What Is an Eclipse Attack and What Are Some Similar Cases in History?
2026/04/01 06:09:02
An eclipse attack is one of the most subtle yet dangerous threats in blockchain networks, where attackers isolate a node and manipulate its view of reality. This form of attack highlights a deeper truth about decentralized systems: even trustless networks rely heavily on communication integrity. By examining eclipse attacks and similar historical incidents, it becomes clear that the real battleground in crypto is not just code or capital, but control over information flow.
The Invisible War Inside Blockchain Networks
Blockchain is often described as secure, decentralized, and resistant to manipulation. That description is mostly accurate, yet it hides a quieter reality. Behind every transaction is a network of nodes constantly exchanging information. These nodes rely on each other to verify data, share updates, and maintain consensus.
This communication layer is where vulnerabilities can emerge. A blockchain is not a single system but a distributed web of connections. Each node only connects to a limited number of peers at any given time due to bandwidth and protocol design. That limitation creates an opening. If an attacker can control those connections, they can influence what a node sees and believes.
An eclipse attack exploits this exact weakness. Instead of attacking the entire blockchain, it targets a single node or a small group. The attacker surrounds the victim with malicious peers, cutting it off from honest participants. From that point forward, the victim operates in a distorted version of the network.
This concept may sound abstract, but it has real consequences. A node that cannot see the true blockchain state can be tricked into accepting fake transactions or ignoring valid ones. The attack does not break the blockchain itself. It breaks the victim’s perception of it.
What Exactly Is an Eclipse Attack?
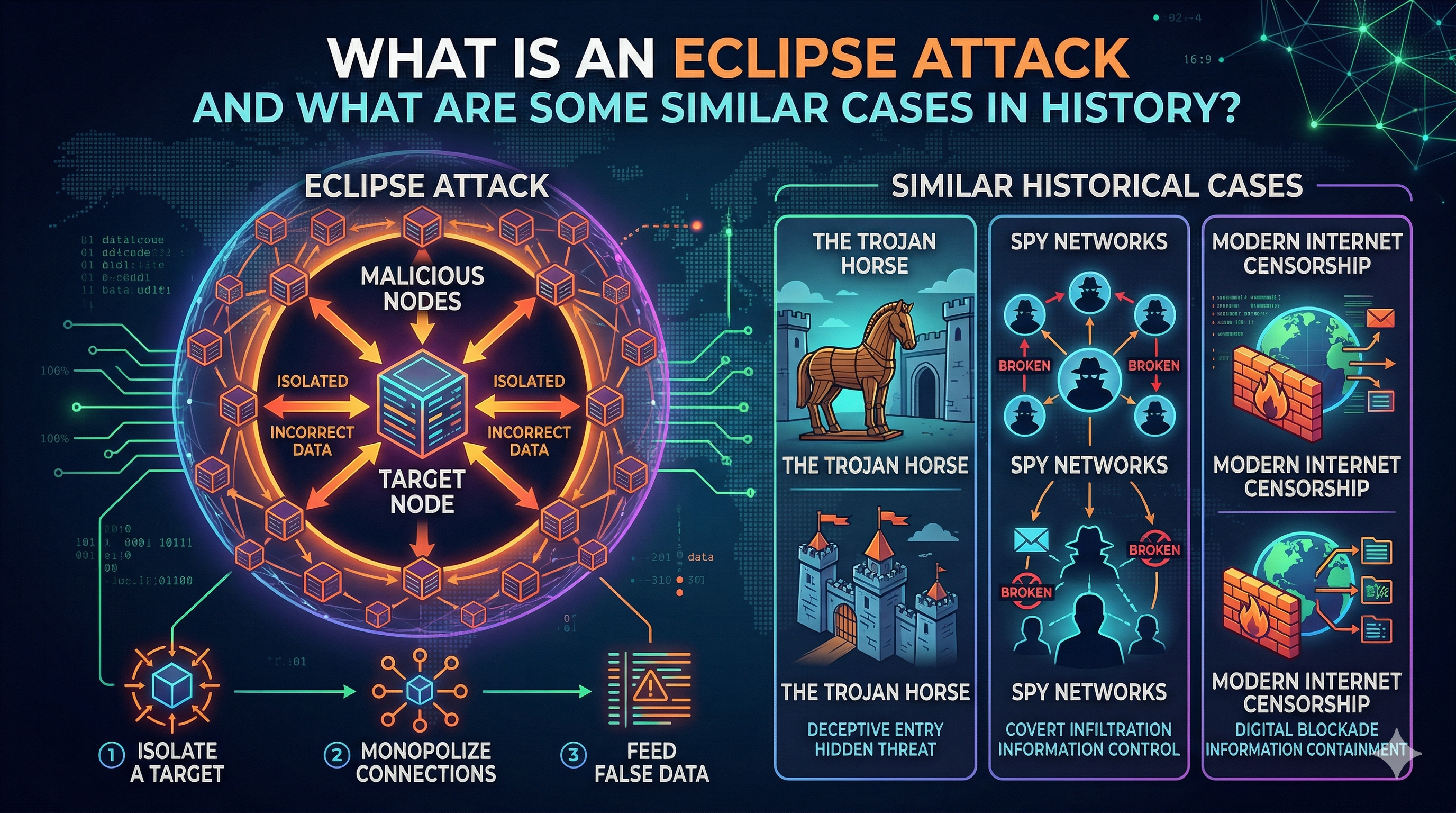
An eclipse attack is a network-level attack where a malicious actor isolates a node from the rest of the blockchain network and controls all its incoming and outgoing connections. Once isolated, the attacker feeds the node false or manipulated data, effectively rewriting its view of reality.
This isolation is achieved by overwhelming the target node with attacker-controlled peers. Since nodes can only maintain a limited number of connections, filling those slots with malicious nodes ensures that no legitimate information gets through. The victim becomes trapped in a controlled environment created by the attacker.
The consequences can be severe. The attacker can delay transactions, hide important updates, or trick the node into accepting invalid data. In some cases, this leads to double-spending, where the same cryptocurrency is used more than once without detection.
What makes eclipse attacks especially dangerous is their precision. They do not require massive computational power like a 51% attack. Instead, they rely on network manipulation and patience. This makes them more accessible to attackers with fewer resources.
The term “eclipse” is fitting. Just as the moon blocks sunlight during a solar eclipse, the attacker blocks the node’s access to the real network, leaving it in darkness.
How an Eclipse Attack Actually Works
The execution of an eclipse attack follows a calculated sequence. It begins with identifying a vulnerable node. Attackers often look for nodes with weak security configurations, outdated software, or limited peer diversity.
The next step involves creating or controlling multiple malicious nodes. These nodes are designed to appear legitimate, often using different IP addresses to avoid detection. This phase is closely related to a Sybil attack, where fake identities are created to influence a network. Once the attacker has enough malicious nodes, they attempt to connect to the target. This can happen when the node restarts or refreshes its connections. At that moment, the attacker floods it with malicious peers, occupying all available connection slots.
With the node fully surrounded, the isolation phase begins. The attacker now controls all data entering and leaving the node. They can delay messages, filter transactions, or inject false information. The final stage is exploitation. The attacker uses the controlled environment to achieve specific goals, such as double-spending or disrupting mining activity. The victim node continues operating normally, unaware that its entire view of the blockchain is false.
Why Eclipse Attacks Are So Dangerous
The danger of an eclipse attack lies in its subtlety. There is no dramatic crash or obvious failure. The network continues running, and the victim node behaves as if everything is normal.
This makes detection extremely difficult. Traditional security measures often focus on protecting the blockchain itself, not individual nodes. An eclipse attack targets the weakest link: the communication layer between nodes.
One major risk is double-spending. The attacker can trick the isolated node into accepting a transaction that does not exist on the real blockchain. By the time the node reconnects to the network, the funds may already be gone.
Another risk involves mining manipulation. A miner under an eclipse attack may waste computational power mining blocks that will never be accepted by the real network. This not only causes financial loss but also weakens network security. There is also a broader implication. If multiple nodes are targeted, the attacker can reduce the overall reliability of the network. This opens the door to larger attacks, including attempts to manipulate consensus mechanisms.
Real-World Case: Bitcoin Gold Double-Spend Attack
One of the most cited real-world incidents related to eclipse-style behavior occurred in 2018 on the Bitcoin Gold network. Attackers managed to exploit network vulnerabilities and perform a double-spending attack worth millions of dollars.
Reports indicate that attackers combined network manipulation with hash power control to isolate parts of the network. This allowed them to create a false version of transaction history and spend the same funds multiple times.
The attack resulted in losses estimated at around $18 million. It highlighted how smaller blockchain networks are more vulnerable to these types of attacks due to lower security and fewer nodes. This event demonstrated that eclipse attacks are not just theoretical. They can be used as part of larger attack strategies, amplifying their impact.
Ethereum Research and Eclipse Vulnerabilities
Ethereum has also been the subject of extensive research into eclipse attacks. Academic studies have shown that even large networks can be vulnerable under certain conditions. One study revealed that attackers could exploit peer discovery mechanisms to isolate nodes with relatively few resources. By manipulating how nodes find and connect to peers, attackers can increase their chances of controlling connections.
More recent research has demonstrated advanced techniques such as DNS poisoning and connection slot hijacking. These methods allow attackers to gradually take over a node’s connections without raising immediate suspicion. In controlled experiments, researchers successfully isolated Ethereum nodes and manipulated their view of the network. These findings were shared with developers, leading to improvements in security protocols.
Similar Attack: Sybil Attack
A closely related concept is the Sybil attack. In this scenario, an attacker creates multiple fake identities within a network to gain influence. While a Sybil attack targets the network as a whole, it often serves as a foundation for an eclipse attack. By flooding the network with fake nodes, the attacker increases the chances of surrounding a specific target.
The key difference lies in the objective. A Sybil attack aims to manipulate network behavior broadly, while an eclipse attack focuses on isolating a single node. Despite this difference, the two attacks often work together. The fake identities created in a Sybil attack can be used to execute an eclipse attack more effectively.
Similar Attack: 51% Attack
A 51% attack is another well-known threat in blockchain systems. It occurs when a single entity gains control of more than half of the network’s computational power. With this control, the attacker can manipulate transaction history, reverse payments, and prevent new transactions from being confirmed.
Although this attack operates at a different level, it shares a common theme with eclipse attacks: control over information. In a 51% attack, the attacker controls the majority of the network. In an eclipse attack, they control what a specific node sees. Both attacks undermine trust in the system. They demonstrate that decentralization alone is not enough. The structure of communication and consensus also matters.
Similar Attack: Routing and BGP Hijacking
Outside of blockchain, routing attacks such as BGP hijacking have similar effects. In these attacks, malicious actors manipulate internet routing paths to redirect traffic. By controlling how data flows across the internet, attackers can intercept, delay, or alter information. This is conceptually similar to an eclipse attack, where the victim’s view of the network is controlled.
Several incidents have shown how BGP hijacking can affect cryptocurrency networks. Attackers have redirected traffic from mining pools and exchanges, leading to financial losses. These cases show a broader issue. Blockchain security does not exist in isolation. It depends on the underlying internet infrastructure, which can also be attacked.
Why Smaller Networks Are More Vulnerable
Not all blockchains face the same level of risk. Smaller networks are generally more vulnerable to eclipse attacks due to limited resources and lower node diversity.
In a large network like Bitcoin, nodes connect to many peers, making it harder for an attacker to control all connections. Smaller networks often have fewer nodes and less redundancy, increasing the chances of successful isolation. Lower hash power also makes it easier to combine eclipse attacks with other methods, such as double-spending or consensus manipulation.
This vulnerability has been observed in several altcoin networks, where attackers exploit weaker security to carry out coordinated attacks.
How Developers Defend Against Eclipse Attacks
Developers have introduced several strategies to reduce the risk of eclipse attacks. One common approach is increasing peer diversity, ensuring that nodes connect to a wide range of participants.
Randomizing peer selection also helps prevent attackers from predicting and controlling connections. Some protocols limit the number of connections from the same IP range to reduce the impact of Sybil attacks.
Monitoring network behavior is another key defense. Sudden changes in connection patterns or data flow can indicate an ongoing attack. These measures do not eliminate the risk entirely, but they make attacks more difficult and costly to execute.
The Bigger Lesson: Control of Information Is Power
Eclipse attacks reveal a fundamental truth about blockchain systems. Security is not just about cryptography or consensus algorithms. It is also about communication. A node that cannot access accurate information cannot make correct decisions. Even in a decentralized system, isolation can lead to manipulation.
This insight extends beyond blockchain. In any networked system, controlling the flow of information can be as powerful as controlling the system itself.
The Future of Eclipse Attack Research
Research into eclipse attacks continues to grow massively. New techniques are being discovered, along with improved defenses. As blockchain adoption grows, so does the incentive for attackers to find new vulnerabilities. This creates an ongoing cycle of attack and defense.
Future developments will likely focus on improving peer discovery, strengthening network resilience, and integrating real-time detection mechanisms. The goal is not to eliminate attacks entirely, but to make them impractical and economically unviable.
FAQs
1. What is an eclipse attack in simple terms?
It is when a hacker isolates a node and controls all the information it receives, making it see a fake version of the network.
2. Is an eclipse attack common?
It is rare but dangerous. It requires planning and control over multiple nodes.
3. Can Bitcoin be affected by eclipse attacks?
Yes, but large networks like Bitcoin have stronger defenses, making attacks more difficult.
4. What is the main goal of an eclipse attack?
To manipulate transactions, delay information, or enable double-spending.
5. How is it different from a Sybil attack?
A Sybil attack creates fake identities across the network, while an eclipse attack isolates a specific node.
Disclaimer
This content is for informational purposes only and does not constitute investment advice. Cryptocurrency investments carry risk. Please do your own research (DYOR).

