Top 10 Cryptocurrency Security Incidents in 2025
2026/04/03 03:28:20
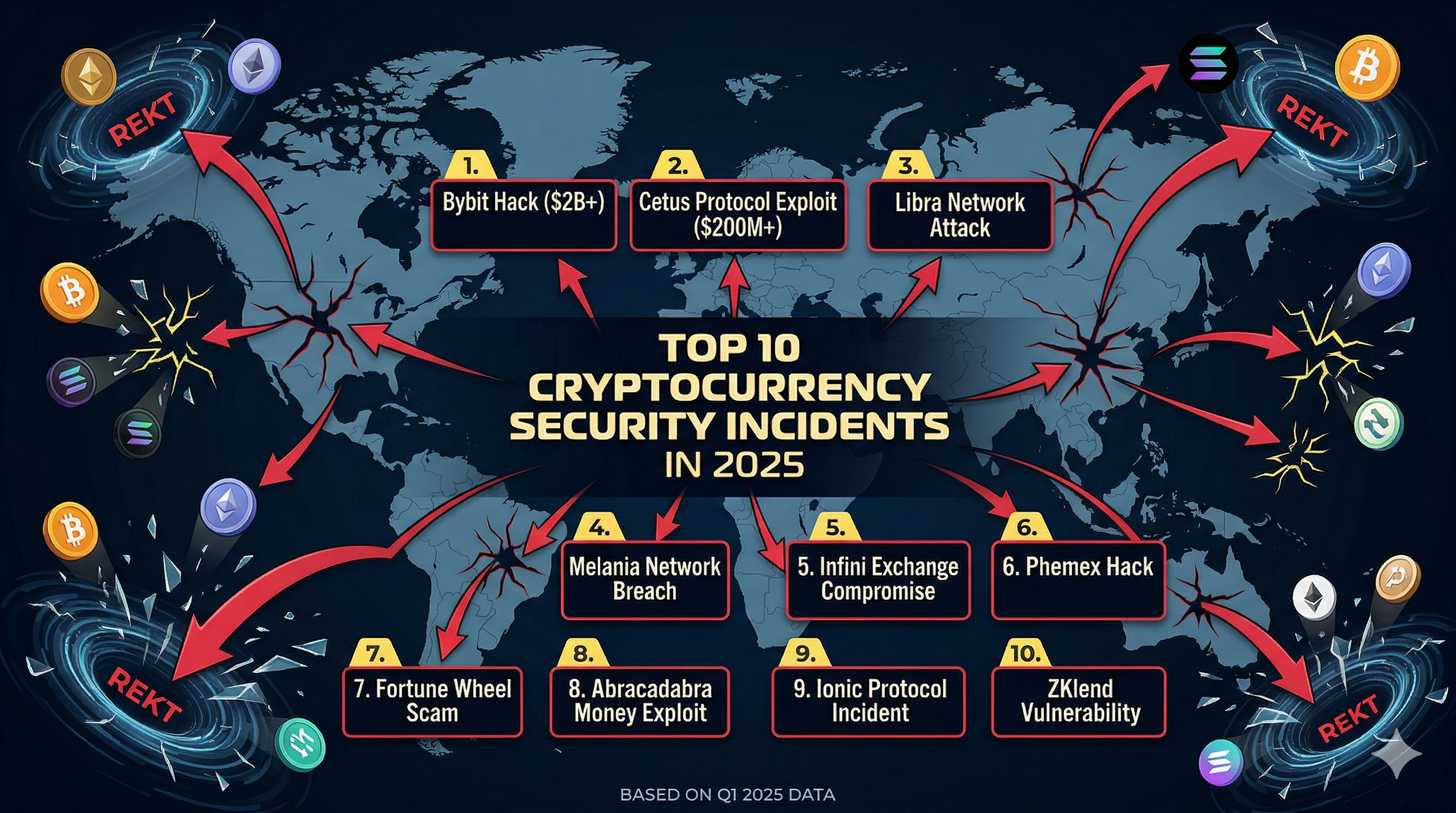
The cryptocurrency industry in 2025 experienced fewer attacks than previous years, but the scale and sophistication of those incidents reached unprecedented levels, revealing a shift from opportunistic hacking to highly strategic, state-backed and technically advanced operations that exposed deep structural weaknesses across exchanges, DeFi protocols, and user security practices.
A Year of Fewer Hacks: but Far Bigger Damage
2025 did not follow the usual pattern of crypto crime. Instead of hundreds of small exploits, the industry saw fewer incidents, but much larger ones. According to blockchain analytics, total stolen funds surged past $3.4 billion, even as the number of attacks declined significantly.
This shift marked a clear evolution in attacker behavior. Hackers moved away from “spray-and-pray” tactics toward carefully planned, high-value operations. Groups spent months infiltrating systems, studying internal workflows, and targeting specific vulnerabilities. In many cases, attackers gained access not through code bugs but through human and operational weaknesses, phishing, impersonation, and compromised infrastructure.
The result was a “quality over quantity” crisis. A single breach could now wipe out more funds than dozens of smaller hacks combined. The industry also saw a surge in wallet compromises and social engineering attacks, affecting tens of thousands of individuals.
Perhaps the most striking trend was the growing role of state-linked actors. Reports indicate that North Korean hacking groups alone were responsible for over $2 billion in stolen crypto during the year, highlighting how digital assets have become part of geopolitical strategy. 2025 ultimately proved that crypto security is no longer just a technical issue, it is a systemic challenge involving infrastructure, human behavior, and global cyber warfare dynamics.
The $1.5 Billion Bybit Hack: The Largest in History
The defining moment of 2025 came in February, when Bybit suffered what is widely considered the largest crypto theft ever recorded. Hackers stole approximately $1.4–$1.5 billion worth of Ethereum from the exchange’s cold wallet infrastructure. What made this breach particularly alarming was not just its size, but how it happened. Attackers did not brute-force their way in. Instead, they exploited a vulnerability in a third-party wallet system and manipulated transaction approvals, effectively tricking authorized signers into approving malicious transfers.
This attack shattered a long-held assumption in crypto, that cold wallets are inherently safe. The incident showed that even offline storage can be compromised if the surrounding infrastructure or user interface is manipulated.
Investigators later linked the attack to the Lazarus Group, a sophisticated hacking collective believed to be backed by North Korea. The scale and precision of the operation suggested months of preparation, including potential infiltration of systems or personnel. Despite the massive loss, Bybit managed to restore liquidity within days, preventing a broader market panic. Still, the damage was done. The hack triggered widespread withdrawals and renewed fears about exchange security across the industry.
Cetus Protocol Exploit: DeFi’s Persistent Weakness
One of the most significant DeFi-related incidents of 2025 involved the Cetus protocol, which suffered losses exceeding $220 million. While smaller than the Bybit breach, this exploit highlighted a recurring issue: smart contract vulnerabilities remain one of the weakest links in decentralized finance. Unlike centralized exchanges, DeFi platforms rely entirely on code. If that code contains flaws, attackers can exploit them instantly and irreversibly. In the case of Cetus, attackers reportedly identified weaknesses in liquidity pool mechanics, allowing them to drain funds in a matter of minutes.
What makes these attacks particularly damaging is their speed. There is no customer support, no rollback mechanism, and often no immediate way to stop the exploit once it begins. Funds can be moved across chains and mixed within hours, making recovery extremely difficult. The Cetus incident also demonstrated how attackers increasingly target protocols with large total value locked (TVL). Rather than chasing small bugs, hackers are now focusing on high-impact vulnerabilities that yield massive payouts. For users, the takeaway was clear: decentralization does not eliminate risk, it changes its nature. Trust is no longer placed in institutions but in code, and that code must be flawless.
The $330 Million “OG Wallet” Heist
Another striking case in 2025 involved a long-dormant Bitcoin wallet, often referred to as an “OG wallet,” which was drained of approximately $330 million in assets.
Unlike exchange hacks, this incident targeted an individual holder, likely someone who had accumulated Bitcoin early and held it for years. The exact method of compromise remains unclear, but analysts suspect a combination of social engineering and private key exposure.
This event underscored a growing reality: large individual holders are becoming prime targets. As blockchain data is public, attackers can identify wallets with significant balances and design tailored attacks to access them. The psychological aspect of such attacks is also important. Long-term holders may feel secure due to years of inactivity, but that complacency can create vulnerabilities. Whether through phishing emails, fake software updates, or compromised devices, attackers exploit moments of trust.
The “OG wallet” hack served as a reminder that crypto security is not just about technology, it is also about personal discipline. Even the most experienced users are not immune if operational security fails.
Balancer V2 Breach and Smart Contract Exploits
The Balancer V2 incident, which resulted in losses exceeding $100 million, further reinforced the risks inherent in DeFi protocols. Balancer, a well-known automated market maker, had undergone multiple audits. Yet attackers still managed to exploit a vulnerability within its system. This highlights a key issue: audits reduce risk, but they do not eliminate it.
Smart contracts are complex, and even minor oversights can have catastrophic consequences. Attackers often study open-source code extensively, searching for edge cases that developers may have overlooked. Once identified, these vulnerabilities can be exploited at scale.
In the case of Balancer, the exploit triggered cascading effects across liquidity pools, amplifying the damage. This kind of systemic vulnerability is particularly dangerous because it can affect multiple assets and users simultaneously. The incident also raised questions about the limits of current security practices. If audited protocols can still be exploited, what level of assurance can users realistically expect? Balancer’s breach did not just result in financial losses, it shook confidence in the broader DeFi ecosystem.
Bitget Incident and Exchange-Level Vulnerabilities
Another notable event involved Bitget, where losses reportedly approached $100 million due to a security breach. While not as large as the Bybit hack, the Bitget incident highlighted that centralized exchanges remain attractive targets. These platforms hold large amounts of user funds, making them high-value targets for attackers.
The breach reportedly involved weaknesses in internal systems rather than direct blockchain exploits. This is a crucial distinction: many of the most damaging attacks occur off-chain, targeting infrastructure, APIs, or employee access points.
In recent years, exchanges have invested heavily in security, including cold storage, multi-signature wallets, and insurance funds. However, attackers continue to find ways around these defenses by targeting human and operational weaknesses.
The Bitget case demonstrated that even well-established platforms are not immune. It also reinforced the importance of transparency, as users increasingly demand clear communication during and after security incidents. For traders, the lesson remains consistent: exchanges are convenient, but they are also centralized points of failure.
From Smart Contract Flaws to State-Backed Exploits: What 2025’s Biggest Crypto Hacks Reveal About Systemic Risk
Data aggregated from DeFiLlama Hacks Dashboard shows that 2025’s largest crypto losses were not random failures, but concentrated around a few recurring weaknesses. Smart contract vulnerabilities remained a major entry point, particularly in DeFi protocols where complex logic and composability increase the risk of overlooked edge cases. However, what stands out is that code-level flaws alone no longer explain the scale of losses. Many of the year’s biggest incidents involved attackers combining technical exploits with deeper system access, targeting governance mechanisms, upgrade keys, or liquidity structures rather than just isolated bugs.
At the same time, the rise of state-linked operations introduced a new layer of risk. Groups associated with geopolitical actors demonstrated capabilities far beyond traditional hackers, including long-term infiltration, supply chain compromise, and coordinated attacks across multiple systems. These actors were not simply exploiting vulnerabilities, they were strategically identifying high-value targets such as centralized exchanges and cross-chain infrastructure, where a single breach could yield hundreds of millions. This shift highlights how crypto has evolved into a domain of financial and political significance, where attacks are increasingly aligned with national interests.
The broader implication is that crypto security must now be viewed as a system-wide challenge. Vulnerabilities no longer exist in isolation, they emerge at the intersection of code, human behavior, and operational infrastructure. As protocols become more interconnected and capital concentration increases, the attack surface expands accordingly. The events of 2025 make it clear that strengthening individual components is not enough; resilience must be built across the entire ecosystem.
The Rise of AI-Powered Crypto Scams
Beyond traditional hacks, 2025 saw an explosion in AI-driven scams. These were not always technical exploits but were equally damaging. Attackers used deepfakes, voice cloning, and automated chat systems to impersonate trusted individuals and organizations. Reports indicate that AI-powered scams generated significantly higher returns than traditional methods, with some operations earning millions per campaign. One of the most alarming trends was impersonation. Victims received messages or calls that appeared to come from colleagues, executives, or even family members. These interactions were often highly convincing, making it difficult to detect fraud.
The use of AI also allowed scammers to scale their operations. Instead of targeting individuals manually, they could automate outreach to thousands of potential victims simultaneously. This shift blurred the line between hacking and social engineering. In many cases, the weakest link was not the system but the user. The rise of AI scams suggests that the future of crypto security will require not only better technology but also greater awareness and education among users.
The $LIBRA Collapse: A Political Crypto Scandal
Not all major incidents in 2025 involved hacking. The $LIBRA token collapse became one of the most controversial events of the year, blending politics, hype, and alleged fraud.
The token gained attention after being promoted by Argentine President Javier Milei, leading to a rapid surge in price. However, the project quickly collapsed, wiping out approximately $251 million in investor funds. The incident has been widely described as a potential rug pull, a scheme where developers inflate a token’s value before withdrawing liquidity and abandoning the project.
What made this case unique was its political dimension. The involvement of a high-profile figure added legitimacy to the project, attracting a large number of retail investors. The fallout sparked investigations and raised questions about accountability in crypto promotions. It also highlighted the risks of hype-driven investments, where narrative can overshadow fundamentals.
The $LIBRA scandal served as a reminder that not all losses in crypto come from hackers, sometimes, they come from misplaced trust.
Conclusion
2025 marked a turning point for cryptocurrency security. The industry did not collapse under constant attack, instead, it faced fewer but far more devastating incidents. From the historic Bybit hack to AI-driven scams and political token collapses, the year revealed a harsh truth: the threat ecosystem is evolving faster than many defenses.
Security is no longer just about protecting code, it is about understanding systems, people, and incentives. As attackers become more strategic, the margin for error continues to shrink. The lessons from 2025 are clear. In crypto, the biggest risks are often invisible until it is too late.
FAQs
-
What was the biggest crypto hack in 2025?
The Bybit hack, with losses of around $1.5 billion, was the largest crypto theft ever recorded.
-
How much crypto was stolen in 2025?
Estimates suggest over $3.4 billion was stolen across hacks and exploits.
-
Who was behind most attacks?
Reports indicate North Korean-linked groups were responsible for a significant portion of stolen funds.
-
Are crypto platforms becoming safer?
Security is improving, but attacks are becoming more sophisticated and targeted.
-
What is the biggest risk today?
Human error and social engineering remain the most common entry points for attackers.
Disclaimer
This content is for informational purposes only and does not constitute investment advice. Cryptocurrency investments carry risk. Please do your own research (DYOR).