Original author: @Cointelegraph
AididiaoJP, Foresight News
This article explains how BIP-360 reshapes Bitcoin's quantum defense strategy, analyzes its improvements, and explores why it has not yet achieved full post-quantum security.
Key Points
- BIP-360 formally integrates quantum resistance into Bitcoin's development roadmap for the first time, marking a cautious and incremental technological evolution rather than a radical overhaul of the cryptographic system.
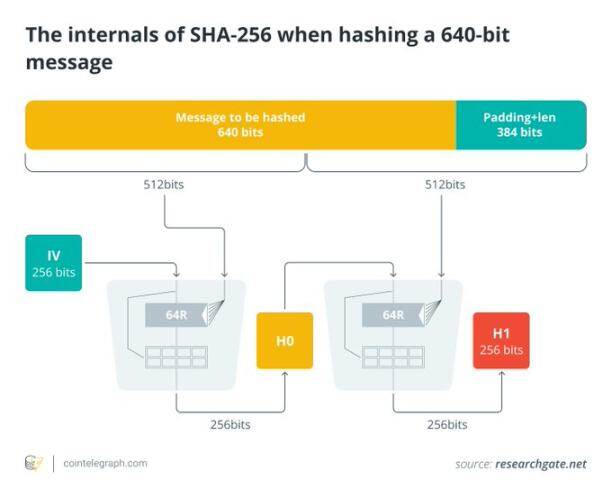
- Quantum risk primarily threatens exposed public keys, not the SHA-256 hashing algorithm used by Bitcoin. Therefore, minimizing public key exposure has become a core security focus for developers.
- BIP-360 introduces a Pay-to-Merkle-Root (P2MR) script that eliminates the key path spending option from the Taproot upgrade, mandating that all UTXOs be spent via the script path to minimize exposure of elliptic curve public keys.
- P2MR retains the flexibility of smart contracts and continues to support multisignature, timelocks, and complex custody structures through Tapscript Merkle trees.
Bitcoin's design philosophy enables it to withstand severe economic, political, and technological challenges. As of March 10, 2026, its development team is addressing an emerging technological threat: quantum computing.
The recently released Bitcoin Improvement Proposal 360 (BIP-360) formally incorporates quantum resistance into Bitcoin’s long-term technical roadmap for the first time. Although some media outlets have framed it as a major overhaul, the reality is more cautious and incremental.
This article will explore how BIP-360 reduces Bitcoin’s quantum risk exposure by removing Taproot’s key path spending functionality through the introduction of Pay-to-Merkle-Root (P2MR) scripts. It aims to clarify the improvements offered by this proposal, the trade-offs it introduces, and why it has not yet enabled Bitcoin to achieve full post-quantum security.
Sources of quantum computing threats to Bitcoin
Bitcoin's security is built on cryptography, primarily relying on the Elliptic Curve Digital Signature Algorithm (ECDSA) and Schnorr signatures introduced via the Taproot upgrade. Classical computers cannot reverse-engineer a private key from a public key within a feasible time frame. However, a sufficiently powerful quantum computer running Shor's algorithm could potentially solve the elliptic curve discrete logarithm problem, thereby compromising private key security.
The key differences are as follows:
- Quantum attacks primarily threaten public-key cryptography systems, not hash functions. The SHA-256 algorithm used by Bitcoin is relatively robust against quantum computing. Grover's algorithm provides only quadratic speedup, not exponential speedup.
- The real risk occurs when the public key is made public on the blockchain.
Based on this, the community generally considers exposing public keys to be the primary quantum risk.
Potential vulnerabilities of Bitcoin in 2026
Different types of addresses on the Bitcoin network face varying levels of future quantum threats:
- Reused address: When funds from this address are spent, its public key becomes publicly visible on the chain, making it vulnerable if a cryptographically relevant quantum computer (CRQC) emerges in the future.
- Legacy pay-to-public-key (P2PK) outputs: Early Bitcoin transactions directly embedded public keys into the transaction outputs.
- Taproot key path spending: The Taproot upgrade (2021) introduced two spending paths: a concise key path (which reveals an adjusted public key when spent) and a script path (which reveals the specific script via a Merkle proof). Among these, the key path is the primary theoretical vulnerability against quantum attacks.
BIP-360 is specifically designed to address the issue of key path exposure.

The core of BIP-360: Introducing P2MR
BIP-360 introduces a new output type called Pay-to-Merkle-Root (P2MR). Structurally inspired by Taproot, it makes a key modification: completely removing the key path spending option.
Unlike Taproot commitments to an internal public key, P2MR commits only to the Merkle root of the script tree. The process for spending a P2MR output is:
Reveal a leaf script in the script tree.
Provide a Merkle proof to verify that this leaf script belongs to the committed Merkle root.
Throughout the entire process, there is no spending path based on the public key.
The direct impacts of removing the key path cost include:
- Avoid exposing your public key by performing signature verification directly.
- All spending paths rely on hash-based commitments with stronger quantum resistance.
- The number of elliptic curve public keys permanently stored on the chain will significantly decrease.
- Compared to schemes relying on the elliptic curve assumption, hash-based methods offer significant advantages in resisting quantum attacks, thereby substantially reducing the potential attack surface.
Features reserved by BIP-360
A common misconception is that abandoning key path spending weakens Bitcoin’s smart contract or scripting capabilities. In fact, P2MR fully supports the following features:
- Multisig configuration
- Time lock
- Conditional Payment
- Asset inheritance plan
- Advanced custody arrangements
BIP-360 implements all the above features using a Tapscript Merkle tree. This approach retains full script capabilities while eliminating the convenient but potentially risky direct signature path.
Satoshi Nakamoto briefly mentioned quantum computing in early forum discussions, suggesting that if it became a reality, Bitcoin could migrate to stronger signature schemes. This indicates that designing for future upgrades with flexibility was part of the original design philosophy.
Practical implications of BIP-360
Although BIP-360 appears to be a purely technical improvement, its impact will extend broadly across wallets, exchanges, and custodial services. If adopted, it will gradually reshape how new Bitcoin outputs are created, spent, and secured, particularly affecting users who prioritize long-term quantum resistance.
- Wallet support: Wallet apps may offer an optional P2MR address (possibly starting with "bc1z") as a "quantum-resistant" option for users to receive new coins or store long-term holdings.
- Transaction fees: Since script paths introduce additional witness data, P2MR transactions may incur slightly higher fees compared to Taproot key path spending, reflecting a trade-off between security and transaction efficiency.
- Ecosystem collaboration: Full deployment of P2MR requires coordinated updates from wallets, exchanges, custodians, hardware wallets, and other stakeholders. Planning and coordination efforts must begin several years in advance.
Background: Governments around the world have begun to recognize the risk of "harvest now, decrypt later"—the practice of collecting and storing encrypted data today in anticipation of decrypting it in the future once quantum computers become available. This strategy mirrors the same concern regarding Bitcoin’s exposed public keys.
The clear boundaries of BIP-360
Although BIP-360 enhances Bitcoin's defense against future quantum threats, it is not a complete cryptographic overhaul. Understanding its limitations is equally crucial:
- Existing assets do not automatically upgrade: All old unspent transaction outputs (UTXOs) remain vulnerable until users actively transfer their funds to P2MR outputs. Therefore, the migration process depends entirely on individual user action.
- No introduction of post-quantum signatures: BIP-360 does not adopt lattice-based signatures (such as Dilithium or ML-DSA) or hash-based signatures (such as SPHINCS+) to replace the existing ECDSA or Schnorr signatures. It only removes the public key exposure pattern introduced by Taproot key paths. A comprehensive transition to post-quantum signatures at the base layer would require a much larger protocol change.
- Absolute quantum immunity cannot be guaranteed: Even if a practical CRQC were to emerge suddenly, defending against its impact would require large-scale, high-intensity coordination among miners, nodes, exchanges, and custodial institutions. Long-dormant "sleeping coins" could trigger complex governance challenges and place significant strain on the network.
Motivations behind developers' forward-looking strategic planning
The technological development path of quantum computing remains highly uncertain. Some believe its practical application is still decades away, while others point to accelerating progress, evidenced by IBM’s goal of achieving fault-tolerant quantum computers by the late 2020s, Google’s breakthroughs in quantum chips, Microsoft’s research into topological quantum computing, and the U.S. government’s deadline for transitioning cryptographic systems by 2030–2035.
The migration of critical infrastructure requires a lengthy time frame. Bitcoin developers emphasize that systematic planning must be carried out across all stages—from BIP design and software implementation to infrastructure adaptation and user adoption. Waiting until the quantum threat becomes imminent could leave insufficient time to act, resulting in a reactive and vulnerable position.
If the community reaches broad consensus, BIP-360 could be advanced through a phased soft fork approach:
- Enable the new P2MR output type.
- Wallets, exchanges, and custodians are gradually increasing their support for it.
- The user gradually migrated their assets to a new address over several years.
This process is similar to the path taken by SegWit and Taproot upgrades, which evolved from optional to widespread adoption.
Widespread discussion around BIP-360
There is ongoing discussion within the community regarding the urgency of implementing BIP-360 and its potential costs. Key issues include:
- Is a slight increase in fees acceptable for long-term holders?
- Should institutional users lead the way in asset migration to set a positive example?
- How should "sleeping" bitcoins that will never be moved be properly handled?
- How should a wallet app accurately communicate the concept of "quantum safety" to users—without causing unnecessary alarm, while still providing meaningful information?
These discussions are still ongoing. The proposal of BIP-360 has significantly advanced the in-depth exploration of related issues, but it has by no means resolved all questions.
Background: The theoretical possibility that quantum computers could break current cryptography dates back to 1994, when mathematician Peter Shor introduced Shor's algorithm—long before Bitcoin's emergence. Therefore, Bitcoin's planning for future quantum threats is essentially a response to this theoretical breakthrough that has existed for over three decades.
Current actions users can take
Currently, quantum threats are not imminent, and users need not be overly concerned. However, taking some precautionary measures is beneficial:
- Follow the principle of not reusing addresses.
- Always use the latest version of the wallet software.
- Stay updated on developments related to Bitcoin protocol upgrades.
- Keep an eye on when your wallet app begins supporting P2MR address types.
- Users holding large amounts of Bitcoin should quietly assess their risk exposure and consider developing a corresponding contingency plan.
BIP-360: A First Step Toward a Quantum-Resistant Future
BIP-360 marks the first concrete step toward reducing quantum risk exposure at the Bitcoin protocol level. It redefines how new outputs are created, minimizing accidental public key exposure and laying the groundwork for future long-term migration planning.
It does not automatically upgrade existing Bitcoin, preserves the current signature system, and highlights the fact that achieving true quantum resistance requires a careful, coordinated, and ongoing effort across the entire ecosystem. This depends on long-term engineering practices and phased community adoption, rather than being achievable through a single BIP proposal.










