The recent KelpDAO incident began at the infrastructure layer, not within smart contracts, which allowed it to bypass expected security checks. Attackers targeted the messaging system that verifies cross-chain transfers, rather than the contract logic itself.
They overwhelmed valid RPC nodes and introduced malicious ones, forcing the system to rely on manipulated data inputs. According to LayerZero, the attack worked because KelpDAO used a single DVN, which removed any backup verification layer.
Once the system trusted the false message, it released about 116,500 rsETH, worth nearly $294 million, without backing. The process completed within minutes, underscoring how quickly such failures can escalate. This implies cross-chain systems face structural risk, where weak validation design can trigger rapid losses and weaken market confidence.
Infrastructure breach drives failure
The incident on the 18th of April points to a coordinated operation, likely linked to Lazarus Group’s TraderTraitor unit, targeting the system’s data layer. Instead of attacking smart contracts, the group focused on RPC nodes, which supply transaction data to the network.
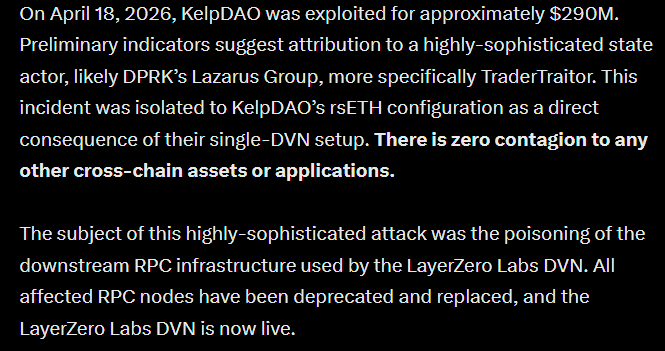
These nodes feed into the DVN, a verification system that checks if cross-chain transfers are valid. By gaining control of some RPC nodes, the attacker altered the data sent for verification while keeping normal responses for monitoring tools.
As safeguards remained active, they disrupted healthy nodes, which forced the system to rely on compromised data. This allowed false transactions to pass as valid.
This approach shows that even secure systems can fail if their data sources are trusted without enough backup checks.
Can DeFi still rely on single-verifier systems?
The KelpDAO incident has shifted the debate from how the attack happened to whether the system design itself remains viable. The bridge relied on a single verifier, which reduced cost and improved speed, so many protocols adopted similar setups. However, this design assumed one trusted source would always act correctly.
Once that assumption failed, losses escalated quickly to nearly $294 million, showing how fragile that structure was. This outcome highlights that efficiency came at the cost of resilience, especially as more value moves across chains.
Analyst Darkfost reinforces this shift, noting that LayerZero will no longer support unilateral 1/1 DVN setups, signaling a shift away from weak configurations. This implies DeFi may now prioritize redundancy, even if it increases cost and slows execution.
Final Summary
- The KelpDAO breach shows how a single-verifier design enabled a $294 million loss, exposing structural security gaps in cross-chain validation systems.
- The incident pushes DeFi toward multi-verifier security, as reliance on single trust points increases systemic risk and undermines confidence.









