Can Decentralized Networks Like Bitcoin Reduce Single Points of Failure in National Cybersecurity Infrastructure?
2026/04/28 08:48:02
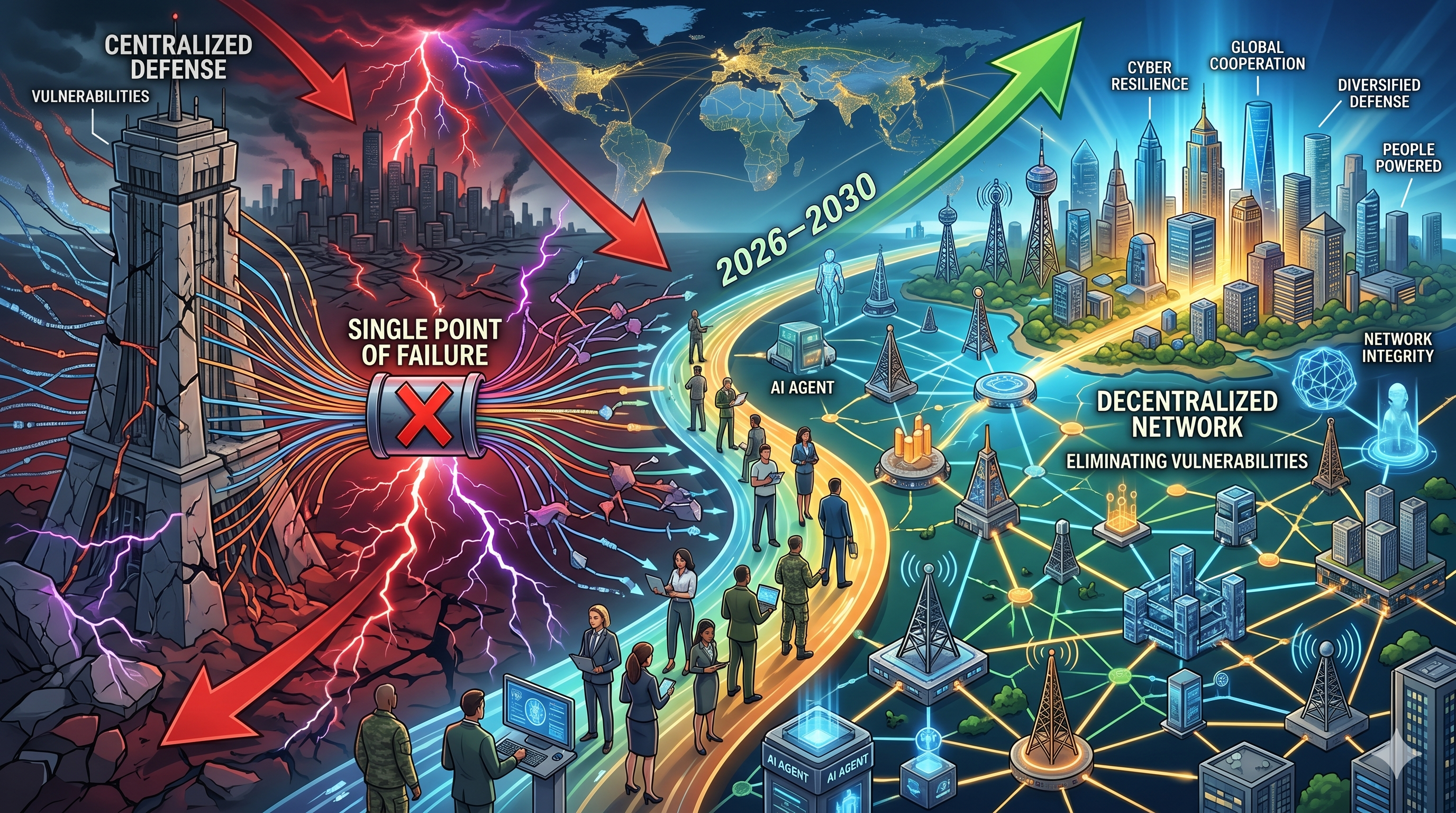
In 2025, a single Amazon Web Services outage cascaded across critical sectors — power grids, financial systems, transport networks — in a real-world demonstration of what cybersecurity experts call a "single point of failure." Following that AWS outage, several governments sounded the alarm over intrusions targeting critical infrastructure, ranging from cyber-espionage campaigns to disruptive attacks — with single points of failure now ranked among the leading threats to national security heading into 2026.
The answer to whether decentralized networks like Bitcoin can fix this problem is: yes, in meaningful and demonstrable ways — but with important caveats. Bitcoin's distributed architecture, proof-of-work consensus, and zero-trust design eliminate the central choke points that make traditional systems so vulnerable. And in April 2026, the U.S. military publicly confirmed it agrees.
Key Takeaways
-
National cybersecurity infrastructure built on centralized systems creates dangerous single points of failure — one successful attack can cascade across entire networks and sectors.
-
Bitcoin's peer-to-peer architecture, cryptographic immutability, and proof-of-work consensus are structurally designed to eliminate these choke points.
-
On April 21–23, 2026, Admiral Samuel Paparo of INDOPACOM confirmed the U.S. military is running a live Bitcoin node and conducting operational cybersecurity tests using the Bitcoin protocol.
-
Research from Cambridge spanning 2014–2025 shows Bitcoin's random-failure threshold is extremely high — the vast majority of global internet infrastructure would need to fail before the network disconnects.
-
The critical vulnerability is not Bitcoin's base layer but the centralized infrastructure wrapped around it: cloud-hosted nodes, third-party APIs, and DeFi bridges.
-
DePIN (Decentralized Physical Infrastructure Networks) and BitSov-style frameworks are emerging as architectural blueprints for applying Bitcoin's decentralization model to broader national infrastructure.
The Single Point of Failure Problem in National Cybersecurity
Centralized Systems Are the Achilles' Heel of Modern Infrastructure
Single points of failure will likely prompt many countries to seek to decentralize their cloud providers more aggressively and rely on a more diverse set of vendors to reduce concerns about dependence on one major provider. Critical infrastructure providers — including in the power, transportation, and financial sectors — face numerous infiltration attempts by state actors seeking to establish footholds in computer systems for exploitation during a potential cyber conflict.
This is the core paradox of modern digital infrastructure. The same centralization that makes systems efficient — one cloud provider, one authentication service, one software library — makes them catastrophically vulnerable. Attack one node, disable everything that depends on it.
Youssef El Maddarsi, Co-Founder and Chief Business Officer of Naoris Protocol, explained the logic plainly: "Today in systems you have what we call a single point of failure. That means if I'm an attacker, I attack one device and take over everything."
The Scale of the Problem in 2026
The WEF 2026 Cybersecurity Report shows 61% of organizations identify cloud technology as a major cybersecurity factor, and Web3 projects still run most "decentralized" applications on AWS, Google Cloud, or Azure. A compromise anywhere in that chain cascades everywhere.
The irony is pointed: an industry built on the philosophy of decentralization is running its infrastructure on hyper-centralized cloud platforms. When those platforms fail — or are successfully attacked — the consequences are system-wide.
Two-thirds of companies surveyed reshuffled their cybersecurity strategies because of geopolitical volatility, with two in three firms specifically accounting for state-sponsored cyberattacks.
Why Bitcoin's Architecture Addresses This Problem Directly
Distributed by Design: No Single Node Controls the Ledger
By distributing information across a network of computers, blockchain removes single points of failure, and it becomes extremely hard for hackers to tamper with or destroy the information. It can be said that there is no point of failure or vulnerability in the base layer of blockchain technology.
Bitcoin's network consists of thousands of independent nodes, each holding a complete copy of the blockchain and independently validating transactions. There is no CEO, no headquarters, no master database. Disabling one node — or even thousands of nodes — does not impair the rest. The network heals and continues.
This decentralized architecture eliminates single points of failure, making it significantly more challenging for attackers to disrupt or compromise the entire network. Blockchain employs cryptographic hash functions to secure transactions. Each block contains a hash of the previous block, creating a cryptographic linkage that ensures immutability and provides a permanent, auditable record that is highly resistant to tampering.
Proven Resilience: 11 Years of Stress Testing
The resilience of Bitcoin's network is not theoretical. It has been measured rigorously. A longitudinal Cambridge Centre for Alternative Finance study using 11 years of peer-to-peer network data (2014–2025) and 68 verified cable fault events found that Bitcoin's critical failure threshold for random failures requires the vast majority of inter-country submarine cables to fail before significant node disconnection occurs. Targeted attacks are an order of magnitude more effective, but even then, the threshold remains substantially higher than conventional centralized systems.
This means Bitcoin's network has effectively been stress-tested against real-world infrastructure disasters — including cable failures, ISP outages, and coordinated routing attacks — continuously for over a decade, and has never gone offline.
Zero-Trust Architecture and Cost-Imposition Logic
Proof-of-work requires real computational resources to validate transactions. INDOPACOM sees that property as applicable to raising real-world costs for adversaries in cyber operations. Admiral Paparo framed it directly: proof-of-work "imposes more cost than just the algorithmic securing of networks."
This is a fundamental shift from conventional cybersecurity thinking. Traditional defenses are algorithmic — they cost almost nothing to bypass if the attacker finds the right exploit. Proof-of-work introduces physical-world cost into digital security. Attacking a PoW-secured system requires real energy, real hardware, and real money. The economics of attack change entirely.
The U.S. Military's Validation: INDOPACOM Runs a Live Node
The Congressional Testimony That Changed the Conversation
Admiral Samuel Paparo, commander of U.S. Indo-Pacific Command, disclosed to the House Armed Services Committee on April 23, 2026 that the U.S. military is operating a live node on the Bitcoin network and conducting operational tests using the protocol to explore its potential applications for securing military infrastructure. This marks the first public confirmation by a sitting U.S. combatant commander that the military is directly participating in the Bitcoin peer-to-peer network.
The military framing was explicit and technical, not financial. Paparo stated: "Our interest in Bitcoin is as a tool of cryptography, a blockchain, and reusable proof of work as an additional tool to secure networks and project power. I think this protocol is here to stay. I think the computer science of it has direct implications for the projection of power — not financial, but from a computer science standpoint."
From Academic Theory to Operational Doctrine
Conceptually, Paparo's testimony picks up a thesis that Major Jason Lowery developed in his 2023 book "Softwar" — which frames proof-of-work as a form of military power projection in cyberspace, without physical force. When a four-star admiral argues along these lines before the Senate, the debate moves from academic circles into operational doctrine.
Jason Lowery, a member of the U.S. Space Force, said that proof-of-work blockchains may be used to protect "all forms of data, messages, or command signals," not just money. The U.S. military running a live Bitcoin node in April 2026 is the operational manifestation of that thesis.
The Critical Nuance: Where Decentralization Still Falls Short
The Centralized Wrapper Problem
Bitcoin's base layer is resilient. But the infrastructure built around it often is not. Think about Web3 and crypto's infrastructure dependencies: cloud providers hosting nodes, third-party wallet libraries, blockchain explorers, custody solutions. A compromise anywhere in that chain cascades everywhere. In 2025, single vulnerabilities in widely-used libraries affected thousands of projects downstream.
This is the "centralized wrapper problem" — a decentralized protocol made vulnerable by the centralized services layered on top of it. If your Bitcoin node runs on AWS, and AWS goes down, your node goes with it. The protocol survives, but your participation in it does not.
Smart Contracts and Bridge Vulnerabilities
While the number of security incidents fell by about 50% compared with 2024, the damage from those incidents grew far worse — losses climbed 55% to over $3.4 billion. Cross-chain bridge exploits alone led to more than $1.5 billion in theft by mid-2025. The blockchain space has a glaring vulnerability in outdated, siloed security audits.
The recent April 2026 KelpDAO exploit — in which attackers drained $292 million through a single-verifier bridge misconfiguration — illustrates exactly this dynamic. The Bitcoin base layer was never touched. The vulnerability was in the centralized infrastructure layer connecting it to other systems.
Quantum Computing: The Coming Threat
About 37% of respondents think quantum computing will impact cybersecurity this year, but the WEF projects it becoming a real threat by 2030. For crypto, that timeline is deeply concerning — most blockchain cryptography breaks under quantum attacks, especially the public key cryptography securing wallet addresses.
Post-quantum cryptography migration is something the White House strategy has emphasized massively, covering everything from infrastructure to network to identities. Bitcoin's long-term role in national cybersecurity infrastructure depends in part on the speed of quantum-resistant cryptography adoption.
Emerging Frameworks: Building National Infrastructure on Bitcoin's Architecture
DePIN: Decentralizing Physical Infrastructure with Crypto-Economic Design
The emergence of Decentralized Physical Infrastructure Networks (DePIN) signals a significant shift driven by the need to improve data sovereignty, reduce trust centralization, and increase resilience against single points of failure. DePINs merge the Internet of Things with blockchain technology and crypto-economic design to create a more distributed and resilient approach to digital infrastructure.
DePIN networks apply Bitcoin's core insight — that economic incentives can coordinate distributed, trustless infrastructure — to physical systems like wireless networks, sensor grids, and data storage. The model distributes both control and risk across thousands of independent participants, making any single-node attack strategically futile.
BitSov: A Bitcoin-Native Architecture for Sovereign Infrastructure
BitSov, accepted at IEEE's BlockArch 2026 workshop, presents an architectural framework for sovereign internet infrastructure that composes existing decentralized technologies — Bitcoin, the Lightning Network, decentralized storage, federated messaging, and mesh connectivity — into a unified, eight-layer protocol stack anchored to Bitcoin's base layer. Today's internet concentrates identity, payments, communication, and content hosting under a small number of corporate intermediaries, creating single points of failure, enabling censorship, and extracting economic rent from participants.
The BitSov framework represents the most comprehensive attempt yet to use Bitcoin's architectural principles as a blueprint for censorship-resistant, failure-tolerant national infrastructure. Its acceptance at a leading IEEE workshop signals the idea is maturing from concept to engineering.
How to Position Yourself at the Intersection of Bitcoin and Cybersecurity Infrastructure
The U.S. military's validation of Bitcoin as a cybersecurity tool is one of the most significant institutional signals for Bitcoin's long-term value proposition in years. It fundamentally repositions BTC from a "speculative asset" narrative into something more durable: mission-critical infrastructure. If you want to trade Bitcoin and the ecosystem of tokens building on its security model — from DePIN infrastructure tokens to proof-of-work derivatives — KuCoin provides deep, liquid markets with professional-grade tools.
Bitcoin surpassed $77,000 following Paparo's testimony, with Strategy making a $2.5 billion BTC purchase — the third-largest weekly buy on record — tightening supply at a time when U.S. spot Bitcoin ETFs were already seeing inflows for five consecutive days. For traders and long-term holders alike, this institutional confluence of military validation, sovereign reserve accumulation, and ETF inflows creates a compelling market structure. KuCoin's spot markets, grid trading bots, and futures desk give you the tools to capitalize on these macro tailwinds — whether you're accumulating Bitcoin during consolidation or hedging exposure around geopolitical developments.
Further Read:
Conclusion
The answer to whether decentralized networks like Bitcoin can reduce single points of failure in national cybersecurity infrastructure is an emphatic yes — with an essential caveat. Bitcoin's base layer, tested across 11 years and 68 real-world cable fault events, demonstrates extraordinary resilience to both random failures and targeted attacks. Its zero-trust architecture, cryptographic immutability, and proof-of-work cost-imposition logic address the structural vulnerabilities of centralized systems in ways that no conventional cybersecurity approach can replicate.
The U.S. military's live Bitcoin node — confirmed by Admiral Paparo before Congress in April 2026 — validates this thesis at the highest institutional level. INDOPACOM is not investing in Bitcoin for profit. It is testing whether Bitcoin's protocol architecture can harden military networks against state-sponsored adversaries in the most contested theater on earth.
But the work is not finished. Centralized infrastructure layers, bridge vulnerabilities, cloud dependencies, and the looming quantum computing threat all create real attack surfaces that Bitcoin's base layer alone cannot solve. The future of decentralized national cybersecurity infrastructure lies in applying Bitcoin's architectural principles across every layer of the stack — from physical nodes to identity systems to communications. That work is underway. And the race to build it is geopolitical.
FAQs
Is running a Bitcoin node the same as investing in Bitcoin?
No. Running a Bitcoin node requires no investment, no specialized mining hardware, and earns no financial reward. It means storing a complete copy of the blockchain and validating transactions independently. The U.S. military is not mining Bitcoin — it is using the node to monitor the network and run operational tests on securing and protecting networks using the Bitcoin protocol.
Could the U.S. government use its Bitcoin node to censor or control transactions?
No. The blockchain is supported by tens of thousands of nodes distributed worldwide. That decentralized structure means no single operator controls transaction validation. One government-run node would not threaten the network's independence. Bitcoin's consensus rules are enforced collectively — any node that attempts to violate them is simply rejected by the rest of the network.
What is DePIN and how does it relate to Bitcoin's cybersecurity model?
DePIN (Decentralized Physical Infrastructure Networks) merges the Internet of Things with blockchain technology and crypto-economic design to create a more distributed and resilient approach to digital infrastructure, driven by the need to improve data sovereignty, reduce trust centralization, and increase resilience against single points of failure. DePIN applies Bitcoin's core insight — that distributed, incentivized coordination can replace centralized control — to physical infrastructure like wireless networks and data storage.
What is the "Softwar" thesis and why is it relevant to national cybersecurity?
Major Jason Lowery's "Softwar" thesis frames proof-of-work as a form of military power projection in cyberspace, without physical force. The argument is that just as nuclear deterrence imposes physical costs on would-be aggressors, proof-of-work imposes real computational and energy costs on cyber attackers — fundamentally changing the economics of offensive cyber operations. Admiral Paparo's April 2026 congressional testimony directly echoes this framework.
Disclaimer: This article is for informational purposes only and does not constitute financial or investment advice. Cryptocurrency investments carry significant risk. Always conduct your own research before trading.

