In 2025, the Web3 world is not short of grand narratives, especially with regulatory transformations being completed and stablecoins gradually integrated into the TradFi system. Discussions around "compliance," "integration," and "rebuilding the next phase of order" have almost formed the main theme of the year (Extended reading: *"2025 Global Crypto Regulatory Landscape: The Beginning of the Integration Era, A Year of Convergence Between Crypto and TradFi*》)。
." However, behind these seemingly high-level structural changes, a more fundamental yet long-neglected issue is surfacing, namely: the account itself is becoming the systemic risk source for the entire industry.
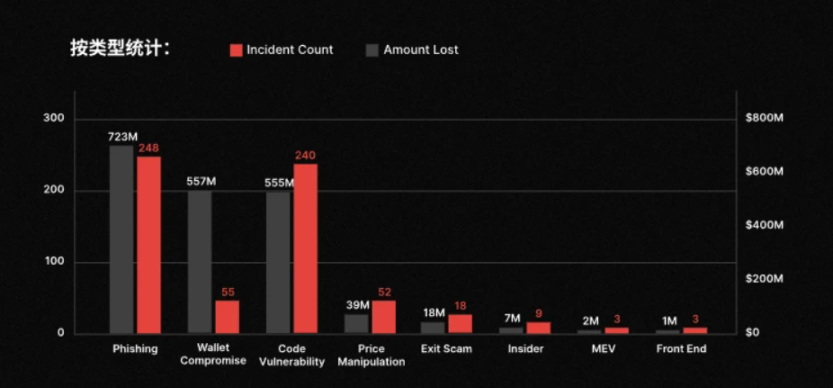
Recently, CertiK's latest security report highlighted a striking figure: 2025 saw a total of 630 security incidents in the Web3 space, resulting in cumulative losses of approximately $3.35 billion. If one were to stop at this aggregate figure, it might seem like just another annual reiteration of the severity of the security landscape. However, a deeper breakdown of these incidents reveals a more alarming trend:
a significant portion of the losses did not stem from complex contract vulnerabilities or direct protocol breaches, but rather concentrated on a more primitive and unsettling level—phishing attacks . Over the year, there were 248 phishing-related incidents causing losses of approximately $723 million, even slightly exceeding code vulnerability attacks (240 incidents, approximately $555 million).
In other words, in many user loss cases, the blockchain itself did not fail, cryptography was not broken, and transactions were fully compliant with the rules.
What truly went wrong was the account itself.
**1. EOA Accounts: Becoming Web3's Largest "Historical Issue"**
Objectively speaking, whether in Web2 or Web3, phishing has always been the most common way for people to lose funds.
The difference lies in the fact that Web3, with its introduction of smart contracts and irreversible execution mechanisms, often leads to more extreme outcomes when such risks occur. To understand this, one must revisit Web3's most fundamental and core account model, the EOA (Externally Owned Account):
its design logic is extremely pure—private key equals ownership, signature equals intent. Whoever holds the private key has complete control over the account. This model undoubtedly held revolutionary significance during the early stages, bypassing custodial institutions and intermediary systems to directly return asset sovereignty to individuals.
Yet this design also implicitly assumes an extremely radical premise, which means: in the EOA model, users will not fall for phishing scams, will not make operational errors, and will not make wrong judgments under fatigue, anxiety, or time pressure. As long as a transaction is signed, it is regarded as the user's genuine, fully understood expression of intent.
Reality, however, is clearly not so.
The frequent security incidents in 2025 are the direct result of this assumption being repeatedly invalidated. Whether it’s being tricked into signing malicious transactions or transferring funds without fully verifying details, the common thread is not the complexity of the technology but rather the account model’s lack of tolerance for human cognitive limitations (Extended reading: *"From EOA to Account Abstraction: Will the Next Leap in Web3 Happen in the Account System?*》)。
). A typical scenario involves the long-standing chain-wide Approval authorization mechanism. When users authorize a specific address, they essentially allow the address to transfer assets from their account without seeking further confirmation. While this design is efficient and straightforward in contract logic, it frequently becomes the starting point for phishing and asset drain in real-world usage.
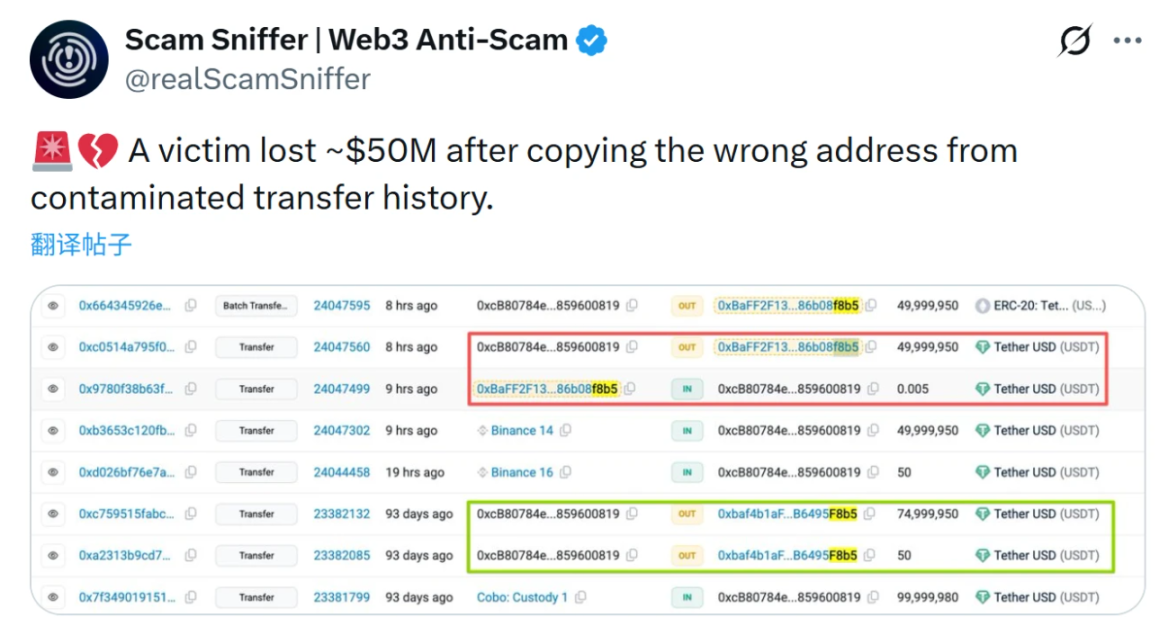
For instance, in a recent address poisoning incident involving $50 million, the attacker did not attempt to hack the system but instead crafted a “similar address” with highly identical first and last four characters, tricking users into transferring funds hastily. The flaw in the EOA model becomes evident here; it's genuinely difficult for anyone to ensure, in a very short time, that they have verified a string of long, meaningless characters.
Ultimately, the underlying logic of the EOA model simply does not care whether you were scammed—it only cares about one thing: whether you “signed.”
This is why the success of address poisoning, a typical attack case, has made frequent headlines over the past two years. The attacker doesn’t need to resort to labor-intensive 51% attacks; they simply need to create a sufficiently deceptive address for poisoning and wait for the user to carelessly copy, paste, and confirm.
After all, the EOA cannot determine whether this is an unfamiliar address that has never interacted before, nor can it recognize whether this operation significantly deviates from historical behavior patterns. To the EOA, this is just a legitimate, valid transaction instruction that must be executed. Thus, a long-overlooked paradox is becoming unavoidable: Web3 is extremely secure at the cryptographic level but exceptionally fragile at the account level.
From this perspective, the $3.35 billion industry loss in 2025 cannot simply be attributed to "user carelessness" or "advanced hacking methods." Instead, it signals that the historical debts of the account model are becoming increasingly evident as it scales to real financial proportions.
**2. The Historical Inevitability of AA: A Systematic Correction for Web3 Account Models**
After all, when massive losses occur under a system that is "operating completely as intended," this is the biggest problem in itself.
For instance, as observed in CertiK’s statistics: phishing attacks, address poisoning, malicious authorizations, and mis-signatures all share a common prerequisite—transactions are legitimate, signatures are valid, and execution is irreversible. These incidents neither violate consensus rules nor trigger abnormal states, and they even appear completely normal on block explorers.
From a system's perspective, these are not attacks but repeatedly correctly executed user instructions.
At its core, the EOA model compresses "identity," "permissions," and "risk-bearing" into a single private key. Once a signature is completed, identity is confirmed, permissions are granted, and risks are irrevocably borne. While this extreme simplification offered efficiency advantages in the early stages, it began to reveal significant systemic flaws as the scale of assets, participants, and use cases evolved.
Especially as Web3 gradually transitions into high-frequency, cross-protocol, and long-duration online usage, accounts are no longer just cold wallets used occasionally, but instead, they take on multiple functions such as payments, authorizations, interactions, and settlements. Under this premise, the assumption that "every signature represents a fully rational decision" has become increasingly hard to sustain.
From this perspective, the frequent success of address poisoning is not because attackers are smarter but because the account model lacks any buffering mechanism for human errors— the system does not inquire whether the recipient is an entity the user has never interacted with, does not check whether the transaction amount significantly deviates from historical behavior, and does not trigger delays or secondary confirmations due to abnormal operations. For EOAs (Externally Owned Accounts), as long as the signature is valid, the transaction must be executed.
In fact, traditional financial systems have already provided answers, such as transfer limits, cooling-off periods, abnormal freezes, hierarchical permissions, and revocable authorizations. These are essentially acknowledgments of a simple yet realistic fact: humans are not always rational, and account designs must incorporate buffer mechanisms for this.
It is against this backdrop that Account Abstraction (AA) emerges, revealing its essential historical significance. It functions more like a redefinition of the nature of accounts, aiming to transform accounts from passive tools that execute signatures into entities capable of managing intentions.
The core idea of AA is that accounts are no longer merely equivalent to a private key; they can incorporate multiple verification paths, set differentiated permissions for different types of operations, delay execution in the case of abnormal activity, and even regain control when specific conditions are met.
This does not represent a departure from the spirit of decentralization but rather an adjustment towards its sustainability. True self-custody does not imply that users must bear the permanent consequences of a single mistake; instead, it allows accounts to inherently possess error-tolerance and self-protection capabilities without relying on centralized custodians.
III. What can account evolution bring to Web3?
As the author has often stated, "Behind every successful scam is a user who stops using Web3, and without any new users, the Web3 ecosystem has nowhere to go."
From this perspective, neither security institutions nor wallet products, nor industry builders from other sectors, can continue to treat "user misoperation" as individual negligence. Instead, they must shoulder systemic responsibility for ensuring that the entire account system is safe, comprehensible, and fault-tolerant in real-world scenarios.
Therefore, the historical significance of AA lies precisely in this. In short, AA is not merely a technical upgrade for accounts but a systematic adjustment of security logic.
This shift first manifests in the loosening relationship between accounts and private keys. For a long time, seed phrases have been regarded as the passport to self-custody in Web3. However, in reality, this single-point key management method has repeatedly proven unfriendly to most ordinary users. By introducing mechanisms such as social recovery, AA unbinds accounts from a single private key. Users can designate multiple trusted guardians, allowing them to regain control of their accounts through verification if a device is lost or a private key becomes invalid.
When AA is combined with Passkey, it becomes possible to create an approach to account security that closely aligns with users' intuitive understanding of financial account security in traditional systems (for further reading, see " Web3 Without Seed Phrases: How AA × Passkey Could Define Crypto’s Next Decade"). 》)。
Equally important is AA's reconstruction of transaction friction. In the traditional EOA system, gas fees often constitute a hidden barrier to all on-chain operations. Through mechanisms like Paymaster, AA enables transaction fees to be covered by third parties or paid directly using stablecoins.
This means users no longer need to prepare a small amount of native tokens to complete a transfer, nor are they forced to understand the complexities of gas logic. Objectively, this seamless gas experience is not just a nice-to-have feature but a critical factor in determining whether Web3 can break out of its early adopter circle.
Additionally, AA accounts leverage the native capabilities of smart contracts to bundle previously fragmented multi-step operations into a single atomic execution. For example, in DEX trading, instead of going through multiple steps like authorization, signing, trading, and re-signing, AA accounts can consolidate these actions into a single transaction that either fully succeeds or fully fails, reducing costs and avoiding ineffective losses due to mid-process failures.
A deeper change lies in the malleability of account permissions themselves. AA accounts are no longer trapped in a binary structure of "either full control or complete loss of control" but instead can offer sophisticated permission management logic akin to traditional bank accounts. Different transaction amounts can require different levels of verification, interactions with different entities can be subjected to varying access permissions, and black-and-white lists can restrict accounts to interacting only with specific safe contracts.
This means that even in extreme cases where a private key is leaked, the account itself still has a buffer mechanism in place, preventing assets from being entirely drained in a short amount of time.
Of course, it is important to emphasize that the evolution of account security does not rely solely on the widespread adoption of AA account systems. Existing wallet products can and must also take responsibility for rectifying some of the shortcomings of the EOA model.
Take imToken as an example. Its address book feature allows frequently used and trusted addresses to be saved, so accounts no longer rely entirely on the user's on-the-spot judgment of a string of hash characters when making transfers. Instead, they prioritize selecting from the existing address book, significantly reducing the risk of transfer errors caused by manual copying, pasting, or misjudging similar addresses.
Equally critical is the "What You See Is What You Sign" principle, which has gradually become a consensus within the industry in recent years. Its core is not about presenting more information but about ensuring that the content users sign matches their expectations, understanding, and intentions, rather than being compressed into an indecipherable hash string.
Surrounding this principle, imToken has structured and made readable the contents of signatures in various key processes such as DApp login, transfers, token swaps, and authorizations, allowing users to truly understand what they are agreeing to before confirmation. This design does not alter the irreversible nature of transactions, but instead introduces a necessary rational buffer before the signature occurs, which is an indispensable step in the maturity of account systems.
1 From a broader perspective, the evolution of AA accounts is essentially reshaping the foundational assumptions for the next stage of Web3 development, enabling the blockchain to truly accommodate large-scale real users. Otherwise, 2 no matter how complex the protocols are or how grand the narratives may be, they will ultimately be repeatedly punctured by the most primitive question—whether ordinary users dare to keep their assets on-chain for the long term.
3 In this sense, AA is not a bonus for Web3 but more like a pass mark. It determines not whether the experience is good but 4 whether Web3 can evolve from an experimental system dominated by tech enthusiasts into an inclusive financial infrastructure for a broader population.
5 In conclusion,
6 $3.35 billion is essentially the tuition fee that the entire industry will pay by 2025.
7 This also reminds us that when the industry begins discussing compliance, institutional interfaces, and mainstream capital entry, if Web3 accounts remain at the state of "signature/authorization clears everything after one use," then the so-called financial infrastructure is merely built on sand.
8 The real question may not be "Will AA become mainstream?" but rather— 9 If accounts do not evolve, how much future can Web3 still carry?
10 This may be the most valuable safety insight for the entire industry to repeatedly ponder by 2025.









