
Zero Hour Tech’s Monthly Security Incident Roundup is here! According to statistics from multiple blockchain security monitoring platforms, the overall security landscape in the cryptocurrency sector remained stable in February 2026, but risks were pronounced: total losses due to security incidents amounted to approximately $228 million, with $126 million attributed to hacker attacks and smart contract vulnerabilities, and $102 million linked to phishing scams and Rug Pulls. A total of 18 protocol hacks occurred, representing a 9.2% decrease from the previous month. Thirteen phishing and authorization hijacking incidents took place, accounting for 41.9% of all incidents that month—multiple AI-simulated phishing attacks caused significant losses and were the primary driver behind the rise in scam-related losses. Hacker groups continue to shift their focus toward low-cost, high-reward social engineering attacks, with AI-generated phishing pages becoming increasingly common; individual investors and smaller projects have become the primary targets.
Regarding hacker attacks
Six typical security incidents
• CrossCurve cross-chain bridge contract verification vulnerability attack
Amount lost: Approximately $3 million
Incident Details: On February 1–2, the decentralized cross-chain protocol CrossCurve suffered a hack. The attacker exploited a gateway validation bypass vulnerability in the expressExecute function of the ReceiverAxelar contract to forge cross-chain messages, unauthorizedly unlocking and stealing tokens from the protocol’s PortalV2 contract across multiple chains, resulting in total losses of approximately $3 million. Following the incident, the CrossCurve team immediately suspended cross-chain services, patched the vulnerability, and disclosed 10 addresses that received the stolen tokens. They offered a 10% bounty for funds returned within 72 hours. The situation is now under control, and部分 stolen EYWA tokens have been frozen by exchanges and are no longer tradable.
• Vibe Coding Smart Contract AI Code Vulnerability Attack (Moonwell Protocol)
Loss amount: approximately $1.78 million
Event Details: On February 18, the DeFi protocol Moonwell was hacked due to a critical vulnerability in smart contract code generated by Claude Opus 4.6, which incorrectly set the price of cbETH at $1.12 (actual price ~$2,200). The attacker exploited this price discrepancy to over-borrow, resulting in approximately $1.78 million in losses. Security researchers identified this as the first on-chain security incident caused by Vibe Coding. Following the incident, the project team removed the affected contracts, initiated vulnerability remediation, and strengthened manual auditing of AI-generated code.
• YieldBloxDAO Oracle Manipulation Attack
Amount lost: approximately $10 million
Event Details: On February 21, the Stellar chain-based lending protocol YieldBloxDAO was hacked. The attacker manipulated the prices of underlying liquidity tokens, exploiting oracle price feed anomalies to execute malicious over-collateralized loans, resulting in approximately $10 million in asset losses. Following the incident, the project team suspended protocol services and partnered with security firms to trace stolen assets and patch the vulnerability.
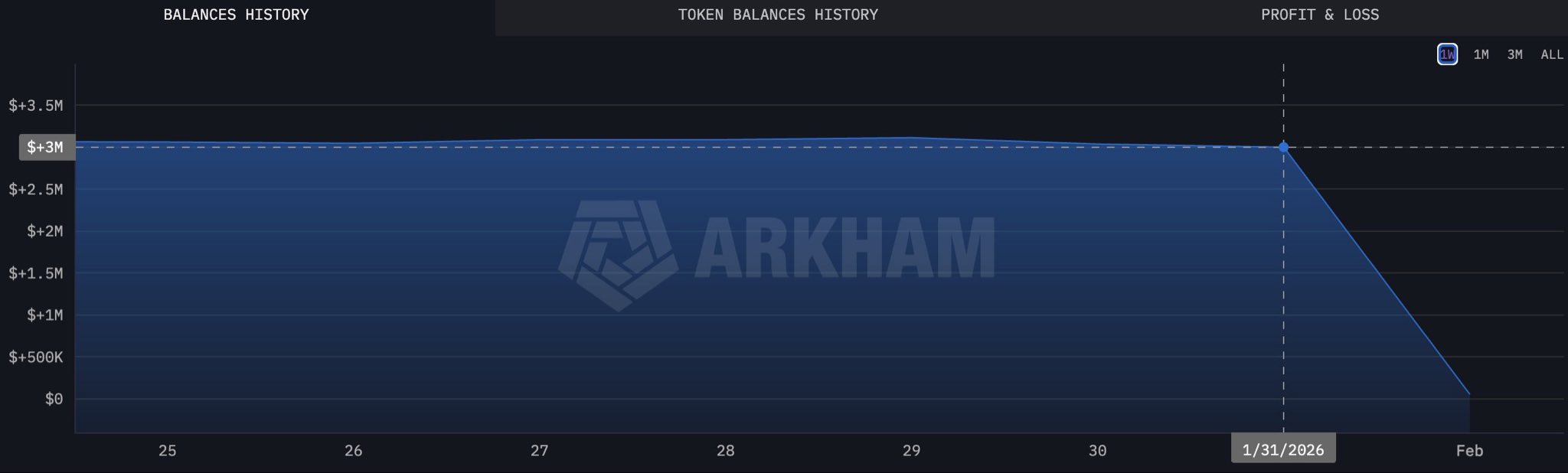
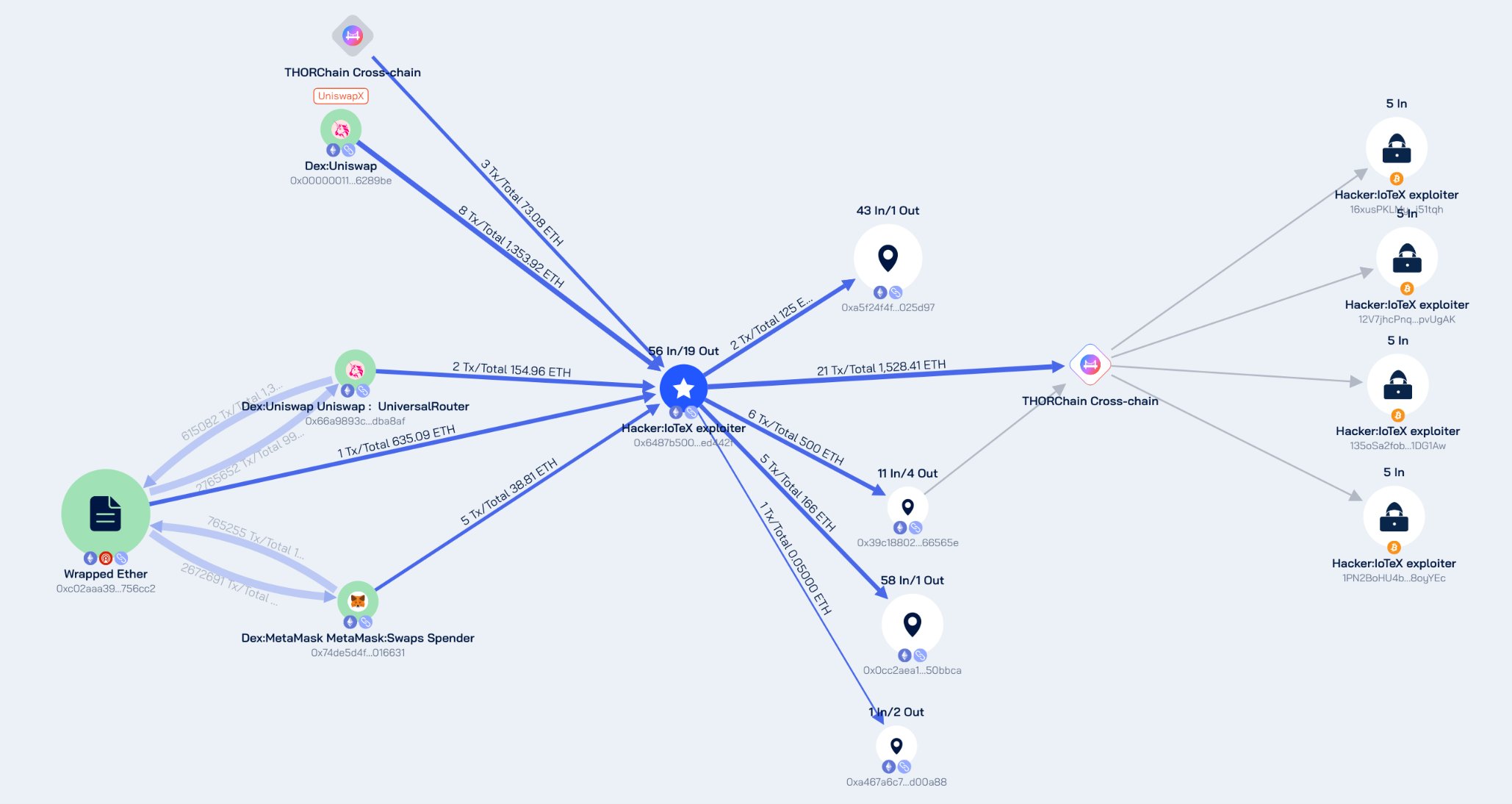
• IoTeX Token Vault Private Key Compromise Attack
Loss amount: approximately $4.4 million
Event Details: On February 21, the ioTube cross-chain bridge of the IoTeX ecosystem was hacked. The attacker gained access to the private key of the Ethereum side validator owner, successfully compromising the related smart contracts and stealing various crypto assets from the pools. IoTeX officially issued multiple updates, confirming that the actual loss amounted to approximately $4.4 million, with 99.5% of the abnormal minted tokens intercepted or permanently frozen. Following the incident, the project team immediately suspended the cross-chain bridge and related trading functions, initiated a mainnet upgrade, blacklisted 29 malicious addresses, and collaborated with the FBI and law enforcement agencies from multiple countries to conduct a global asset tracking effort. The team has committed to 100% full reimbursement for affected users and has since fully restored operations.
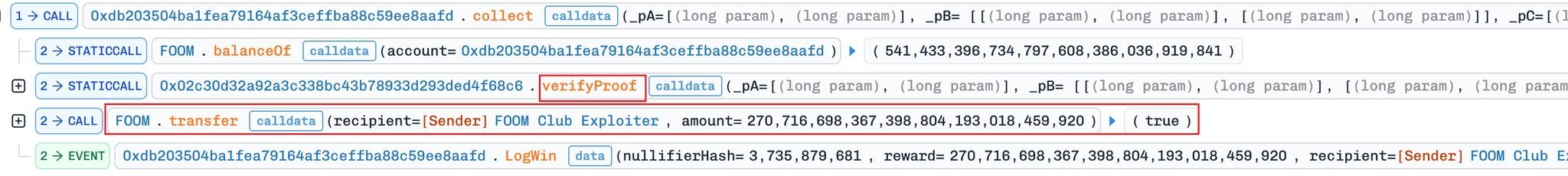
• FOOMCASH impersonation attack incident
Loss amount: approximately $2.26 million
Event Details: On February 26, the FOOMCASH project on both the Base and Ethereum chains suffered a copycat attack. The attacker exploited an incorrect configuration of zkSNARK verification keys—similar to the previous Veil Cash incident (improper Groth16 verifier parameters)—to forge proofs and steal a large number of tokens. Losses amounted to approximately $427,000 on the Base chain and $1.833 million on the Ethereum chain (some funds appear to have been rescued by white-hat actors), resulting in total losses of approximately $2.26 million. Following the incident, the project team immediately suspended related services and launched an investigation.

• Seneca DeFi protocol arbitrary call vulnerability attack
Loss amount: approximately $6.5 million
Event details: On February 28, the DeFi protocol Seneca was exploited due to an arbitrary call vulnerability, resulting in initial estimated losses of over 1,900 ETH, valued at approximately $6.5 million. Following the attack, the address associated with the hacker transferred 1,537 ETH (approximately $5.3 million) back to Seneca’s deployment address, while the remaining 300 ETH (approximately $1.04 million) were moved to a new address. The project team is currently working on patching the vulnerability and conducting an asset audit.
Rug Pull / Phishing Scam
Eight typical security incidents
(1) On February 10, victims with addresses starting in 0x6825 signed a malicious "increaseAllowance" transaction on BSC, resulting in a loss of $118,785 in BUSD. Most people are cautious about authorization signatures and approval requests, but "increaseAllowance" is the same trap—just with a less common name.
(2) On February 17, address poisoning/similar recipient scams returned. On Ethereum, 0xce31…b89b sent approximately $599,714 to an incorrect, similarly matching address.
Expected: 0x77f6ca8E…a346
Error: 0x77f6A6F6…A346
(3) On February 18, victims with addresses starting in 0x308a approved a malicious USDT transaction (approve(address,uint256)), resulting in approximately $337,069 in USDT being transferred to the scammer’s wallet.
(4) On February 18, a victim sent $157,000 to a similar address after copying a compromised transaction history.
Expected: 0xa7a9c35a…03F0 → Sent to: 0xa7A00BD2…03F0
(5) On February 25, victims with addresses starting with 0xb30 lost $388,051 on Ethereum after signing a phishing token approval.
(6) Phishing scam involving counterfeit hardware wallet verification
Time: February 12
Incident Type: Hackers forged the official verification page of a major hardware wallet and sent “Wallet Security Alert” emails and text messages, tricking users into entering their seed phrases and private keys for “security verification.” As a result, the attackers successfully obtained seed phrases from multiple users and stole assets from their accounts, with total losses amounting to approximately $950,000.
(7) Fake DEX Address Hijacking Rug Pull
Time: February 17
Nature of the incident: Hackers manipulated user transfer addresses and forged DEX transaction interfaces to deceive users into sending funds to fraudulent addresses. Immediately after the transfers were completed, the stolen funds were consolidated into multiple anonymous addresses. Total losses amounted to approximately $600,000 in USDT, affecting over 200 victims. Monitoring indicates that the maximum loss per individual victim reached approximately $600,000.
(8) Phishing scam using a fake Uniswap official website
Date: February 19 – February 26
Incident Type: Hackers purchased Google search ads to create a phishing website that closely mimics the official Uniswap interface. They drove traffic through social media ads and direct messages, tricking users into clicking links and authorizing access. Using the AngelFerno wallet draining tool, they systematically stole users’ crypto assets. Some victims were deceived because the fake domain appeared visually indistinguishable from the legitimate URL. Over 1,000 victims were targeted in a single month, with total losses amounting to approximately $1.8 million.
Summary
In February 2026, blockchain security risks were characterized by continued high frequency of contract attacks and increasingly sophisticated scam techniques. Hacker attacks primarily targeted oracle manipulation, cross-chain bridge security, contract permission vulnerabilities, and code defects, with growing instances of vulnerability reuse and imitation attacks, significantly increasing threats to medium- and small-sized protocols.
Scammers continue to primarily rely on phishing authorization, fake websites, and Ponzi scheme exits. AI-generated impersonated pages and ad hijacking have further increased the stealth of these scams, making it increasingly difficult for ordinary users to identify them.
ZeroTime Security Team recommends: Individual users should exercise caution when granting permissions, verify official addresses, and avoid suspicious links and high-risk projects; project teams should strengthen contract audits, private key management, and permission isolation, with particular attention to oracle and cross-chain security; at the industry level, enhance threat intelligence sharing and improve end-to-end defense capabilities to collectively safeguard ecosystem security.










