
Foreword
In the blockchain world, every on-chain operation relies on gas fees to function. They serve as the "fuel" that powers the network, yet they have also become a target for malicious actors. From unauthorized infinite approvals leading to assets being quietly drained, to gas fee hijacking causing users to pay far more than expected, these traps are growing increasingly stealthy.
Unlike traditional phishing attacks, these attacks often disguise themselves as legitimate actions such as “authorization,” “minting NFTs,” or “participating in DeFi mining,” exploiting users’ unfamiliarity with contract mechanisms to silently consume or steal assets. To help you recognize these risks, the Zero Time Tech security team, drawing on industry security practices and building on their series of blockchain security educational content, focuses on gas fees and transaction security to break down common traps, equip you with practical prevention techniques, and outline emergency response steps in case of asset loss.
Prat 01-Common Gas Fees and Transaction Security Pitfalls
Gas fees serve as the “pass” for on-chain transactions, and the security of related operations is directly tied to the safety of users’ assets. Malicious actors exploit users’ lack of understanding of gas fee mechanisms and contract approvals to create various hidden traps, often disguised as normal on-chain interactions to avoid detection. Common traps fall into the following three categories:
1. Unlimited authorization
An infinite approval is when a user grants a smart contract unlimited permission to spend a specific token from their wallet during interaction. This is one of the most common and dangerous traps leading to asset loss.
◆ How it works: When you click the “Approve” button in a DApp, if you don’t carefully check the approval amount, you may inadvertently sign an “unlimited approval” agreement. This means the contract can theoretically transfer all tokens of that type from your wallet at any time, without requiring further confirmation from you.
◆ Typical scenario: When minting niche NFTs, participating in un-audited DeFi liquidity mining, or trading on obscure DEXs, malicious contracts automatically check “unlimited approval,” tricking users into quickly confirming, then silently draining assets from their wallets without their knowledge.

2. Gas fee hijacking
Gas fee hijacking refers to attackers forcing users to pay significantly higher-than-normal gas fees by using malicious contracts or tampering with transaction data, or even directly stealing the gas fees paid by users — essentially exploiting manipulation of gas-related parameters for illegal gain.
◆ Operating Logic:
Frontend manipulation: An attacker-controlled DApp frontend automatically sets the gas price or gas limit to extremely high levels when the user initiates a transaction, far exceeding fees during normal network congestion.
Contract malicious gas consumption: Malicious contracts contain "infinite loop" code that, when executed, continuously consumes Gas until the user's set Gas limit is exhausted, resulting in transaction failure, but the Gas fees have already been deducted by the blockchain node.
◆ Typical scenario: A user participates in a popular NFT whitelist mint via a non-official link; after clicking confirmation, their wallet instantly deducts dozens of times the normal amount of ETH as gas fees, but the NFT never arrives.
3. Fake Authorization / Fake Transactions
Attackers trick users into signing malicious data by forging authorization requests or transaction pop-ups, directly stealing assets or taking control of wallets, often combined with gas fee traps.
◆ Operating Logic:
Phishing link诱导: Users click on "official links" in phishing emails, Discord direct messages, or social media ads, leading them to counterfeit websites that closely resemble legitimate DApps.
Malicious request forgery: A fake “authorization” popup from a spoofed website, seemingly displaying “authorize token for trading,” but the actual transaction data has been altered to instruct the transfer of the user’s assets directly to the attacker’s wallet.
◆ Typical scenario: The user receives a private message stating, "Your wallet has security risks and requires urgent authorization verification," clicks the link, completes authorization, pays a high gas fee, and instantly loses all major tokens in their wallet.

Part 02-Wallet Security Settings and Preventive Measures
To address the above gas fees and transaction security traps, the key lies in “prevention beforehand.” Users don’t need to master complex blockchain technology—just focus on three core areas: authorization management, gas fee settings, and transaction verification. By developing good operational habits, risks can be effectively avoided. Here are three practical steps:
1. Strictly control authorization limits and adhere to the principle of least privilege
Authorization actions are the primary entry point for asset loss. Controlling authorization limits cuts off risk at its source—the core principle is “do not authorize excess balances, and revoke immediately when not in use.”
◆ Reject infinite approval: When approving any DApp, always decline the default option and choose “custom amount,” authorizing only the minimum token quantity required for the current operation (e.g., authorize only 0.01 ETH to mint an NFT, or authorize only the exact amount needed for the transaction).
◆ Grant permissions on demand and revoke immediately after use: For temporary DApp interactions, revoke authorization immediately after the operation is complete; for long-term, compliant DApps, regularly review authorization limits to avoid asset risks due to contract vulnerabilities.
2. Fine-tune Gas fee settings to prevent malicious hijacking
Setting gas fee parameters is crucial to preventing gas fee hijacking; take active control of gas fee settings to avoid manipulation by malicious frontends or contracts, reducing unnecessary cost losses.
◆ Enable Advanced Gas Control: Turn on the "Advanced Gas Management" feature in major wallets such as MetaMask and TokenPocket, and manually set the Gas price and Gas limit cap to prevent malicious frontends from altering parameters.
◆ Refer to on-chain data: Before initiating a transaction, check the current network average Gas price using blockchain explorers such as Etherscan or Arbiscan, and reject transaction requests with Gas prices significantly above market levels.
◆ Avoid high-congestion periods: During times such as popular project mints or major policy announcements, network gas fees surge. Pause non-urgent operations during these periods, or use Layer 2 networks to reduce costs and risks.
3. Strengthen trading security and avoid common pitfalls
In addition to authorization and gas fee settings, verifying the details of each transaction and ensuring the security of interaction scenarios are crucial steps in avoiding traps—always carefully check details and refuse anything suspicious.
◆ Verify core transaction details: When confirming via wallet popup, you must check three items — whether the contract address matches the official one, whether the transaction amount is correct, and whether the Gas fee parameters are reasonable. All three are mandatory.
◆ Verify DApp authenticity: Obtain DApp links only through the official website or verified blue-check social media accounts, cross-check the website’s SSL certificate and contract address, and avoid clicking on suspicious links.
◆ Isolate risky assets: Use a dual-wallet strategy—keep only a small amount of assets in the hot wallet for daily transactions, and store large holdings in hardware or cold wallets to completely isolate on-chain interaction risks.

Part 03-Handling and Tool Recommendations After Asset Loss
Even with proper precautions, negligence can still lead to malicious attacks. In such cases, swift and accurate response can minimize losses to the greatest extent. The ZeroTime Security Team, drawing on real-world experience, has compiled “Emergency Response Steps” and “Essential Security Tools” to help users take control during a crisis.
1. Three-step emergency response (Golden 10 minutes)
Authorization actions are the primary entry point for asset loss. Controlling authorization limits cuts off risk at its source—the core principle is “do not authorize excess balances, and revoke immediately when not in use.”
◆ Immediately freeze your wallet and revoke approvals: After detecting unusual asset transfers or high gas fees being deducted, immediately freeze operations using the wallet’s “Pause Transactions” feature; then open your approval management tool to batch-revoke approvals for all suspicious contracts, cutting off the attacker’s access to your assets.
◆ Secure and report evidence to the platform: Take screenshots to preserve key evidence such as the transaction hash (TxID), malicious contract address, authorization records, and DApp access links; submit the transaction hash to a block explorer and flag the transaction as “suspicious attack”; also report to the wallet provider and DApp platform to request assistance in blocking the activity.
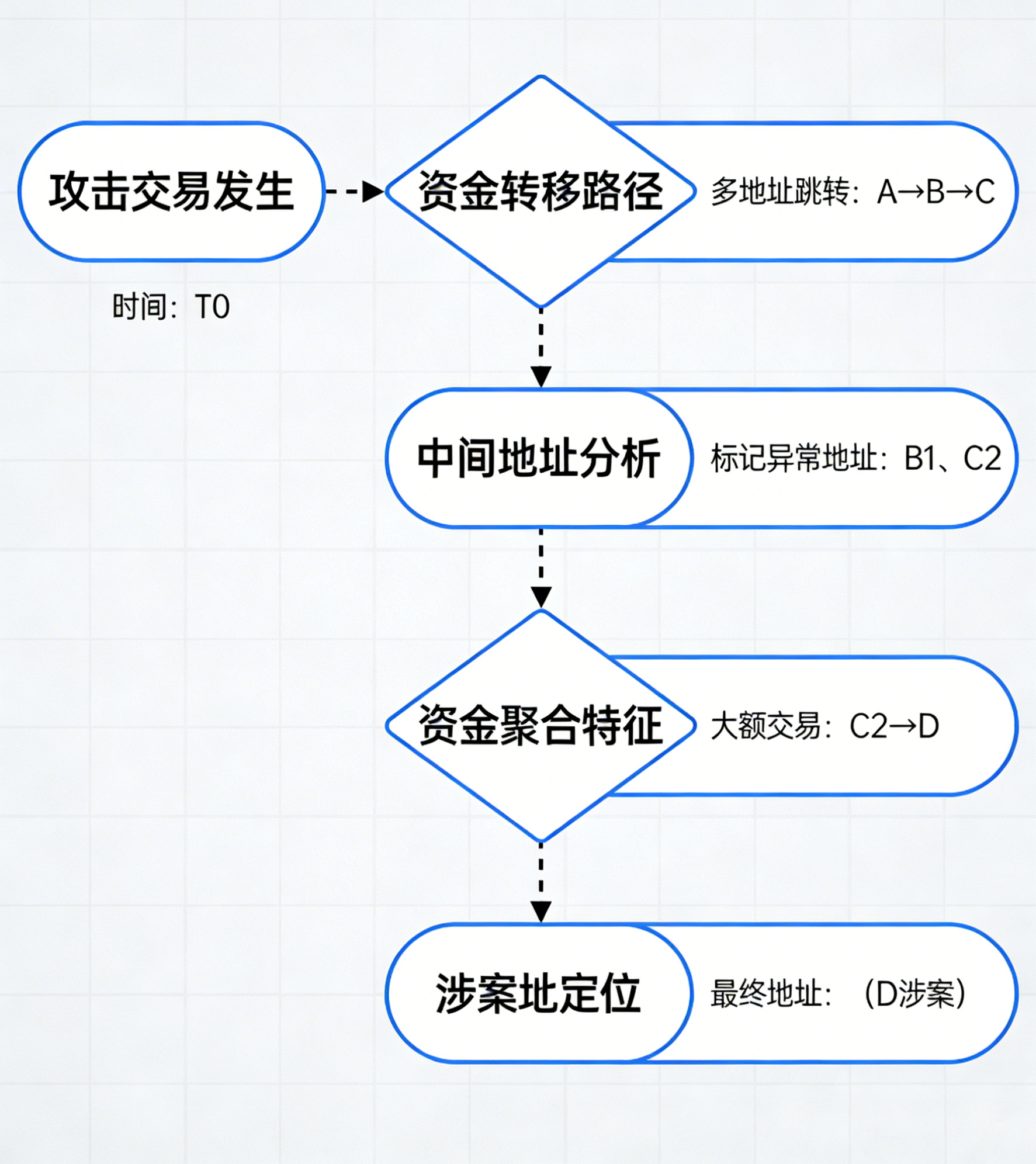
◆ Seek assistance from professional security agencies: If significant asset loss is involved, immediately contact a professional blockchain security firm (such as ZeroTime Technology) and provide a complete chain of evidence. The security team can use on-chain tracing technology to track the attacker’s fund movements, assist in coordinating with law enforcement, and attempt to freeze assets associated with the involved addresses.
2. Recommended Essential Blockchain Security Tools
To help users maintain daily security and quickly respond to risks, we’ve selected 4 essential tools covering core scenarios such as authorization management, transaction verification, and risk alerts—all industry-recognized security tools:

3. Common Disposal Misconceptions (Avoidance Guide)
To help users maintain daily security and quickly respond to risks, we’ve selected 4 essential tools covering core scenarios such as authorization management, transaction verification, and risk alerts—all industry-recognized security tools:
◆ Myth #1: Paying a “unfreezing fee” to recover assets—scammers demand tokens under the pretense of helping to freeze涉案 addresses; this is a second-layer scam. Do not be deceived.
◆ Misconception 2: Just delete the wallet—Deleting the wallet does not revoke contract approvals; attackers can still transfer your assets. The correct approach is to revoke approvals first, then reset your wallet.
◆ Misconception 3: Ignoring on-chain tracing—After a large loss, individual efforts alone cannot track fund movements; you must rely on professional institutions and law enforcement agencies, and never give up on seeking justice.
Conclusion
Gas fees and transaction security are the “first line of defense” in the blockchain world. Traps such as unlimited approvals and gas fee hijacking exploit users’侥幸心理 and lack of understanding of technical details. When interacting with various DApps, remember the three key principles: minimize approvals, pause before confirming transactions, and act quickly to mitigate losses—to effectively avoid most risks.









