Author: Thejaswini M A
Article translation: Block Unicorn
Foreword
What happens when a company shifts from defense to offense, changes its stance, and refines its messaging?
We know this because Microsoft has long claimed it had no ill will toward Linux. Yet it began appearing at government procurement meetings, delivering security briefings on how open-source software poses a threat to national infrastructure. Google also spent a decade telling publishers it was merely organizing information. Yet it began funding research that found news paywalls harm democracy. What was once “We built something different” became “They built something dangerous.” If you’re good enough and have the right connections, you don’t even need to outperform your competitors technologically—you just need to ensure the people who ultimately decide technology’s direction trust you more than they trust your rivals.
Canton is doing this now, while the cryptocurrency industry has largely been excluded from the discussion.
In January this year, I noted that Canton chose efficiency over freedom, and institutions followed suit. At the time, the argument was that Canton and Ethereum served different audiences and addressed distinct problems—a perspective that was accurate then. However, Canton’s trajectory has since changed.
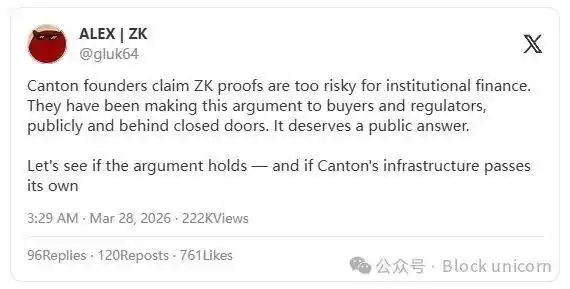
The founders of Canton have consistently argued in public forums and private meetings with buyers and regulators that zero-knowledge proofs (ZKPs) pose an unacceptable risk to mission-critical financial systems. I believe this is a regulatory positioning campaign coordinated with a fundraising effort that attracted major investors including Goldman Sachs, Citadel, DRW, Circle, Paxos, and Polychain. JPM Coin launched on Canton in January. Visa joined as a super validator in March. On March 27, LayerZero became the first interoperability protocol to run directly on Canton, enabling institutions to route tokenized assets across more than 165 public blockchains. The fully diluted valuation of the $CC token is $5 billion.
These aren’t the focus. What I want to emphasize is how Canton is currently trying to influence the scope of technologies banks can use. So far, Canton is the only one engaging in this discussion.
Arguments Against ZK
Canton's argument is roughly as follows: Zero-knowledge proof vulnerabilities may be difficult to detect because the underlying data is private. If such vulnerabilities spread silently without audit trails or accountability mechanisms, they could constitute a fatal flaw.
They cited a real-world example: On April 16, 2025, Solana patched a zero-day vulnerability in its zero-knowledge proof (ZKP)-based "confidential transfers" feature, which could have allowed attackers to mint an unlimited supply of tokens. It is currently unclear whether the vulnerability was exploited.
The person making this argument is Shaul Kfir, co-founder and COO of Canton and a co-author of libsnark, a C++ library for creating zk-SNARK proofs. Is he dismissing a technology he doesn’t understand? Unlikely.
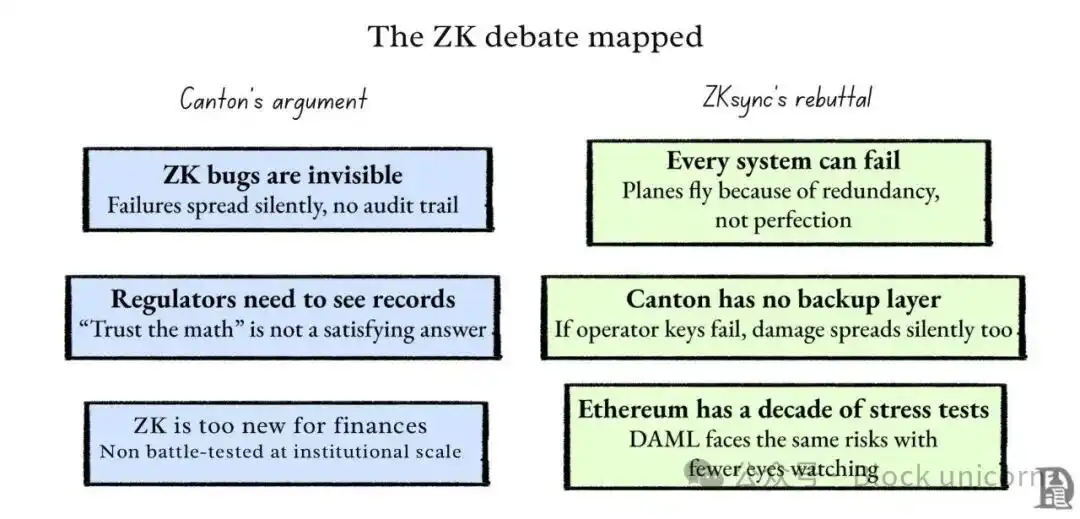
His argument is that when zero-knowledge proofs fail, no one will notice. The data remains private, errors are concealed, and by the time someone detects the issue, the damage has already spread. For regulators, whose responsibility is to prove that banks are not laundering money, a system that “trusts the math” is unsatisfactory. They need to be able to examine the records.
In Canton's model, the only entities that can view these records in real time are the super verifiers—the same institutions that would become single points of failure if their keys were compromised.
In Canton's model, the only entities capable of viewing these records in real time are super verifiers, and if the keys of these institutions are compromised, they become a single point of failure.
This argument doesn’t need to be flawless to be effective—it just needs to sound reasonable enough to sway those already skeptical of cryptocurrency. For those who have built their careers on paper records and audit trails, any major flaw in cryptocurrency renders the evidence meaningless. You don’t need to win the technical debate, but you still need to make the other side feel that the alternative carries significant risk.
What's the issue?
Last week, ZKsync co-founder Alex Gluchowski publicly responded to this viewpoint, stating that Canton’s logic is overly extreme. If we were to avoid using any technology simply because it has vulnerabilities that could lead to catastrophic consequences, we should have grounded all commercial flights and ceased manufacturing aircraft entirely back in the 1970s. Fly-by-wire systems have vulnerabilities, engine controllers have vulnerabilities, and autonomous software has previously failed in ways that resulted in fatalities. Yet we did not stop flying. Instead, we build aircraft with multiple independent systems so that when one system fails, another can detect and compensate for the failure, preventing crashes.
Did Canton address what happens after an operator's key is compromised? Currently, there is no backup system or second-layer security mechanism to verify operations. Trusted operators are the only line of defense. If this line fails, damage will spread silently across the network without oversight. According to Canton’s own standards, this architecture is precisely what should raise regulatory concerns.
The solution to technical flaws is never to find a perfectly reliable technology, but to build systems that anticipate failures and ultimately survive them. The safety of a nuclear reactor does not stem from its software never crashing, but from the fact that a disaster only occurs if five other components fail simultaneously when one does. The same applies to pacemakers and commercial aircraft. The engineering principle here is redundancy and isolation: constructing multiple independent system layers so that when one fails, another can promptly compensate. At the same time, system design must ensure that when a failure occurs, the damage is contained within the system and does not spread to all connected components.
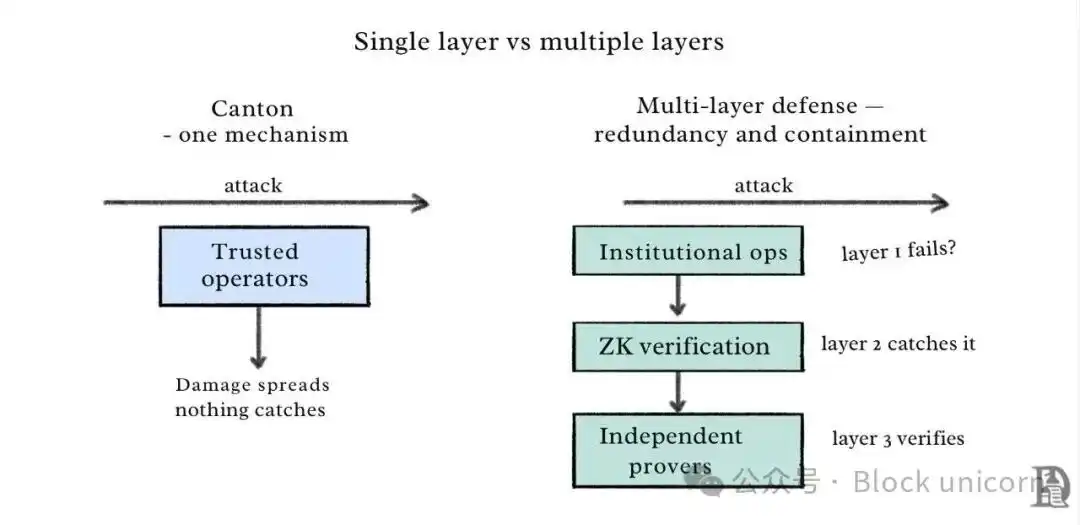
Grubhofsky applied the same test to Canton’s own architecture. Canton’s privacy and integrity model relies on a single mechanism: data isolation among participants by a trusted operator. This model lacks an encryption verification layer or independent audit mechanisms. If the operator’s key is compromised, tampered states would silently propagate through the opaque UTXO chain with no monitoring in place. According to Canton’s own logic—a single point of failure with catastrophic consequences—this is precisely the architecture regulators should be concerned about.
ZK vulnerabilities, Solana zero-day exploits—these are real issues. But the response to error-prone components is not to replace them with another single point of failure disguised as an institutional solution. The correct approach is to build multiple independent layers of defense, design systems to limit the blast radius of attacks, and subject them to adversarial stress testing through a decade of public scrutiny. The very existence of the EVM today is the result of over a decade of sustained adversarial testing by the world’s most sophisticated attackers, costing hundreds of billions of dollars. Every maturity concern Canton raises about ZKPs applies equally to DAML—but far fewer mitigation options are available.
These cannot end the debate, but they redefine its focus. One institutional risk management approach advocates, in the context of regulatory rulemaking, that it should be the only permitted method.
Canton's argument completely ignores a key point: zero-knowledge technology does not operate at a fixed level of risk; rather, it becomes more secure as more participants engage in verification. Its core mechanism lies in the fact that zero-knowledge proofs allow individuals to prove the truth of a statement without revealing the underlying data. Verifiers check the proof itself, not the data. The more independent verifiers validate the same proof system, the harder it becomes to detect any vulnerabilities or tampering. In 2025, Nethermind formally verified the correctness of ZKsync’s on-chain zero-knowledge verifier using EasyCrypt, completing the first such formal proof in a live zero-knowledge system. This demonstrates that adversarial review of open systems, over time, yields significantly stronger outcomes.
Canton’s model is precisely the opposite. Trust is concentrated among a small number of approved operators, and their cumulative effect is not the same. A closed system composed of approved validators has limited capacity for censorship resistance. Who holds the authority to validate is far from a trivial matter in security discussions. As the validator network grows, open zero-knowledge (ZK) systems become harder to compromise. The strength—and vulnerability—of a permissioned trust model depends on its weakest operator. A systematic analysis of known attacks in 2024 found that approximately 96% of recorded circuit-layer vulnerabilities in ZK systems stem from under-constrained circuits, and open adversarial testing is specifically designed to uncover and eliminate such vulnerabilities. The vulnerabilities Canton points out are real. An open ecosystem is precisely the mechanism for discovering and fixing these vulnerabilities. Keeping the ecosystem closed does not make vulnerabilities disappear—it only reduces the number of people paying attention to them.
Canton is no longer sticking to tradition.
Recall what I mentioned earlier: position Canton as a parallel system that addresses different problems for different user groups, rather than competing with Ethereum for the same market.
LayerZero’s integration has changed this landscape. It enables Canton’s traditional financial institutions to route tokenized securities, digital bonds, and stocks across more than 165 public blockchains while meeting compliance and confidentiality requirements. Investors can now use stablecoins on external public chains to purchase tokenized real-world assets developed natively on Canton. Canton’s native tokenization tools can access other ecosystems for secondary market trading.
Bryan Pellegrino, CEO of LayerZero Labs, said: "Canton has already built the infrastructure for traditional finance, processing over $350 billion in U.S. Treasury repurchase transactions daily. LayerZero’s mission is to ensure these assets can circulate across all markets and all blockchains globally."
Canton is entering the realm of cryptocurrency liquidity pools rather than staying away from them, creating a tension. Canton’s founders are engaged in private discussions with regulators, arguing that zero-knowledge proofs are too risky for institutional finance. Meanwhile, assets based on Canton are flowing into a public blockchain ecosystem via LayerZero, where zero-knowledge proofs form a foundational infrastructure—including products positioned as institutional alternatives to Canton.
What does this mean in practice? A bank holds tokenized U.S. Treasuries on Canton. Through LayerZero, these Treasuries can now be transferred to Ethereum or Arbitrum, where they can be used as collateral on Aave, borrowed against on Ondo, or serve as underlying assets for DeFi lending protocols. This tool maintains institutional-grade compliance and regulatory adherence on Canton’s network, while unlocking crypto-native liquidity. Ondo Finance has already implemented similar functionality: its tokenized Treasury product, USDY, operates across four blockchains with $700 million in total value locked (TVL), available as collateral in DeFi. Canton can now directly access the same ecosystem. Banks gain yield and composability; DeFi gains institutional-grade collateral; and Canton can argue to regulators that zero-knowledge proofs (ZKPs) are too risky—while still enabling its assets to move freely on the blockchains it supports.
If the goal is regulatory capture, then simultaneously leveraging the infrastructure of cryptocurrency while arguing to regulators that its foundational privacy technologies constitute a systemic threat is itself a coherent strategy, not a contradiction. You can say this because the zero-knowledge camp has not yet organized an equivalent-scale response.
As of last week, the most notable contribution from the ZK camp in regulatory discussions was Gromovsky’s post. It was indeed a strong post. Canton has lawyers involved in these meetings and connections at Goldman Sachs. For a decade, they have been working to build trust with regulators, whose approvals determine what a systemically important bank is permitted to operate.
What risks does Ethereum face?
This is not an abstract concept for anyone holding Ethereum or following the institutional tokenization trend.
If Canton wins the regulatory debate—that is, if zero-knowledge proofs are classified as too risky, too obscure, and too novel to fit within the regulatory framework for systemically important institutions—then Ethereum’s path to institutional settlement will be shut off before it can fully open. The $100 trillion tokenization opportunity mentioned by Larry Fink in his annual letter will continue to rely on permissioned payment systems. Ethereum can settle decentralized finance (DeFi). That is important, but it is not the global financial settlement layer.
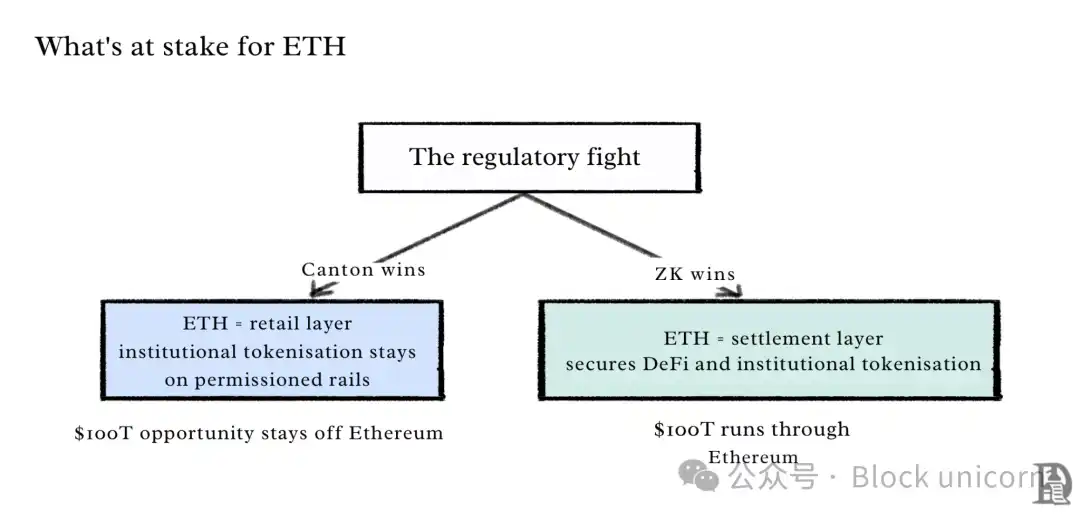
If the zero-knowledge (ZK) camp prevails—that is, if zkSync’s Prividium and emerging institutional-grade zero-knowledge infrastructure receive regulatory approval simultaneously with or prior to Canton’s model—the landscape will undergo a major transformation. The blockchains securing decentralized finance (DeFi) will begin securing tokenized institutional assets. Ethereum’s position within the financial system will be elevated. Assets once seemingly at risk of being marginalized at the institutional level will ultimately become foundational to it.
Visa has just joined Canton as a super validator node. DTCC is advancing toward production. Broadridge is already processing hundreds of billions of dollars in daily transaction volume on the Canton platform. Participating institutions include Goldman Sachs, BNP Paribas, Tradeweb, and Citadel Securities. The institutional payments flywheel is in motion and has been running long enough to generate real momentum.
In January this year, I said that Canton’s goal is not to replace Ethereum. That remains unchanged today. Its goal is more specific and more effective than replacing Ethereum: it aims to ensure that Ethereum never has the opportunity to compete in the same market—not by building a better product, but by securing certification first. It seeks to obtain certification before regulators intervene in the technology, and then use that certification as the framework to establish evaluation standards for all subsequent related technologies.
Cryptocurrencies have always competed based on visible metrics such as total value locked (TVL), fees, user count, trading volume, and token price. Canton has never competed on these metrics. It is built on trust—an intangible asset that accumulates slowly and is nearly impossible to replicate once possessed by others.
Interestingly, zero-knowledge proofs were invented precisely to address the very issue Canton is leveraging. If mathematics can prove something without revealing the result, you don’t need to trust anyone. Canton’s argument is that mathematics itself is not trustworthy—so institutions should be trusted instead. The last person named as a risk wins.










