Double Spending in Cryptocurrency: What It Is, How It Works, and Historical Parallels That Changed Finance
Introduction: The Problem That Nearly Killed Digital Money Before It Began
Imagine handing a merchant a $100 bill for a new pair of shoes and then walking into the store next door to spend the same bill again. In the physical world, this is not how money is meant to work. Physical cash cannot be reused in multiple transactions at the same time because possession transfers when it is exchanged.
While counterfeiting exists, it is a separate issue that involves creating fake currency rather than reusing the same valid bill. In the digital world, however, money is represented as data, and data can be copied. This creates a fundamental question at the heart of digital finance: what prevents someone from duplicating their coins and spending them twice?
This problem, known as double spending, has long been one of the most important challenges in building a reliable digital currency. Before Bitcoin introduced a decentralized solution in 2009, preventing double spending without relying on a central authority was widely viewed as impractical. Without an effective safeguard, a digital currency system would struggle to maintain trust, since the same unit of value could be reused across multiple transactions.
This article explains what double spending is, how blockchain technology prevents it, the different types of double spending attacks, examples of cryptocurrencies that have faced such issues, and the historical context behind this long-standing financial problem. Whether you are new to crypto or looking to deepen your understanding of blockchain security, this guide provides a clear and structured foundation.
What Is Double Spending?
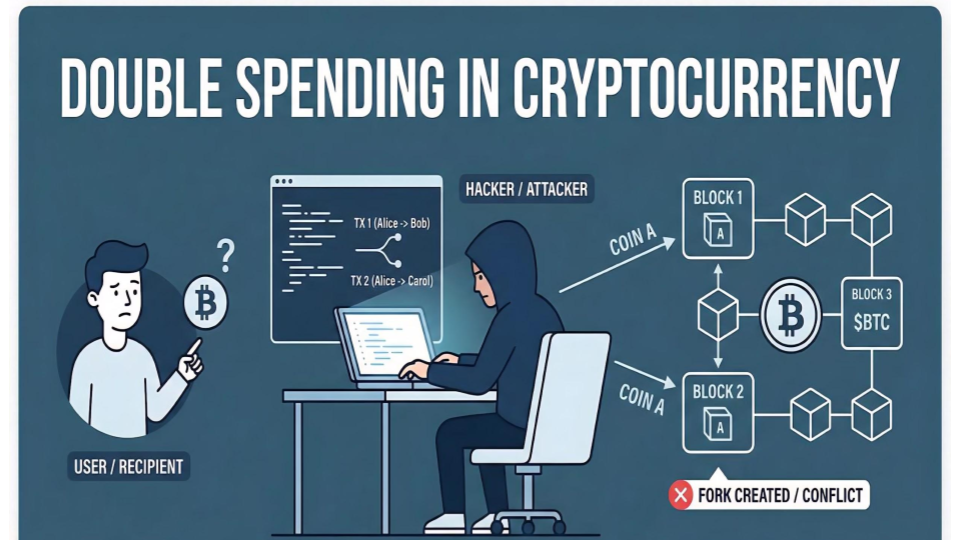
Double spending is the unauthorized act of spending the same unit of digital currency more than once. In traditional financial systems, this is prevented by centralized record keeping. In decentralized systems like blockchain, preventing the same unit from being reused across multiple transactions is a core design challenge.
In simple terms, double spending occurs when a single digital asset is duplicated or reused in a way that allows it to be transferred to more than one recipient. This can lead to an increase in effective supply, reduce trust in the system, and undermine the integrity of transactions.
Why Double Spending Matters
Double spending is more than a technical limitation. It directly impacts the reliability, integrity, and usability of any monetary system built on digital assets. At its core, money depends on trust, and double spending threatens that trust by introducing uncertainty over whether a transaction is final and valid. This challenge was explicitly identified by Satoshi Nakamoto in the Bitcoin whitepaper as a fundamental problem that needed to be solved for decentralized digital currency to work.
When a system cannot guarantee that a digital asset will not be reused, several consequences emerge. Transactions may lose finality, meaning recipients cannot be fully confident that the funds they receive are permanently theirs. This uncertainty can delay acceptance, especially in commercial environments where immediate settlement is important.
Over time, this lack of certainty can also affect the perceived value of the currency. If participants believe that the supply of a digital asset can be manipulated or duplicated, confidence in its scarcity weakens. Scarcity is a key property that underpins value in both traditional and digital monetary systems.
In practical terms, merchants and users may become reluctant to accept a currency that does not reliably prevent double spending. This hesitation can limit adoption, reduce transaction volume, and weaken the overall network effect that many digital currencies depend on.
For these reasons, preventing double spending is not just a technical requirement but a foundational condition for maintaining confidence, stability, and widespread usability in any digital currency system.
Double Spending in Traditional Banking Systems
In traditional banking, double spending is prevented through centralized control. Banks maintain private ledgers that track account balances in real time. When a transaction is initiated, the bank verifies whether sufficient funds exist and updates the ledger immediately.
For example, when a debit card payment is made, the bank authorizes the transaction, deducts the amount from the account, and ensures the same funds cannot be used again. This centralized verification system eliminates the possibility of spending the same money twice.
Double Spending in Cryptocurrency Systems
Cryptocurrency systems operate without a central authority. Instead of a single institution managing transactions, a distributed network of participants maintains a shared ledger.
Because digital assets are purely data, they can technically be copied or retransmitted. Without a mechanism to validate transactions across the network, a user could attempt to send the same funds to multiple recipients before the network confirms the first transaction.
This is the core challenge that blockchain technology was designed to solve. By using consensus mechanisms and cryptographic validation, blockchain networks ensure that each unit of currency can only be spent once.
How Satoshi Nakamoto Solved the Double Spending Problem
Before Bitcoin, double spending was considered one of the main barriers to creating a decentralized digital currency. Without a trusted intermediary, there was no reliable way for independent participants to agree on which transactions were valid and in what order they occurred.
The Bitcoin Whitepaper and Blockchain Innovation
In 2008, Satoshi Nakamoto introduced Bitcoin and proposed a new approach to solving this problem. The idea was to use a public, distributed ledger known as a blockchain, where transactions are grouped into blocks and validated through network consensus.
Instead of relying on a central authority, the network collectively agrees on the order and validity of transactions. Once a transaction is confirmed and added to the blockchain, it becomes extremely difficult to alter or reverse.
Why This Was a Breakthrough
This approach allowed digital money to function without a central intermediary while still preventing double spending. It introduced a system where trust is established through cryptography and consensus rather than institutional control. This innovation became the foundation for modern blockchain-based cryptocurrencies.
Types of Double Spending Attacks in Cryptocurrency Explained
Double spending attacks refer to techniques used to attempt spending the same digital asset more than once by exploiting timing gaps, consensus rules, or control over network resources. While blockchain systems are designed to prevent such behavior, different attack methods target specific weaknesses in transaction confirmation, network distribution, or validation mechanisms. Understanding these attack types helps clarify how blockchain networks maintain integrity and where potential risks may arise.
51% Attack in Cryptocurrency
A 51% attack occurs when a single entity or coordinated group gains control of more than half of a blockchain’s mining power in Proof-of-Work systems, or a majority of staked tokens in Proof-of-Stake systems. With this level of control, the attacker can influence which transactions are confirmed and how blocks are added to the chain.
In practical terms, the attacker can reorganize recent blocks, exclude certain transactions, and potentially reverse transactions that were previously confirmed. This creates the possibility of double spending by allowing the attacker to invalidate earlier payments while keeping the same funds.
This type of attack is more feasible on smaller or less decentralized networks where total network participation is limited. Larger blockchains with widely distributed participants are significantly more resistant due to the scale of resources required to gain majority control. However, when successful, a 51% attack can disrupt network trust, lead to financial losses, and undermine confidence in the affected blockchain.
Race Attack in Blockchain Transactions
A race attack takes advantage of the time delay between when a transaction is broadcast and when it is confirmed by the network. In this scenario, an attacker sends two conflicting transactions using the same funds almost simultaneously.
One transaction is sent to a merchant or recipient, while the second is directed to an address controlled by the attacker. The attacker attempts to have the second transaction confirmed by the network before the first one is validated.
This method is most effective when merchants accept unconfirmed transactions. If the attacker’s transaction is confirmed first, the original payment becomes invalid, resulting in the recipient not receiving the intended funds. Race attacks rely heavily on network latency and the speed at which transactions propagate across nodes.
Finney Attack and Miner-Based Double Spending
A Finney attack is a more advanced technique that involves a miner who pre-mines a block containing a transaction that sends funds back to themselves. Before broadcasting this block, the attacker initiates a second transaction sending the same funds to a merchant.
If the merchant accepts the transaction before it is confirmed, the attacker can release the pre-mined block to the network. Since the block already contains a conflicting transaction, the network may reject the merchant’s transaction in favor of the attacker’s version.
This type of attack requires access to mining resources and is therefore considered an insider-style threat. It relies on the attacker’s ability to control block production and timing, making it more complex than simpler race-based techniques. The effectiveness of a Finney attack is also influenced by how quickly merchants wait for transaction confirmations before releasing goods or services.
Replace-By-Fee (RBF) Double Spending Attack
Replace-By-Fee (RBF) is a mechanism that allows a sender to replace an unconfirmed transaction with a new one that includes a higher transaction fee. Miners are incentivized to include transactions with higher fees, which can lead to the replacement transaction being confirmed instead of the original.
In a double spending scenario, an attacker first sends a transaction to a merchant using a lower fee. Before it is confirmed, the attacker broadcasts a replacement transaction with a higher fee that redirects the same funds back to themselves. Because miners prioritize the higher fee, the replacement transaction may be confirmed instead of the original.
This approach is particularly relevant in systems where unconfirmed transactions are treated as valid by merchants. It highlights the importance of confirmation delays and fee prioritization in transaction processing. Replace-By-Fee is often discussed in the context of non-custodial wallets and instant payment scenarios where users may not wait for full confirmation before considering a transaction final.
Real-World Double Spending Examples and Case Studies
Real-world double spending incidents demonstrate that the concept is not purely theoretical. While blockchain systems are designed to prevent such occurrences, vulnerabilities in network security, consensus mechanisms, or application layers have been exploited in practice. These case studies highlight how different attack methods operate in live environments and the impact they can have on users, exchanges, and entire networks.
Bitcoin Gold Double Spending Attack (2018)
Bitcoin Gold, a fork of Bitcoin designed to be more accessible to individual miners, experienced one of the most notable double spending incidents in May 2018. Attackers gained majority control of the network’s hashing power, enabling a 51% attack. With this level of control, they were able to reorganize blocks and rewrite parts of the blockchain history.
By creating an alternative version of the chain, the attackers invalidated previously confirmed transactions and redirected funds, effectively spending the same assets multiple times. Reports estimate that approximately $18.6 million worth of BTG was double spent during the attack. The incident exposed the risks associated with networks that have relatively low hash rates and weaker decentralization.
Bitcoin Gold faced another attack in January 2020, resulting in additional losses of around $72,000. This recurrence highlighted how networks with limited mining participation can remain vulnerable over time if security conditions do not improve.
Ethereum Classic Double Spending and 51% Attacks (2019–2020)
Ethereum Classic originated from the 2016 Ethereum split that followed the DAO hack. After the exploit, the Ethereum community was divided over whether to intervene and reverse the theft. A majority supported a hard fork that effectively restored the stolen funds, while a portion of the community rejected this change on the principle that blockchain history should remain immutable. This dissenting group continued operating on the original chain, which became known as Ethereum Classic.
Years later, Ethereum Classic’s relatively smaller Proof-of-Work network made it more susceptible to security risks, particularly 51% attacks. In such scenarios, an attacker with sufficient hash power can reorganize recent blocks, alter transaction history, and enable double spending by replacing confirmed transactions with an alternative chain.
Between 2019 and 2020, Ethereum Classic experienced multiple 51% attacks involving deep chain reorganizations. In one widely reported incident, Coinbase detected reorganizations that included approximately 219,500 ETC, valued at around $1.1 million, which were associated with double spending attempts. In another case, Gate.io reported losses of about $220,000 resulting from similar attack patterns.
These events demonstrated how networks with lower hash rates can face persistent security challenges, even years after their inception. In response, exchanges adjusted their confirmation requirements and deposit policies for Ethereum Classic transactions to mitigate exposure to reorganization risks.
Bitcoin 2013 Chain Split and Double Spending Incident
In March 2013, Bitcoin experienced a significant network disruption caused by a software bug in version 0.8.0 of the Bitcoin client. This bug led to an unintended chain split, where two versions of the blockchain coexisted temporarily.
During this period, some merchants accepted transactions on one version of the chain before the network reached consensus on the valid chain. A notable case involved a merchant receiving a confirmed payment on the 0.8.0 chain. However, miners reverted to the pre-0.8.0 chain by reorganizing the blockchain and invalidating several blocks.
As a result, the original transaction was reversed, and the funds were effectively double spent on the canonical chain. Developers and the mining community responded quickly by coordinating and patching the issue within hours. This incident demonstrated both the risks of software-level vulnerabilities and the ability of a decentralized community to resolve critical issues through coordination.
These case studies illustrate that double spending can manifest in different forms depending on the underlying vulnerability, whether at the consensus layer, network level, or application layer. Together, they reinforce the importance of robust security mechanisms, proper confirmation practices, and continuous monitoring in maintaining the integrity of cryptocurrency systems.
How Blockchain Technology Solves the Double Spending Problem
Blockchain solves the double spending problem by replacing trust in a central authority with distributed consensus and cryptographic verification. Instead of allowing a digital asset to be copied and reused, blockchain networks ensure that every transaction is recorded, validated, and agreed upon by multiple participants before it becomes part of an immutable ledger.
This is achieved through a combination of consensus mechanisms and protocol-level safeguards that make it extremely difficult for any single actor to alter transaction history or spend the same asset twice.
How Proof-of-Work Prevents Double Spending
Proof-of-Work (PoW) secures blockchain networks by requiring participants (miners) to perform computational work before adding new blocks of transactions. This process makes it economically and technically difficult to manipulate the blockchain.
-
Mining and Transaction Validation: In PoW systems, miners compete to solve cryptographic puzzles. The first miner to solve the puzzle earns the right to add a new block to the chain, which includes a batch of verified transactions. Because each block is linked to the previous one, altering any transaction would require re-mining that block and all subsequent blocks, which demands significant computational resources.
-
Economic Disincentives Against Attacks: To successfully carry out a double spending attack, an attacker would need to control a majority of the network’s computational power. Even in that scenario, sustaining such control is extremely costly. This cost structure makes attacks economically irrational, as the resources required to rewrite transaction history would likely outweigh any potential gains.
-
Transaction Confirmations and Finality: Transactions on PoW networks gain security as they receive more confirmations. Each additional block added on top of a transaction increases the difficulty of reversing it. For this reason, many systems wait for multiple confirmations before considering a transaction final, reducing the risk of double spending.
How Proof-of-Stake Prevents Double Spending
Proof-of-Stake (PoS) replaces computational work with financial commitment. Instead of miners, PoS networks rely on validators who stake cryptocurrency to participate in transaction validation.
-
Validator Staking and Participation: Validators must lock up a portion of their assets to gain the right to propose and validate blocks. This stake acts as collateral that aligns their incentives with honest behavior. For example, in networks like Ethereum, validators are required to stake assets to participate in consensus and earn rewards for valid activity.
-
Slashing as a Deterrent Mechanism: If a validator attempts to cheat the system, such as by validating conflicting transactions or enabling double spending, the protocol can penalize them through slashing. Slashing results in the loss of a portion or all of the validator’s staked assets, making fraudulent behavior financially unattractive.
-
Incentive Alignment in PoS Systems: The combination of staking rewards for honest behavior and penalties for malicious activity creates a strong economic framework that discourages double spending attempts and supports network integrity.
Additional Mechanisms That Reinforce Double Spending Protection
Beyond consensus mechanisms, blockchain networks use several technical elements that further strengthen protection against double spending.
-
Nonces and Transaction Uniqueness: Each transaction includes a nonce, a unique identifier that ensures it can only be processed once. This prevents replay attacks and helps maintain the correct order of transactions from a given account.
-
Timestamps and Block Ordering: Blocks include timestamps that help establish the chronological order of transactions. While not perfectly precise, they contribute to maintaining a consistent and verifiable transaction history across the network.
-
Block Confirmations and Network Security: As more blocks are added after a transaction, the difficulty of altering that transaction increases exponentially. This is why confirmations are a critical part of blockchain security.
Merchants and exchanges often rely on a minimum number of confirmations before treating a transaction as final, adding an extra layer of protection against potential double spending attempts.
By combining consensus mechanisms like PoW and PoS with cryptographic rules and confirmation processes, blockchain networks ensure that transaction history remains transparent, tamper-resistant, and economically impractical to manipulate. This layered approach is what effectively eliminates the feasibility of double spending in practice.
Conclusion
Double spending is one of the oldest financial exploits, adapted to the digital era. From counterfeit coins and cheque kiting to modern attempts at reorganizing blockchain history through 51% attacks, the underlying goal has remained the same: spending value that is not truly owned.
What has evolved is the sophistication of both attacks and defenses. Blockchain systems, pioneered by Satoshi Nakamoto, provide a practical and economically robust solution by making double spending prohibitively costly on well-secured networks like Bitcoin. However, the problem is not entirely eliminated. Smaller networks, unconfirmed transactions, cross-chain bridges, and smart contract vulnerabilities still present real risks in 2026 and beyond.
For participants in the crypto ecosystem, understanding these risks is essential. Security depends not only on the protocol but also on how it is used in practice. Waiting for sufficient confirmations, auditing smart contracts, and relying on well-decentralized networks are critical steps. In a trustless environment, informed usage remains the strongest layer of protection.
This article is for informational purposes only and does not constitute financial, investment, or security advice. Cryptocurrency systems involve technical and market risks, and readers should conduct their own research or consult a qualified professional before making decisions.

