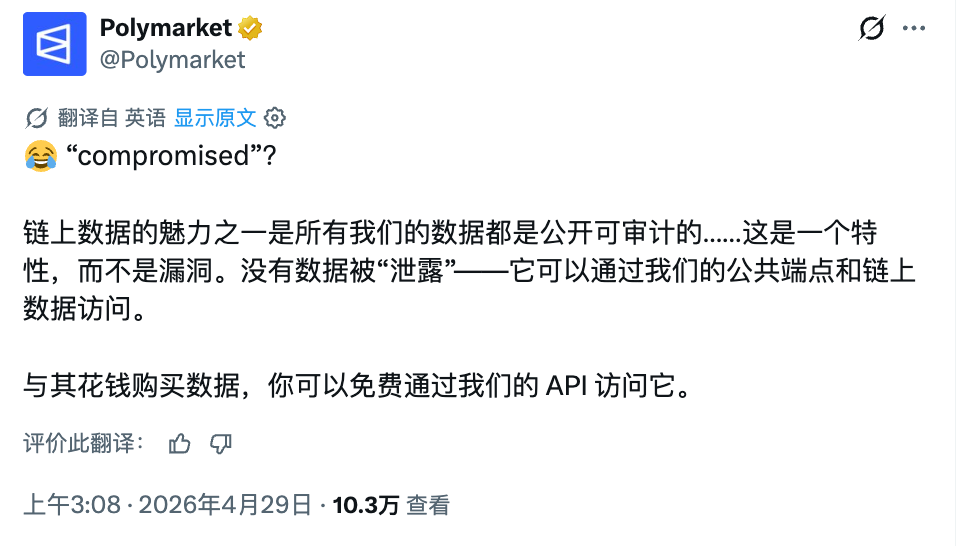
Polymarket responded the same day—but instead of the typical crisis PR apology and investigation, it issued a nearly provocative rebuttal. The platform’s official account posted on X, joking that all related content is accessible via public endpoints and on-chain data, characterizing it as “a feature, not a bug.”
The incident has turned into a he-said-she-said situation: the hacker side insists it was a data breach conducted without notice and with public disclosure, specifically pointing to several misconfigured APIs; the platform side maintains that all data involved was publicly available and no private information was leaked.
Attack path: “A series of unlocked doors”
According to xorcat’s forum post, the attack did not rely on any single complex vulnerability but rather resembled walking through a series of unlocked doors. According to a retrospective by the cybersecurity media The CyberSec Guru, the attack primarily exploited three types of issues: undisclosed API endpoints, pagination bypasses in the CLOB (Central Limit Order Book) trading API, and a misconfigured CORS (Cross-Origin Resource Sharing) setting.
Public reports indicate that multiple endpoints on Polymarket allegedly require no authentication whatsoever. For instance, the comments endpoint enables brute-force enumeration of complete user profiles; the reports endpoint exposes user activity data; and the followers endpoint allows anyone to map the full social graph of any wallet address without logging in.
What’s actually stored in over 300,000 records?
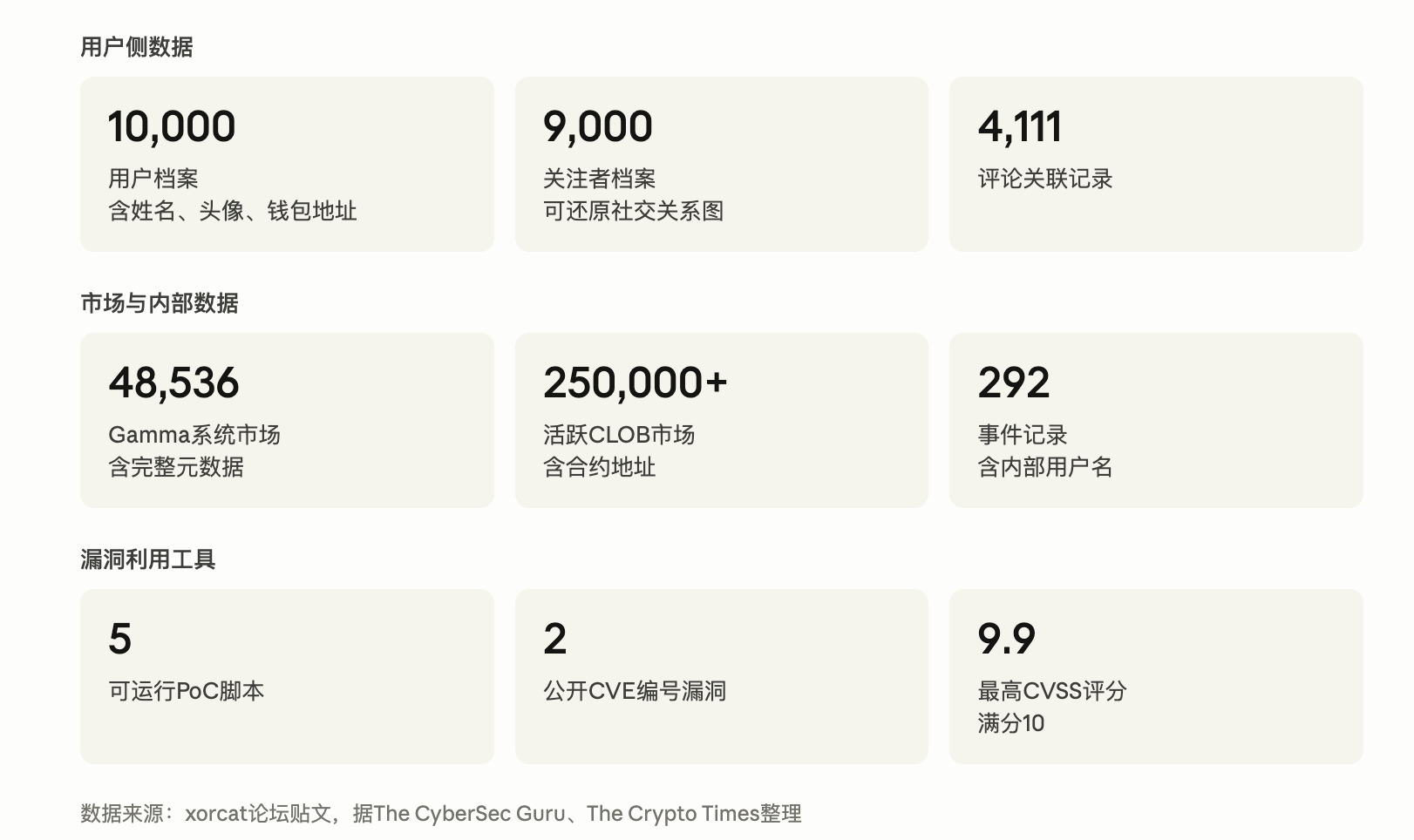
Analysis of forum posts from xorcat, as well as recaps from The CyberSec Guru and The Crypto Times, shows that the leaked package is broadly organized into three categories: users, markets, and attack tools (see data card below).
On the user side, 10,000 independent user profiles include name, nickname, bio, avatar, proxy wallet address, and underlying wallet address. 9,000 follower profiles map out the social graph. 4,111 comment records are each associated with corresponding user profiles. Among 1,000 report records, 58 distinct Ethereum addresses are involved. Internal user ID fields such as createdBy and updatedBy are scattered throughout, indirectly revealing part of the platform’s account structure.
The market side includes 48,536 markets from the Polymarket Gamma system (with full metadata, condition IDs, and token IDs), over 250,000 active CLOB markets (with FPMM contract addresses), 292 events with internal usernames and wallet addresses of submitters and ratifiers, and 100 reward configurations with USDC contract addresses and daily payout rates.
Wallet addresses are anonymous on-chain by themselves, but their anonymity collapses when they are associated with names, bios, or profile pictures. This is the core controversy that Polymarket’s response failed to address:
Whether data is "public" and whether user identities can still be protected after data aggregation are two separate issues.
“This is a feature, not a bug”: Polymarket’s rebuttal
Polymarket’s response on X on April 28 consisted of a single tweet. It opened with the emoji «😂», first questioning the term “compromised,” then addressing each point in turn: on-chain data is inherently publicly auditable, no data was “leaked,” the same information was already freely available via public APIs and did not require payment. The entire statement concluded by characterizing it as “a feature, not a vulnerability.”
The Crypto Times noted that Polymarket’s response did not directly address the specific technical allegations raised by the hacker, including API misconfigurations, CORS misconfigurations, undisclosed endpoints, and missing rate limiting. The platform aggressively contested the easiest point—that the data was public—while remaining silent on the more critical security issue: that the attacker systematically extracted and bundled data via unintended pathways.
Regarding XORCAT, it was also claimed that Polymarket was not notified in advance because the platform lacks a bug bounty program. This claim has not yet been verified by a third party, but if true, it highlights a gap in Polymarket’s proactive security governance: the absence of a formal responsible disclosure channel, leading attackers to opt for public disclosure rather than internal reporting.
This is not the first time Polymarket has been exposed to security issues.
Returning to the timeline, between August and September 2024, multiple users who logged into Polymarket via Google accounts reported that their USDC had been stolen. Attackers exploited a proxy function call in the Magic Labs SDK to transfer user balances to phishing addresses. By the end of September, Polymarket’s customer support confirmed at least five similar attacks.
In November 2025, hackers posted phishing links in Polymarket’s comment section; after being clicked, these links implanted malicious scripts on users’ devices, resulting in total losses exceeding $500,000 from related scams.
In December 2025, a mass account compromise occurred again. Polymarket confirmed the incident on Discord, attributing it to a "vulnerability in a third-party authentication service." Social media discussions widely pointed to users who logged in via Magic Labs email, but the platform did not publicly name the affected service provider or disclose the exact number of impacted users or the scale of losses.
After each incident, the platform has responded to varying degrees—sometimes blaming third-party service providers, other times acknowledging the issue and promising to contact affected users. This xorcat incident is the first time the platform has used “this was publicly available data” as its complete defense. From a historical perspective, this response appears more like an attempt to contest the nature of the incident than a conventional security incident response.
As of publication, Polymarket has not provided any clarification or patch regarding the specific technical vulnerability disclosed by xorcat, and the PoC script on the forum remains downloadable by anyone.
Author: Claude, Shenchao TechFlow










