What is Sandwich Attack : How It Works, Historical Examples, Risks, and Prevention
2026/04/06 09:30:50

What looks like ordinary slippage on a decentralized exchange is not always ordinary. In many cases, a trader submits a swap, the transaction becomes visible before confirmation, and automated bots react within seconds to exploit that information. The result is a worse execution price for the user and a quick profit for the attacker. This tactic is known as a sandwich attack, and it has become one of the most discussed forms of MEV in decentralized finance.
The broader crypto market is built on transparency, speed, and open access. Those qualities are part of what makes DeFi attractive. At the same time, that same openness allows sophisticated bots to monitor pending transactions, estimate price impact, and insert their own trades around user activity. This creates a market-structure problem that every serious crypto user should understand.
By the end of this article, you will understand what a sandwich attack is, how sandwich attacks work in crypto, why they are common on AMM-based decentralized exchanges, which traders are most vulnerable, and what practical steps can reduce exposure. You will also see how this tactic fits into the larger discussion around DeFi trading, transaction ordering, onchain market fairness, and MEV protection.
Hook
What if your crypto trade was not just affected by volatility, but deliberately targeted before it even reached the blockchain?
Overview
This article explains the meaning of a sandwich attack in crypto, breaks down how it works, explores its impact on decentralized trading, reviews historical examples from the rise of DeFi, and outlines the main risks and precautions traders should understand.
Thesis
The purpose of this article is to explain sandwich attacks in a clear, practical way so readers can understand how they affect crypto trading, why they matter in modern DeFi markets, and how traders can reduce the chances of being exploited by this form of market manipulation.
What Is a Sandwich Attack?
A sandwich attack is a DeFi trading exploit that usually happens on decentralized exchanges using automated market makers (AMMs). In simple terms, an attacker spots a victim’s pending transaction in the mempool, places one trade before it and another after it, and profits from the price slippage caused by the victim’s order.
The structure is simple:
-
the attacker’s first trade comes first
-
the victim’s trade is in the middle
-
the attacker’s second trade comes last
The purpose is to profit from the victim’s price impact.
For example, imagine a trader wants to buy a token on a decentralized exchange. If that order is large enough, it will push the token’s price up inside the liquidity pool. A sandwich bot can detect the pending transaction, buy the token first, let the victim’s trade drive the price higher, and then sell immediately afterward at a profit.
The victim still completes the trade, but at a worse price than they would have received if the attacker had not intervened.
That is what makes sandwich attacks so important in crypto. They do not usually involve stealing funds directly or exploiting a software bug. Instead, they exploit the trading environment itself. The attacker relies on three conditions:
-
public visibility of pending transactions
-
predictable price movement in AMM-based pools
-
the victim’s willingness to accept some slippage
Because of that, a sandwich attack is better understood as a transaction-ordering exploit than a traditional hack.
How a Sandwich Attack Works
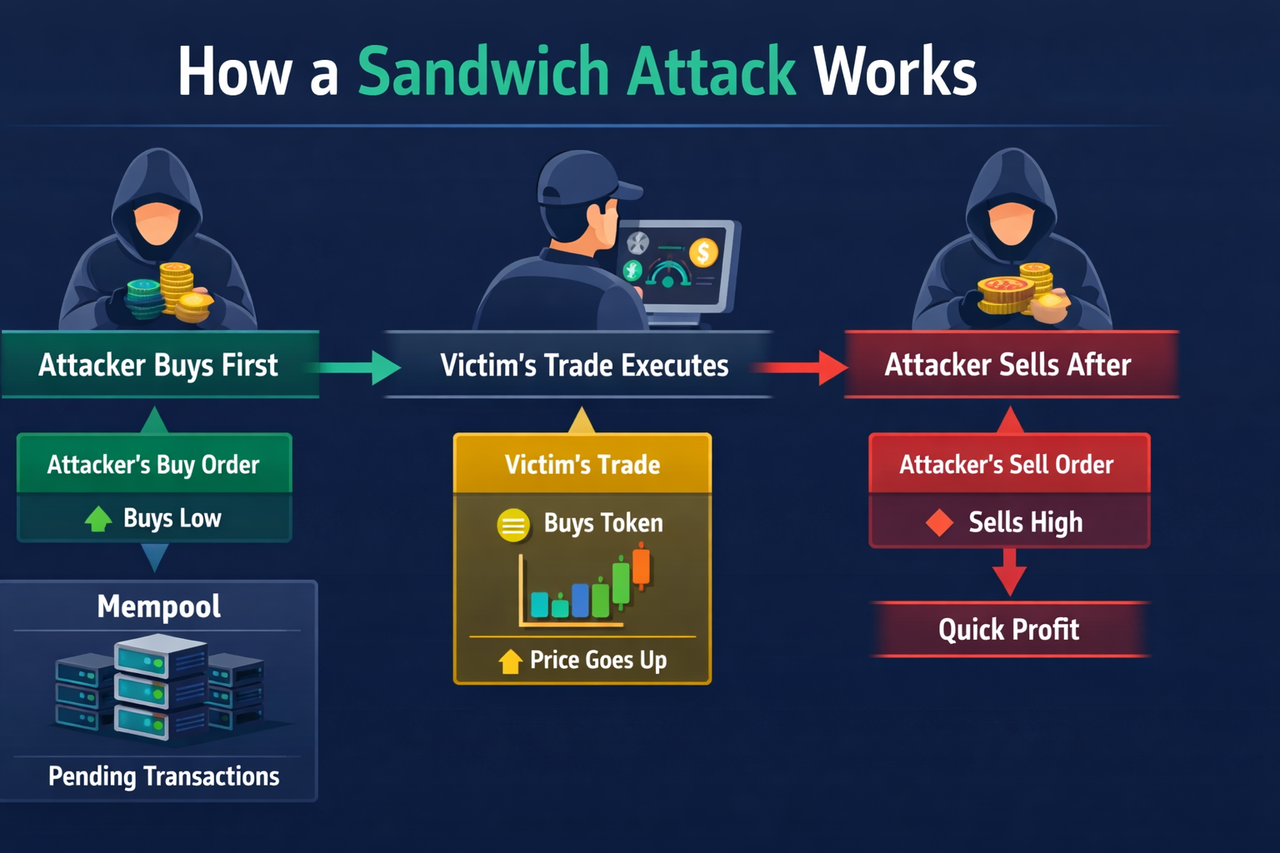
To understand sandwich attacks clearly, it helps to look at the process step by step.
-
A trader submits a swap
A user places a trade on a decentralized exchange. For example, they might swap ETH for another token on a DeFi platform such as a Uniswap-style AMM.
Before the trade is finalized, the transaction often sits in a public waiting area known as the mempool. This is where pending transactions are visible before they are added to the blockchain.
-
A bot detects the pending transaction
Specialized bots constantly scan the mempool. They look for trades that could be profitable to exploit, especially:
-
large swaps
-
trades involving low-liquidity tokens
-
transactions with enough slippage tolerance to leave room for price movement
If the bot estimates that the victim’s trade will move the market enough to create profit, it acts immediately.
-
The attacker places the first trade
The attacker sends a transaction that will execute before the victim’s order. This is often done by paying a higher gas fee or using another method to gain priority.
If the victim is buying a token, the attacker buys first. That preemptive purchase pushes the price up before the victim’s transaction is processed.
-
The victim’s trade executes at a worse price
Now the victim’s trade goes through, but the price has already moved against them. The victim receives fewer tokens than expected or pays more than expected.
The transaction still succeeds because the price movement remains within the user’s slippage tolerance.
-
The attacker exits after the victim
After the victim’s trade pushes the price further, the attacker places the second trade, usually selling what was bought in the first step. This allows the attacker to lock in a quick gain.
The result looks like this:
-
the attacker buys low
-
the victim’s trade pushes the price higher
-
the attacker sells high
All of this can happen in seconds or milliseconds.
A Simple Example of a Sandwich Attack
Suppose a user wants to buy Token A with ETH on a decentralized exchange. The liquidity pool for Token A is not very deep, so a larger order will move the price noticeably.
A sandwich bot sees the user’s pending swap in the mempool. It quickly sends its own buy order first. That purchase raises the price of Token A. Then the victim’s original buy order goes through at the new, higher price. Finally, the bot sells the tokens it bought moments earlier.
The attacker profits from the difference between the lower purchase price and the higher sale price.
The victim may only notice that they received fewer tokens than expected. To them, it may look like ordinary slippage. But in reality, the price movement was deliberately created to exploit their transaction.
This is one reason sandwich attacks are difficult for casual traders to spot. The swap still completes. The interface may not show anything obviously suspicious. The loss is often hidden inside the final execution price.
Why Sandwich Attacks Happen in DeFi
Sandwich attacks became common because DeFi created the exact conditions in which they can thrive.
Public transaction visibility
On many blockchains, transactions are visible before they are confirmed. This transparency helps the network function, but it also gives bots time to inspect pending transactions and plan around them.
In traditional finance, not every pending order is openly visible to every competitor in the same way. In DeFi, public visibility became both a feature and a weakness.
AMM-based pricing
Most decentralized exchanges do not use a traditional order book. Instead, they rely on automated market makers that calculate token prices based on the balance of assets in a liquidity pool.
When someone places a large buy order, the price goes up. When someone places a large sell order, the price goes down. This movement is not random. It follows the pool’s formula, which makes sandwich attacks possible.
Slippage tolerance
Users often allow a certain level of slippage so their transaction does not fail if the price changes slightly before confirmation. This is practical, but it also creates room for attackers.
If the attacker can move the price against the victim while still staying within the allowed slippage range, the trade will still execute.
Speed and automation
Most sandwich attacks are carried out by bots rather than humans. Bots can monitor pending transactions, simulate potential profit, and submit priority transactions almost instantly.
This makes sandwiching highly scalable. Once the strategy became known, it could be automated across large numbers of trades.
Why Sandwich Attacks Matter
Sandwich attacks may sound technical, but they have real effects on everyday crypto traders. They matter because users end up with worse prices, especially on large or low-liquidity trades. Over time, this can reduce trust in DeFi and make decentralized trading feel unfair.
They also highlight a bigger issue in crypto markets: transparency does not always lead to fairness. When pending transactions are visible, faster actors can use that information to profit at the expense of regular users.
Sandwich Attacks and MEV
Sandwich attacks are one of the clearest examples of MEV, or maximal extractable value. MEV refers to profit made by changing the order of transactions in a block.
In a sandwich attack, the attacker earns money by placing one trade before the victim and another after it. That makes transaction ordering the main source of profit.
Because the idea is easy to understand, sandwich attacks became one of the main examples used to explain how MEV works in DeFi.
Historical Background: The Rise of Sandwich Attacks
Sandwich attacks did not become widely known because of one isolated event. They emerged through repeated patterns during the rapid expansion of decentralized finance.
Early DeFi growth
As DeFi gained momentum in the early 2020s, decentralized exchanges such as Uniswap made token swaps simple and accessible. Anyone could trade directly from a wallet, and liquidity pools allowed markets to function without traditional market makers.
This innovation helped fuel explosive growth in onchain trading. But it also introduced a weakness. Pending trades were visible, and AMM prices responded predictably to large swaps. That made it possible for bots to spot and exploit profitable opportunities.
Growing recognition from traders and researchers
As the ecosystem matured, traders began noticing unusually poor execution on larger swaps, especially in lower-liquidity pools. Researchers and market observers started analyzing transaction patterns and realized that many of these cases were not random slippage. They were structured attacks.
Once this pattern became widely recognized, sandwiching moved from being a technical detail to a major topic in DeFi education and research.
From opportunistic tactic to industrialized strategy
In the beginning, sandwich attacks may have seemed like isolated opportunistic behavior. But as the profit potential became clearer, specialized infrastructure emerged. Bots became more sophisticated. Searchers built systems to scan the mempool, simulate trades, calculate profitability, and race for priority.
At that point, sandwich attacks were no longer a side effect. They had become an industry.
Historical Examples of Sandwich Attacks
Because sandwich attacks often happen at the transaction level, they are not always represented by a single famous headline. The clearest way to understand their history is through major phases and recurring examples.
-
Ethereum and Uniswap in the early DeFi era
The first major environment where sandwich attacks became widely visible was Ethereum’s DeFi ecosystem, especially around AMM-based exchanges such as Uniswap.
As Ethereum-based trading volume increased, larger swaps frequently attracted bots that could monitor the mempool and act within seconds. Researchers and traders observed a repeating pattern:
-
a large pending swap appeared
-
a bot entered first
-
the victim’s trade executed at a worse rate
-
the bot exited immediately after
This phase is historically important because it established the classic structure used to explain sandwich attacks today. Ethereum’s public mempool, combined with the popularity of AMM-based trading, made it the clearest early case study.
For many users, this was their first exposure to the idea that bad execution in DeFi might not simply be random market movement.
-
The rise of professional MEV searchers
As DeFi matured, sandwich attacks became much more sophisticated. What began as an opportunistic strategy turned into a specialized activity carried out by MEV searchers.
These searchers built tools specifically for identifying profitable transaction-ordering opportunities. Their systems monitored the mempool continuously, ran simulations to estimate whether a pending trade could be sandwiched profitably, and submitted transactions with carefully optimized fees.
This phase matters historically because it marked the transition from isolated bot activity to a competitive, professionalized market. Sandwich attacks were no longer random occurrences. They became a core strategy in the growing MEV ecosystem.
It also changed the scale of the issue. Once highly optimized searchers entered the space, sandwiching became more systematic and harder for ordinary users to avoid.
-
Gas wars between competing bots
Another important historical phase came when multiple bots started targeting the same pending transaction. If one swap looked especially profitable, several searchers might try to sandwich it simultaneously.
This led to gas wars, where bots paid increasingly high fees in order to gain transaction priority. These contests showed just how valuable sandwich opportunities could be.
Historically, this was a turning point because it demonstrated that sandwich attacks were not a minor inconvenience. They were economically significant enough to spark intense competition between professional actors.
It also revealed a second layer of inefficiency: not only was the victim being exploited, but competition between bots could also raise network congestion and transaction costs more broadly.
-
Expansion beyond Ethereum
Although Ethereum became the most recognized environment for sandwich attacks, the tactic did not remain limited to one blockchain.
As other chains adopted decentralized exchanges and AMM-based trading, similar vulnerabilities appeared elsewhere. Any ecosystem with these characteristics could become a target:
-
visible pending transactions
-
active token trading
-
liquidity pools that react predictably to order size
-
users willing to accept slippage
This expansion showed that sandwich attacks were not specific to one brand or one protocol. They were a structural feature of certain types of onchain market design.
That historical shift is important because it moved the conversation away from blaming a single chain and toward recognizing a broader design problem in DeFi.
-
Meme coin and low-liquidity token markets
Another highly visible example of sandwich attacks emerged in meme coin markets and newly launched low-liquidity tokens.
These environments were especially attractive to attackers because they often combined:
-
shallow liquidity
-
high volatility
-
fast retail demand
-
wide slippage settings
-
traders rushing to enter positions quickly
In these conditions, even relatively small preemptive trades could shift prices meaningfully. That made it easier for bots to exploit users.
This phase matters historically because it brought sandwich attacks into the everyday experience of retail traders. The issue was no longer confined to researchers or large DeFi participants. Average users could feel it directly when they got a far worse price than expected during a hot token launch.
Risks and Precautions of Sandwich Attacks in DeFi
-
Public mempool exposure: Pending transactions are often visible before confirmation, giving bots time to detect and target trades.
-
High slippage settings: Wide slippage tolerance gives attackers more room to move the price against users while still allowing the transaction to go through.
-
Low-liquidity pools: Thin liquidity makes prices easier to manipulate, which increases the risk of sandwich attacks.
-
Hidden losses: Many traders only notice that the swap succeeded, not that they received a worse execution price.
-
Incomplete protection: MEV protection tools can help reduce exposure, but they do not remove all sandwich attack risk.
-
Precautions for traders: Users can lower risk by keeping slippage low, avoiding illiquid pools, splitting large swaps, and using protected routing tools where available.
Conclusion
A sandwich attack in crypto is one of the clearest examples of how transaction visibility and execution mechanics can shape real outcomes in DeFi. The attacker places one trade before a victim’s pending transaction and one after it, capturing profit while the victim gets a worse price. It is simple in concept, highly effective in practice, and deeply tied to the rise of MEV in decentralized markets.
This article has covered the meaning of sandwich attacks, how they work, why they affect crypto trading and market security, the historical patterns that made them such a major topic in DeFi, and the practical precautions users should understand. The key point is straightforward: a successful trade is not always a fair trade. In crypto, execution quality matters.
For traders, educators, and anyone trying to understand decentralized exchanges more deeply, sandwich attacks remain one of the most important concepts in modern DeFi.
Call to Action
Want to understand DeFi trading risks more clearly? Visit KuCoin Learn for more on sandwich attacks, slippage, and other DeFi basics.
Frequently Asked Questions About Sandwich Attacks
What is a sandwich attack in crypto?
A sandwich attack is a DeFi trading exploit where an attacker places one trade before and one trade after a victim’s pending transaction to profit from the price movement caused by that victim’s trade.
Why is it called a sandwich attack?
It is called a sandwich attack because the victim’s transaction is placed between two attacker transactions, like the filling between two slices of bread.
Is a sandwich attack the same as front-running?
Not exactly. Front-running usually means placing a transaction ahead of another pending transaction. A sandwich attack is a more specific version that also includes a second trade after the victim.
Where do sandwich attacks usually happen?
They most often happen on decentralized exchanges that use automated market makers, especially when trades are visible in the public mempool and the token pair has limited liquidity.
Who is most vulnerable to sandwich attacks?
Large traders, users trading low-liquidity tokens, meme coin buyers, and people using high slippage settings are usually the most exposed.
Can sandwich attacks happen outside Ethereum?
Yes. They can occur on any blockchain environment where pending transactions are visible and AMM-style pricing makes transaction ordering profitable.
How can users reduce the risk of a sandwich attack?
Users can reduce risk by tightening slippage, avoiding illiquid pools, splitting large swaps, using protected routing tools where available, and paying closer attention to execution quality.
Are sandwich attacks illegal?
The legal treatment depends on the jurisdiction and the facts of the case. In most crypto discussions, sandwich attacks are treated as a market-structure and MEV issue rather than a simple software exploit.
Disclaimer: The information provided on this page may originate from third-party sources and does not necessarily represent the views or opinions of KuCoin. This content is intended solely for general informational purposes and should not be considered as financial, investment, or professional advice. KuCoin does not guarantee the accuracy, completeness, or reliability of the information, and is not responsible for any errors, omissions, or outcomes resulting from its use. Investing in digital assets carries inherent risks. Please carefully evaluate your risk tolerance and financial situation before making any investment decisions. For further details, please consult our Terms of Use and Risk Disclosure